- Home
- Cyber Security and SIEM Courses
- CISSP Certification Training
Real-time Use cases
24/7 Lifetime Support
Certification Based Curriculum
Flexible Schedules
One-on-one doubt clearing
Career path guidance
MindMajix’s CISSP training will equip you to design, implement, and manage a best-in-class cybersecurity program. The live training from our top-rated trainers will expose you to a wide array of security practices and principles, boosting your expertise in cybersecurity. Along with the interactive virtual classroom sessions, you will go through power-packed labs, real-time projects, the latest industry use cases, and more. We also provide career path guidance to elevate you as a competent security professional and prepare you for the industry-respected Certified Information Systems Security Professional (CISSP) exam.
Our industry-designed CISSP training course curriculum meets the latest cybersecurity requirements for demanding job roles like security information security officer, systems engineer, security architect, and more.
What is CISSP?
CISSP Objectives
CISSP Domains
Benefits of CISSP
CISSP Certification Requirements
Confidentiality, integrity and availability
Security governance principles
Legal and regulatory Issues
Business continuity requirements
Policies, standards, procedures, and guidelines
Risk management concepts
Threat modeling
Types of Intellectual Property (IP) Law
Introduction to Risk Analysis
Importance of Business Continuity Planning
Aligning security and risk to organizational objectives
Evaluate and apply security governance principles
Implement policies, standards and procedures
Applying compliance
Applying risk management concepts
Assessing threats and vulnerabilities
Performing risk analysis and control
Defining qualitative and quantitative analysis
Preserving the business
Adhering to Business Continuity Management Code of Practice and Specifications
Performing a business impact analysis
Asset Security
Data classification
Data Quality Assurance and Quality Control
Limitation on collection of sensitive data
Media Resource Protection
Data Remanence
Equipment Lifecycle
Standards Selection Critical Security Control
Examining security models and frameworks
The Information Security Triad and multi-level models
Investigating industry standards: ISO 27001/27002
Evaluating security model fundamental concepts
Exploring system and component security concepts
Certification and accreditation criteria and models
Reviewing mobile system/cloud/IoT vulnerabilities
Protecting information by applying cryptography
Detailing symmetric and asymmetric encryption systems
Ensuring message integrity through hashing
Uncovering threats to cryptographic systems
Security Engineering
Secure design principles
Controls and countermeasures
Virtualization
Trusted platform module
Mainframes and Other Thin Client Systems
Database security
Cloud Computing
Multilevel Security Models
Information Technology Security Evaluation Criteria
The Internet of Things
DES Operation Modes Electronic Code Book
Cryptography Methods Transposition Ciphe
Network architecture
OSI model
TCP/IP
Mutilayer protocols
Storage protocols
Voiceover IP
Software-defined networks
Content distribution networks
Remote meeting technology
Telecommuting
Remote access and VPN
Host-to-Host Layer and Application Layer
Types of IP Addressing
Flavors of LAN transmission methods
IEEE Wireless Standards and Spread-Spectrum Technologies
Physical and logical access
Multi-factor authentication
SSO Technologies
Accountability
Types of Biometrics
Session management
Credential management
Third-party identity services
Types of Access Control Administration
Unauthorized Disclosure of Information
Identification Authentication and Authorization
Security Assessment
Assessment and test strategies
Security control testing
Security testing strategies
Risk Evaluation and Control
Internal and third-party audits
Reasons to Use Synthetic Transactions
Code Review and Testing
Common Software Vulnerabilities
Leveraging the role of testing and auditing to analyze the effectiveness of security controls
Differentiating detection and protection systems
Security Operations
Investigations
Operational, criminal, civil, and regulatory investigations
Operating and Maintaining Preventive Measures
Logging and Monitoring Activities
Provisioning
Threats to Operations
Security Measurements, Metrics, and Reporting
Incident management
Forensic Investigation Guidelines
Honeypots and honeynets
Vulnerability management
Change management processes
Recovery strategies
Disaster recovery processes
Cloud and Virtual Storage Security Issues
Our CISSP Certification Training course aims to deliver quality training that covers solid fundamental knowledge on core concepts with a practical approach. Such exposure to the current industry use-cases and scenarios will help learners scale up their skills and perform real-time projects with the best practices.
