- Home
- Cyber Security and SIEM Courses
- CyberArk Training
Real-time Use cases
24/7 Lifetime Support
Certification Based Curriculum
Flexible Schedules
One-on-one doubt clearing
Career path guidance
Our CyberArk course provides you with the expertise to build, deploy, and configure Privileged Access Management (PAM) solutions using Cyberark. You will gain hands-on skills in managing various CyberArk components, creating and implementing CyberArk policies, and performing CyberArk troubleshooting.
The advanced course equips you to handle multiple cyberark tools, including Vault, PVWA, CPM, PTA, and PSM. The training includes intensive hands-on labs, real-time projects, and industry examples to enhance your practical skills in the CyberArk platform.
At the end of the CyberArk training, you will become a skilled IT security professional.
| Course Duration |
|
| Lab Environment | Our trainers will guide you through setting up the free trial CyberArk tools for hands-on practice. |
| Post-Training Support |
|
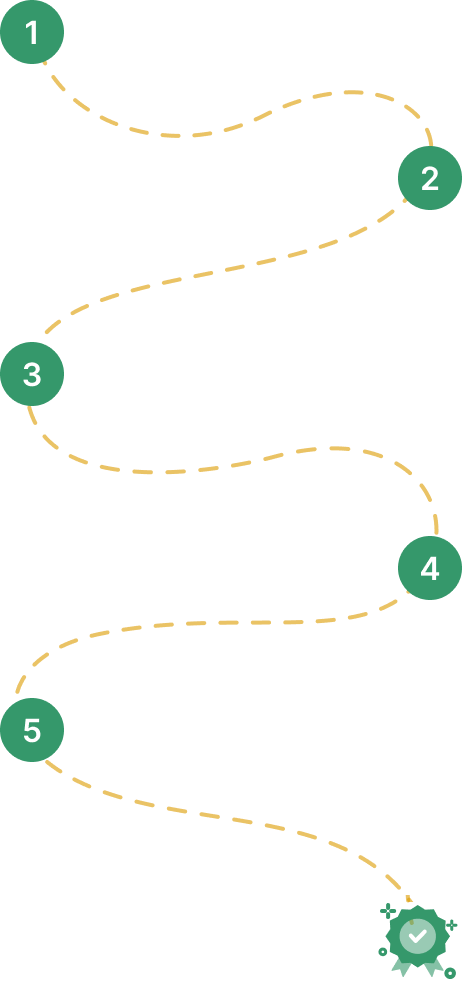
From PAM basics to Identity Security architect - a structured 5- stage progression built for the global cybersecurity market.
Entry-level understanding of Privileged Access Management
PAM Administrator / Security Analyst
PAM Engineer / Implementation Specialist
Enterprise Architect / Senior Consultant
Elite DBA / CyberArk Consultant / Enterprise Architect
MindMajix covers Stages 1-4 in comprehensive structured programming - Online & Self-Paced available.
*CDE certification requires active CyberArk partner status | Salary ranges based on 2025-2026 market data.
No IT degree needed. Whether you're starting your cybersecurity journey or advancing from IT professional to PAM specialist — MindMajix has a structured path for you.
MindMajix’s CyberArk course curriculum covers the key learning modules that will enhance your IAM/PAM expertise. You will be equipped to deliver identity security projects efficiently in real-world environments. The course content aligns with CyberArk version 14.6 and covers the latest PAM features.
Privileged identity management gives complete security and audit control for enterprises. This module will explain how to secure, monitor, and protect privileged accounts in enterprise environments.
This section highlights the core properties and capabilities of the CyberArk solution. Additionally, it explains CyberArk installation and configuration through hands-on practice.
This section provides real-time knowledge needed to design, install, and configure the CyberArk Privileged Account Security Solution. You’ll also learn to install CyberArk components through step-by-step exercises.
This module presents an in-depth look at CyberArk functioning with real-time examples and practices.
This section explains the recommended software and hardware specifications of the servers for CyberArk infrastructure installation.
CyberArk policy offers a centralized overview of the security and compliance policy of privileged accounts. In this section, you’ll gain complete real-time knowledge of configuring CyberArk policy by best practices.
This section will walk you through the fundamentals of creating a CyberArk policy and its services.
In this module, you’ll learn how to create and configure Safe in CyberArk for integration. Also, you’ll master the concepts of matrix approach for account ranking and prioritization, user management using LDAP, dual control configuration, and object-level access control management.
In this module, you’ll learn to integrate CyberArk for Windows and Unix/Linux platforms. You’ll also expand knowledge on network devices and security devices through the best practices.
Windows
Unix/Linux
Network Device Overview
Security Device Overview.
This section highlights the main characteristics of CyberArk use cases.
4+ More lessons
Our CyberArk Training course aims to deliver quality training that covers solid fundamental knowledge on core concepts with a practical approach. Such exposure to the current industry use-cases and scenarios will help learners scale up their skills and perform real-time projects with the best practices.
Course Completion Certificate:
MindMajix offers a CyberArk course completion certificate after you complete all quizzes and assessments conducted in the training.
CyberArk Certifications:
Our CyberArk course curriculum modules align with various CyberArk certification exam topics, as shown in the table below. It ensures that you gain the required knowledge and confidence to pass the certifications on your first attempt.
| Certification Exam | Exam Topics | MindMajix Course Modules |
| Cyberark Defender – PAM (PAM – DEF) | Core Components | Cyberark Solution Components |
| Installation and Platform Readiness | Cyberark Infrastructure Installation | |
| Policies and Platforms |
|
|
| Safe Management and Permissions | Cyberark Safe Management | |
| Account Onboarding and Platforms | Cyberark Account Integration | |
| Session Management and Recording | Cyberark Use Cases | |
| Password Rotation and Reconciliation |
|
|
| Directory/LDAP Integration |
|
|
| Monitoring, Auditing, and Reporting | Cyberark Use Cases | |
| Backup, Maintenance, and Troubleshooting |
|
|
| Cyberark Sentry – PAM (PAM – SEN) |
PAM Deployment Planning and Prerequisites | Cyberark Infrastructure Installation |
|
Cyberark Infrastructure Installation | |
| Directory Integration and Initial Access Model |
|
|
| Design and Cutover Validation | Cyberark DR Overview | |
| Basic Verification: Rotation, Reconciliation, Session Launch and Recording | Cyberark Use Cases |
Sources: Cyberark Certifications

Learn from the certified and real time working professionals.

Krithik , having 8+ yrs of experience
Specialized in:Specialized in Cyberark PAM, SCCD, Power BI, LDAP, Powershell Scripting
With 8+ years of experience in the IT industry, Krithik is one of MindMajix's best Cyberark-certified freelance trainers. He has substantial experience building CyberArk safes and adding different applications/portfolios, PAM solutions using CyberArk, network security, and administration and can deliver the best Cyberark training to our learners.
Both options cover the full curriculum and include most of the certification topics
Learn anytime, at your own pace — complete the course in weeks or months.
20% Off
12,800
Rs 16,000
Get Full Access
Real-time classes with a certified expert — ask questions, get instant feedback, and walk away job-ready
07:30 AM IST · Weekend · Only 4 seats left
20% Off
25,600
Rs 32,000
Empower your team with new skills to Enhance their performance and productivity.

We believe in transparency. Here's how MindMajix stacks up against typical CyberArk training providers so you can compare value, support, and practical depth clearly.
CyberArk Training
Generic CyberArk Training Providers
Updated to the latest CyberArk PAM (Defender + Sentry) — Vault, PVWA, CPM, PSM, PSMP, AAM/CCP & EPM all covered.
Current syllabusOften outdated versions — typically covers basic Vault & PVWA only, with limited core components.
Frequently outdated60+ days of cloud lab access with 40+ real-world PAM exercises — Vault install, safe management & account onboarding.
Included, no extra costMostly slides-based teaching with limited lab time, or labs are charged separately.
Limited / paid extraCyberArk Certified Defender + Sentry trainers with 8–12 yrs of live PAM project experience at MNCs.
Certified trainersTrainers may not hold active CyberArk certifications — often freelancers with varying skill.
UnverifiedA stable trainer journey with consistent delivery, doubt support, and batch continuity.
Consistent trainerTrainer substitutions can happen mid-course and interrupt learning continuity.
Frequent changes24/7 learner community + 1-on-1 doubt sessions, with support extended up to 6 months post-course.
Lifetime doubt supportSupport typically ends the moment the course completes — no post-training help.
No post-course helpResume reviews, mock interviews, hiring guidance, and practical interview preparation support.
Active placement supportPlacement support is often limited to generic guidance or an email list.
Mostly nominalStructured mock interview rounds with domain-focused feedback before interviews.
IncludedStudents are usually expected to prepare independently without guided mock rounds.
Not includedWeekday, Weekend, Fast-Track & Self-Paced options — reschedule a batch any time, free.
Flexible batchesFixed batch schedules — miss a class and there are no recordings to fall back on.
Rigid timingPractice questions, revision guidance, and exam-focused preparation aligned to current objectives.
Comprehensive prepGeneric question banks that may not reflect the latest exam priorities.
Outdated mock testsStrong value with training, support, and practical learning included as a single package.
Best value for inclusionsLower headline pricing can still lead to add-on costs for labs, support, or extras.
Hidden add-on costsLong-term access to recordings and study materials for revision after batch completion.
Lifetime-style accessAccess is often time-limited and may not include refreshed supporting material.
Time-limited accessUpdated to the latest CyberArk PAM (Defender + Sentry) — Vault, PVWA, CPM, PSM, PSMP, AAM/CCP & EPM all covered.
Current syllabusOften outdated versions — typically covers basic Vault & PVWA only, with limited core components.
Frequently outdated60+ days of cloud lab access with 40+ real-world PAM exercises — Vault install, safe management & account onboarding.
Included, no extra costMostly slides-based teaching with limited lab time, or labs are charged separately.
Limited / paid extraCyberArk Certified Defender + Sentry trainers with 8–12 yrs of live PAM project experience at MNCs.
Certified trainersTrainers may not hold active CyberArk certifications — often freelancers with varying skill.
UnverifiedA stable trainer journey with consistent delivery, doubt support, and batch continuity.
Consistent trainerTrainer substitutions can happen mid-course and interrupt learning continuity.
Frequent changes24/7 learner community + 1-on-1 doubt sessions, with support extended up to 6 months post-course.
Lifetime doubt supportSupport typically ends the moment the course completes — no post-training help.
No post-course helpResume reviews, mock interviews, hiring guidance, and practical interview preparation support.
Active placement supportPlacement support is often limited to generic guidance or an email list.
Mostly nominalStructured mock interview rounds with domain-focused feedback before interviews.
IncludedStudents are usually expected to prepare independently without guided mock rounds.
Not includedWeekday, Weekend, Fast-Track & Self-Paced options — reschedule a batch any time, free.
Flexible batchesFixed batch schedules — miss a class and there are no recordings to fall back on.
Rigid timingPractice questions, revision guidance, and exam-focused preparation aligned to current objectives.
Comprehensive prepGeneric question banks that may not reflect the latest exam priorities.
Outdated mock testsStrong value with training, support, and practical learning included as a single package.
Best value for inclusionsLower headline pricing can still lead to add-on costs for labs, support, or extras.
Hidden add-on costsLong-term access to recordings and study materials for revision after batch completion.
Lifetime-style accessAccess is often time-limited and may not include refreshed supporting material.
Time-limited accessIndustry-focused delivery with stronger support, consistency, and practical learning value.
Lower upfront pricing can hide trade-offs in labs, trainer continuity, and support quality.
They gave me an understanding of Cyberark. SInce I already have a background in Identity and Access Management it was easier for me to pickup the material and understand it. They gave me enough understanding that I can go on my own and investigate further.
USA
I took Cyberark training from Mindmajix technologies and it was very helpful. Each and every topic was started from scratch. Also, there was lab sessions on how password management works and other topics.
Bangalore
I recently took an online course "CyberArk" and I was very impressed with my experience it took longer than I expected. The course was well-organized and provided a comprehensive overview of the subject matter. The instructor was knowledgeable and responded promptly to any questions I had. Overall, I feel like I gained a lot from this course and would highly recommend it to anyone looking to learn about this subject. Thank you for this great learning opportunity.
USA
Lead - Salesforce Cloud, D&IT
Senior Technical Manager
Global Head of Infra, Security and Networks,
Business Analyst at American Red Cross, Culpeper, Virginia, United States
IT Business Systems Analyst, Sales Applications • CX GTM Global Program Manager - WomenConnect
Team Leader - DB Admin

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs:
To meet the learning needs of people spread across various geographical locations, we are offering our high-quality training services at the location of your choice to ensure you obtain maximum impact for your training investment. Choose your city below.