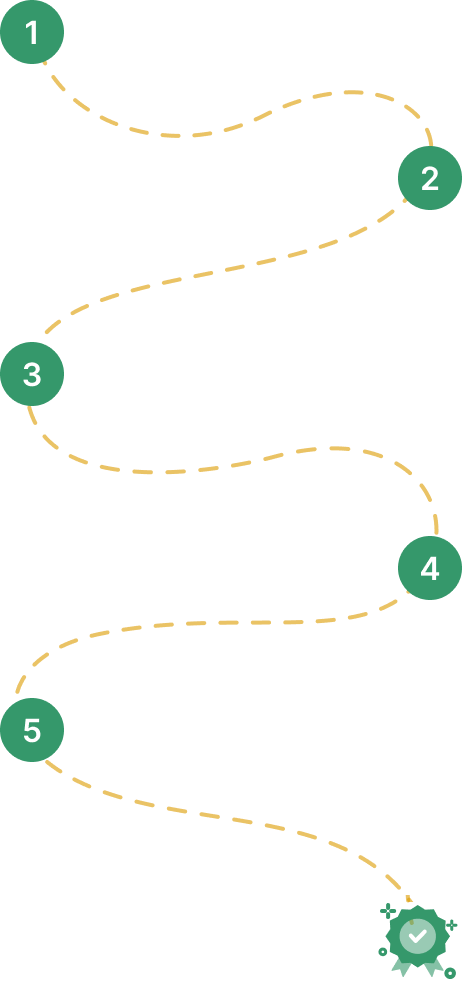
Both options cover the full curriculum and include most of the certification topics
Learn anytime, at your own pace — complete the course in weeks or months.
20% Off
11,200
Rs 14,000
Get Full Access
Real-time classes with a certified expert — ask questions, get instant feedback, and walk away job-ready
07:30 AM IST · Weekend · Only 4 seats left
20% Off
28,000
Rs 35,000
Empower your team with new skills to Enhance their performance and productivity.

We believe in transparency. Here's how MindMajix stacks up against typical CISSP Certification training providers so you can compare value, support, and practical depth clearly.
CISSP Certification Training
Generic CISSP Certification Training Providers
Updated to the latest exam pattern with real-world modules, guided labs, and implementation depth.
Always currentOften outdated basics with limited real-world coverage and shallow practical context.
Frequently outdatedSandbox-style practice with guided exercises, projects, and replay-friendly learning support included.
Included at no extra costSlides-first teaching with restricted lab time or paid add-on practical access.
Limited / paid extraCertified trainers with real implementation experience and structured teaching support.
Verified expertiseTrainer quality varies widely and may depend on availability rather than specialization.
Varies widelyA stable trainer journey with consistent delivery, doubt support, and batch continuity.
Consistent trainerTrainer substitutions can happen mid-course and interrupt learning continuity.
Frequent changesOngoing help through trainer sessions, community support, and guided clarification after class.
Extended supportSupport often stops after sessions, leaving little structured post-class help.
No post-training helpResume reviews, mock interviews, hiring guidance, and practical interview preparation support.
Active placement supportPlacement support is often limited to generic guidance or an email list.
Mostly nominalStructured mock interview rounds with domain-focused feedback before interviews.
IncludedStudents are usually expected to prepare independently without guided mock rounds.
Not includedWeekday, weekend, and flexible learning paths with guidance on the best fit.
Fully flexibleFixed schedules with fewer alternatives once a batch begins.
Limited optionsPractice questions, revision guidance, and exam-focused preparation aligned to current objectives.
Comprehensive prepGeneric question banks that may not reflect the latest exam priorities.
Outdated mock testsStrong value with training, support, and practical learning included as a single package.
Best value for inclusionsLower headline pricing can still lead to add-on costs for labs, support, or extras.
Hidden add-on costsLong-term access to recordings and study materials for revision after batch completion.
Lifetime-style accessAccess is often time-limited and may not include refreshed supporting material.
Time-limited accessUpdated to the latest exam pattern with real-world modules, guided labs, and implementation depth.
Always currentOften outdated basics with limited real-world coverage and shallow practical context.
Frequently outdatedIndustry-focused delivery with stronger support, consistency, and practical learning value.
Lower upfront pricing can hide trade-offs in labs, trainer continuity, and support quality.
Student
Student
Student
Lead - Salesforce Cloud, D&IT
Senior Technical Manager
Global Head of Infra, Security and Networks,
Business Analyst at American Red Cross, Culpeper, Virginia, United States
IT Business Systems Analyst, Sales Applications • CX GTM Global Program Manager - WomenConnect
Team Leader - DB Admin

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs: