Boston Institute of Analytics reports that cybersecurity is among the most reliable and stable careers. It highlights that professionals who learn and build their cybersecurity skills are in a safer position.
Among many cybersecurity tools, CyberArk is one of the major players in identity security. According to TheirStack, companies such as KPMG, EY, Capgemini, Accenture, PwC, and Infosys leverage CyberArk professionals to protect their resources from cyber threats.
MindMajix offers CyberArk Interview Questions with answers to help learners deepen their knowledge of CyberArk and build careers in cybersecurity.
Table of Contents
- Skills Required for CyberArk Professionals
- Job Responsibilities of CyberArk Professionals
- CyberArk Interview Questions
- CyberArk Interview Preparation Tips
- Frequently Asked Questions
Skills Required for CyberArk Professionals
Understanding the skills required of CyberArk professionals will make your interview preparation more effective.
- Hard Skills:
- Expertise in identity and access management (IAM) concepts
- Sound troubleshooting capabilities
- Strong knowledge of privileged access best practices
- Proficient with CyberArk Privileged Access Management (PAM) suite
- Good exposure to Windows and Linux operating systems, databases, middleware, and APIs
- Soft Skills:
- Strong analytical thinking
- Attention to detail
- Effective communication
Job Responsibilities of CyberArk Professionals
Knowing the job responsibilities of CyberArk professionals helps you anticipate employers' expectations and prepare for interviews accordingly.
- Entry-level:
- Installing CyberArk components such as PVWA, PSM, CPM, and Vault
- Configuring PSM recording and session monitoring
- Maintaining the application layer of CyberArk solutions
- Developing policies for risk, audits, and IT security activities
- Monitoring and maintaining privileged access controls
- Onboarding accounts and applications into the CyberArk platform
- Generating audit reports as well as updating documents regularly
- Performing periodic system health checks and taking proactive measures
- Working with SMEs to install new CyberArk modules
- Senior-level:
- Designing and orchestrating scalable, robust CyberArk solutions
- Planning CyberArk integrations across cloud, on-premises, and hybrid environments
- Developing privileged access governance and performing privileged access risk analysis
- Working with teams to implement relevant policies and meet compliance requirements
- Implementing major upgrades, enterprise deployments, MFA, and strong authentication
- Preparing implementation roadmaps and managing enterprise-level migrations
- Implementing best practices and mentoring teams to use CyberArk effectively
| If you want to enrich your career and become a professional in CyberArk, then enroll in "CyberArk Training". This course will help you to achieve excellence in this domain. |
Top Frequently Asked CyberArk Interview Questions
- Define a privileged user?
- What do you understand by PrivateArk Client?
- What is PrivateArk Vault Command Line Interface?
- What is a Privileged Session Manager SSH Proxy (PSMP)?
- What do we mean by Penetration Test
- Which Component is used on all Cyberark solutions?
- What do you understand by SSH Key Manager?
- Can CyberArk Vault be managed manually?
CyberArk Interview Questions for Beginners
In this section, we will go through basic interview questions and answers to help you build a strong foundation in CyberArk concepts.
1) What is CyberArk?
Ans: CyberArk is a popular privileged access management (PAM) solution that helps secure and manage privileged accounts and credentials.
Organizations adopt the CyberArk platform to prevent cyberattacks by controlling access to sensitive data, systems, and applications.
2) What is the latest version of CyberArk?
Ans. As of January 2026, CyberArk 15.0 is the latest version of CyberArk, a privileged access management self-hosted platform.
3) What are the key products of CyberArk?
Ans: The image below shows some of the key features of CyberArk.

4) What are the main components of CyberArk PAM?
Ans: Below are the main components of CyberArk PAM.
- Digital Vault
- PVWA
- Central Policy Manager
- Privileged Session Manager
- Privileged Session Manager For SSH
- On-Demand Privileges Manager
- SSH Key Manager
- CyberArk Vault Synchronizer
5) What are the key enhancements included in the CyberArk version 15.0?
Ans:
| CyberArk Components | Key Enhancements |
| Vault Remote Manager | Simplified remote control and monitoring for disaster recovery |
| Enhanced SNMP V3.0 monitoring with TLS 1.3 encryption | |
| Ensured continuous directory authentication | |
| Password Vault Web Access | Enhanced PVWA reporting experience |
| Secure REST API authorization with OAuth2. | |
| Platform management – platform name modification | |
| Central Policy Manager | Introduction of 64-bit architecture support in CPM |
| Privileged Session Manager | UPN support for Linux target logins via PSM |
| SSH key authentication support in PSM-WinSCP | |
| Privileged Session Manager for SSH | Expanded Ubuntu support |
| Streamlined session initiation with default logon account |
6) Why Choose the CyberArk Privileged Access Security Solution?
Ans:
- CyberArk provides complete protection for privileged accounts against advanced and insider attacks, mitigating risks.
- It plays a key role in meeting high compliance management standards.
- Organizations with large-scale on-premises and cloud environments use the CyberArk security solution to address privileged account security challenges.
- CyberArk offers robust session security, least privilege and application control, and continuous monitoring to rapidly detect threats and report on suspicious privileged account activities.
7) What are the key capabilities of CyberArk’s CORA AI?
Ans:
- CORA AI chatbot enables users to access CyberArk’s services using natural language processing (NLP). It allows users to post queries, run commands, retrieve crucial information, and easily maintain their systems.
- CORA AI provides users with helpful insights and recommendations. For example, it helps discover the accounts that are no longer required.
8) What is CyberArk Enterprise Password Vault?
Ans: CyberArk Enterprise Password Vault is an element of the CyberArk Privileged Account Security Solution. It is designed to discover, secure, rotate, and control access to confidential account passwords used to access systems across an organization’s IT environment.
The image below depicts the use of CyberArk EPV.
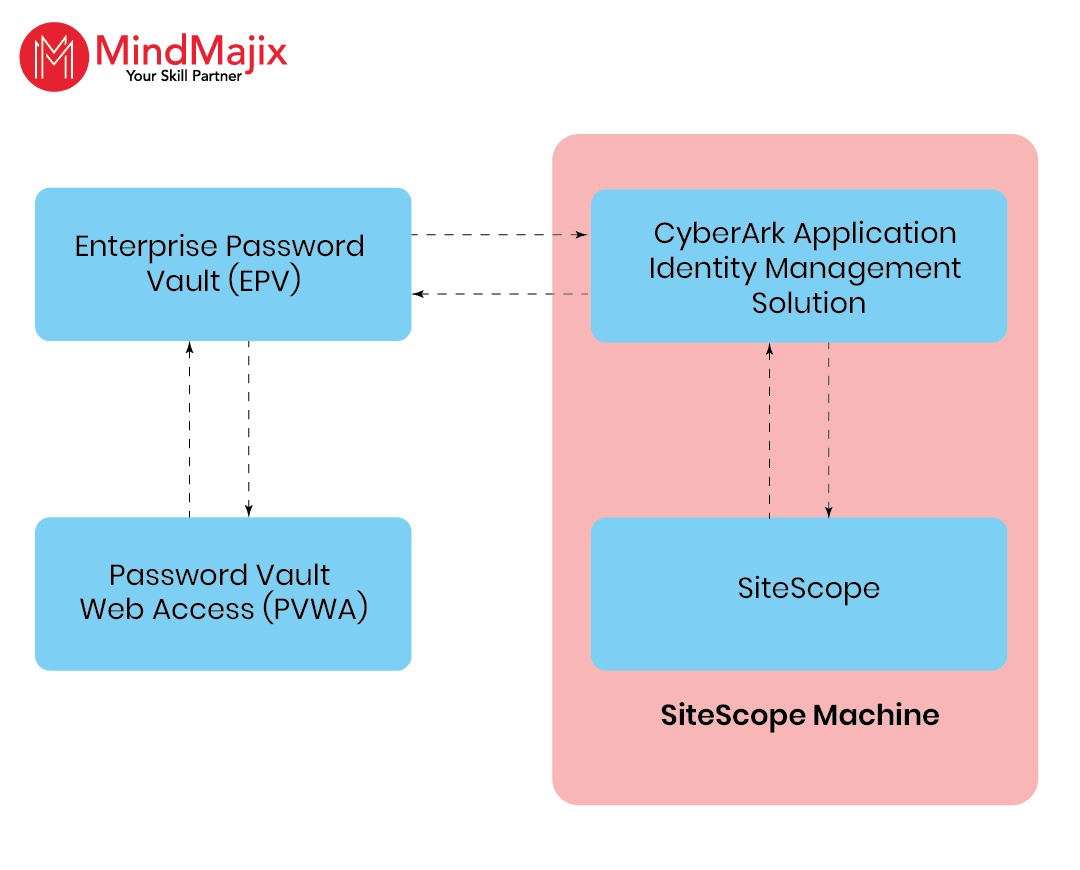
9) How does CyberArk’s Enterprise Password Vault (EPV) work?
Ans: CyberArk’s Enterprise Password Vault (EPV) is also known as Digital Vault. It uses multiple layers of encryption to provide maximum security to files stored in safes.
This is how CyberArk’s EPV works.
- Each file in a safe is encrypted with a unique key.
- The keys are then stored within the vault. They are encrypted with a unique vault encryption key.
- All of these keys are delivered only to users with the required access rights.
- Administrators classify access to safes and the data within them.
- Users must be manually approved by a Safe Supervisor before they can access safes.
10) What do you understand about CyberArk Viewfinity?
Ans: CyberArk Viewfinity is now available as CyberArk Endpoint Privilege Manager. It equips organizations to implement least-privilege policies for business and system administrators.
This reduces the attack surface, minimizes accidental or intentional damage to endpoints and servers. It also segregates administrative duties on Servers.
Complementary application controls prevent malicious applications from infiltrating the environment while allowing unknown applications to run in a safe mode.
11) What do you understand about privileged security in CyberArk?
Ans: CyberArk’s privileged access helps control identities, infrastructure, and applications end-to-end. It enables us to conduct identity-focused audits and meet compliance requirements.
12) Define a privileged user.
Ans: A privileged user is a user of a system, data, or application who has been granted more control than the majority of users.
Here are a few crucial things about privileged users.
- Privileged users can be cloud server managers, system administrators, and database administrators.
- Some applications that use privileged accounts to communicate with other applications, scripts, databases, web services, and more.
- These accounts are often ignored and exposed to significant risk because their credentials are hardcoded and static.
- Hackers can easily access these attack points to escalate their privileged access throughout the organization.
13) What do you understand about Privileged Access Management (PAM)?
Ans: Here are a few key aspects of PAM:
- PAM helps to protect superuser accounts in an organization's IT environments.
- It helps organizations to secure their IT infrastructure and applications.
- Organizations can run their businesses efficiently and protect their sensitive data so that no one, internal or external to the organization, misuses it.
14) How many times can the incorrect Password count be increased in CyberArk?
Ans: The incorrect password count can be increased by up to 99. This approach helps balance usability and security by preventing brute-force attacks and controlling account access.
15) What is required for a specific user to access a specific safe?
Ans: A specific user must have the relevant ‘safe permissions’ to access a specific safe in CyberArk.
16) What is the password complexity required in CyberArk authentication using the internal CyberArk scheme?
Ans: The following are the mandatory requirements to generate a password in CyberArk’s internal authentication scheme.
- At least one minimum lowercase alphabet character
- At least one uppercase alphabet character
- At least one numeric character
You need to meet additional complexity requirements, such as minimum length and the inclusion of special characters, per your organisation's security policies.
17) What do you understand about PrivateArk Client?
Ans: The PrivateArk Client is a standard Windows-based administrative client for managing the CyberArk PAM solution.
By using the PrivateArk client, we can:
- Deploy the client on multiple remote computers
- Access the Enterprise Password Vault through LAN or WAN
- Create and manage safes
- Define vault hierarchy and permissions
Importantly, access to the Enterprise Password Vault via the PrivateArk Client requires that the Digital Vault validate users.
18) What is the PrivateArk Vault Command Line Interface?
Ans: The PrivateArk Vault Command Line Interface (PACLI) enables administrators to access and interact with the CyberArk vault from any location using command-line scripts.
It automatically manages vault operations, including safe creation, account management, and auditing.
19) What are the CyberArk Vault protection layers?
Ans: The CyberArk Vault Protection layers include:
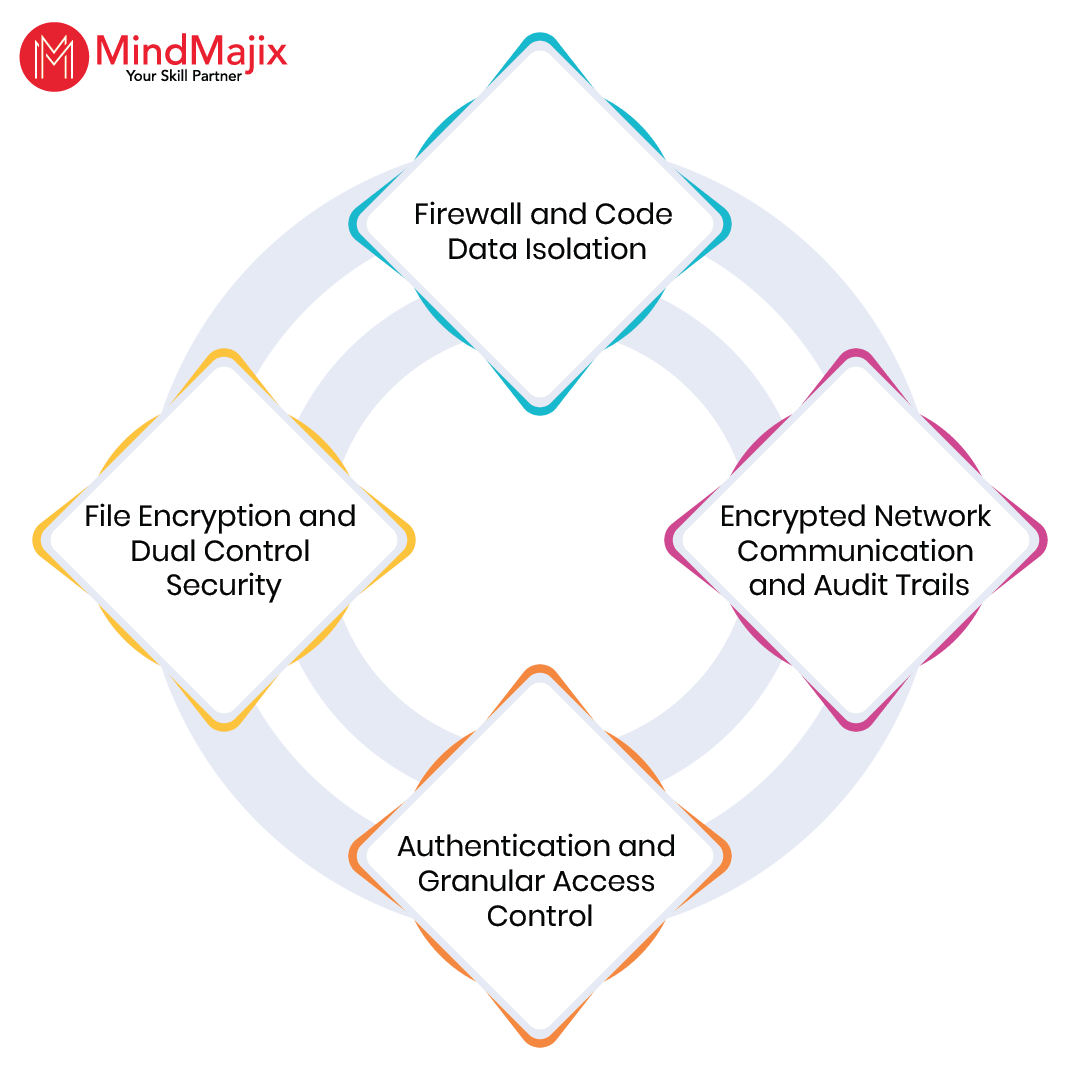
- Firewall and Code Data Isolation – It prevents unauthorized access to vault components.
- Encrypted Network Communication and Audit Trails – It ensures secure data transmission and activity tracking.
- Authentication and Granular Access Control – It enforces strict user verification and role-based permissions.
- File Encryption and Dual Control Security – It protects stored credentials and requires multiple approvals for sensitive account activities.
20) What is Password Vault Web Access (PVWA) Interface?
Ans: The PVWA is a fully-featured web-based interface that provides centralized control for managing privileged accounts.
By using this interface, you can:
- Request, access, and manage privileged account credentials
- Approve access requests
- Monitor and audit privileged access activities
- View dashboards and reports, and gain helpful insights
21) What is a Privileged Session Manager SSH Proxy (PSMP)?
Ans: The PSMP is a Linux-based CyberArk component that acts as a proxy for SSH-enabled devices.
Let’s see the key advantages of PSMP:
- PSMP controls access to privileged sessions and initiates SSH connections to remote devices on a user's behalf without requiring SSH credentials.
- PSMP records text-based sessions, stores them in the EPV, and enables authorized auditors to review them.
- It supports single sign-on capabilities, allowing users to connect to target devices without exposing the privileged connection password.
22) What is Central Policy Manager (CPM)?
Ans: The Central Policy Manager automatically imposes the organizational security policy by routinely changing passwords on remote machines. It stores new passwords in the Enterprise Password Vault, without any human interaction.
The diagram below shows how the CyberArk central policy manager works.
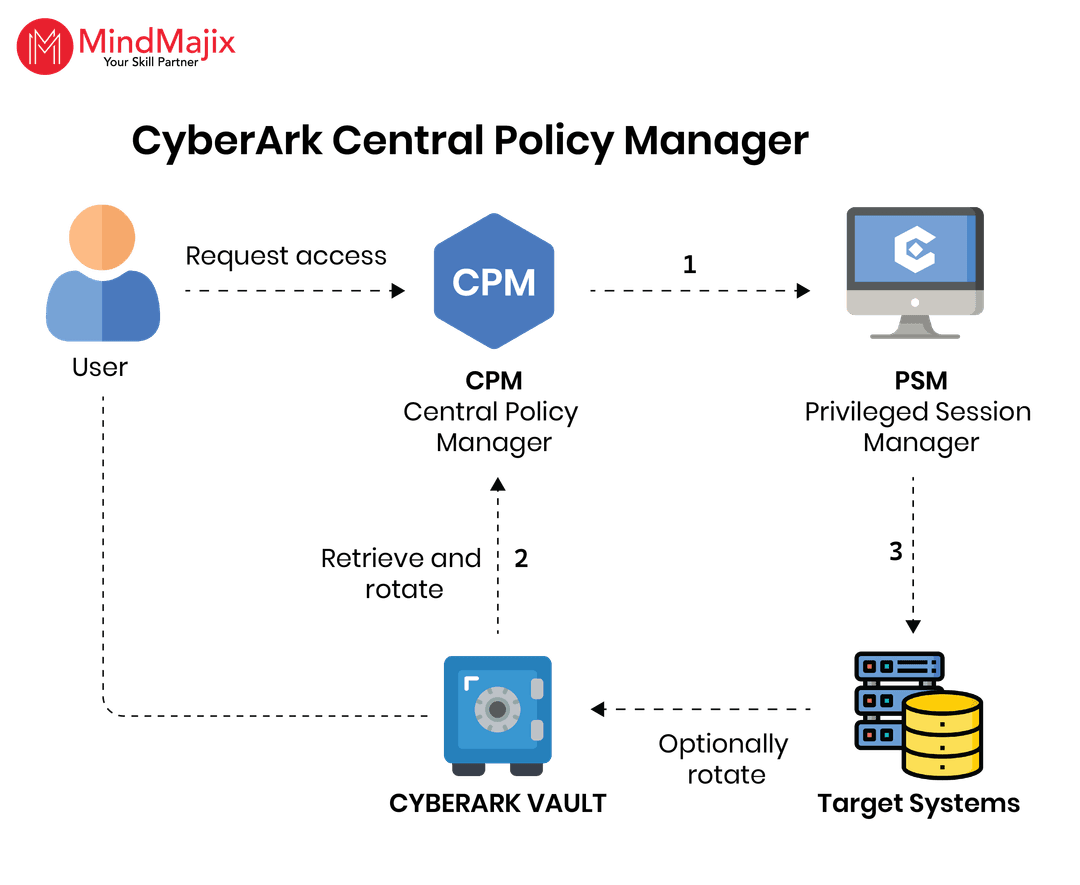
Let’s dig deeper into CyberArk’s CPM.
- The CPM helps generate new random passwords and replaces existing passwords on remote machines.
- Passwords generated by the CPM comply with the organisation's Master Policy.
- It supports storing new passwords in the Enterprise Password Vault.
- Administrators will be notified via the PVWA when passwords will expire and when those that do not meet the Master Policy criteria will expire.
- Administrators can implement a one-time password (OTP) policy using the CPM.
| Looking for Best Cyberark Online Training Platfrom in Hyderabad? To Enroll a Free Demo Click Here. |
23) What is an On-Demand Privileges Manager (OPM)?
Ans: On-Demand Privileges Manager allows privileged users to run administrative commands from their native Unix or Linux sessions. It eliminates the need for root access or admin rights.
This secure solution provides unified, correlated logging of all superuser activities. It enables granular access control and continuous monitoring of all superusers' activities, based on their roles and tasks.
24) What is an Application Identity Manager (AIM)?
Ans: The Application Identity Manager is a Windows- and Linux-based application that facilitates access to privileged passwords and eliminates the need to hard-code plaintext passwords in applications, scripts, or configuration files.
As with all other credentials stored in the Enterprise Password Vault, AIM passwords are strongly stored, logged, and managed.
AIM is separated into two components:
- a Provider, which securely retrieves and caches passwords and provides immediate access to the requesting application
- The SDK, which provides a set of APIs for Java, .NET, COM14, CLI15, and C/C++.
In the evaluated version, the AIM Provider for Windows and SDK have been excluded.
25) What do you mean by Penetration Test?
Ans: A penetration test (Pen Test) attempts to exploit the vulnerabilities to determine whether unauthorized access or other malicious activity is possible.
Penetration testing typically includes network and application security testing, as well as controls and processes for networks and applications. It should occur from both outside the network, trying to come in (external testing), and from inside the network.
Related Article: Wallix vs Cyberark
CyberArk Interview Questions For Experienced
In this section, we will explore advanced CyberArk questions that broaden your understanding of CyberArk components.
26) If a CyberArk vault user changes his Active Directory password, what will happen with his CyberArk account?
Ans: Nothing happens if CyberArk uses LDAP authentication.
27) Which component is used on all CyberArk solutions?
Ans: CyberArk Enterprise Password Vault, a component of the CyberArk Privileged Account Security Solution, is used on all CyberArk Solutions.
It is designed to identify, secure, rotate, and control access to privileged account passwords used to access systems across any organization.
The solution helps organizations understand the scope of their privileged account risks and implement controls to minimise them.
28) What do you need to enable an auto password reconciliation policy in CyberArk?
Ans: The following prerequisites are required to enable an auto password-reconciliation policy in CyberArk.
- Enable Password reconciliation for a specific policy within an Organization.
- An additional account on the target server, along with creating sufficient rights
- System administrators should enable automatic password verification
29) What are the User Directories supported by CyberArk?
Ans: CyberArk supports Active Directory, Oracle Internet Directory, Novell eDirectory, and IBM Tivoli DS.
30) What are the steps required to register a privileged account to CyberArk PIMS using PVWA?
Ans: To register for a privileged account, you need to:
- Create a safe & define the safe owner
- Create a PIM Policy
- Create CPM & PSM Policy
- Add an account with its properties (username, password, address, etc.)
31) What does CyberArk PSM's web form capability mean?
Ans: CyberArk PSM has web form capabilities, meaning it can be used with conditional logic. A PSM connector can be integrated into a web-based application.
By default, PSM web capability only covers the HTML login page with a form id, an input form for user/password, and a button name attribute.
32) What do you understand by Privileged Threat Analytics?
Ans: CyberArk Privileged Threat Analytics is a safety intelligence solution that enables organisations to detect, alert, and respond to anomalous privileged activity that indicates an attack in progress.
The image below shows the function of the privileged threat analytics engine.
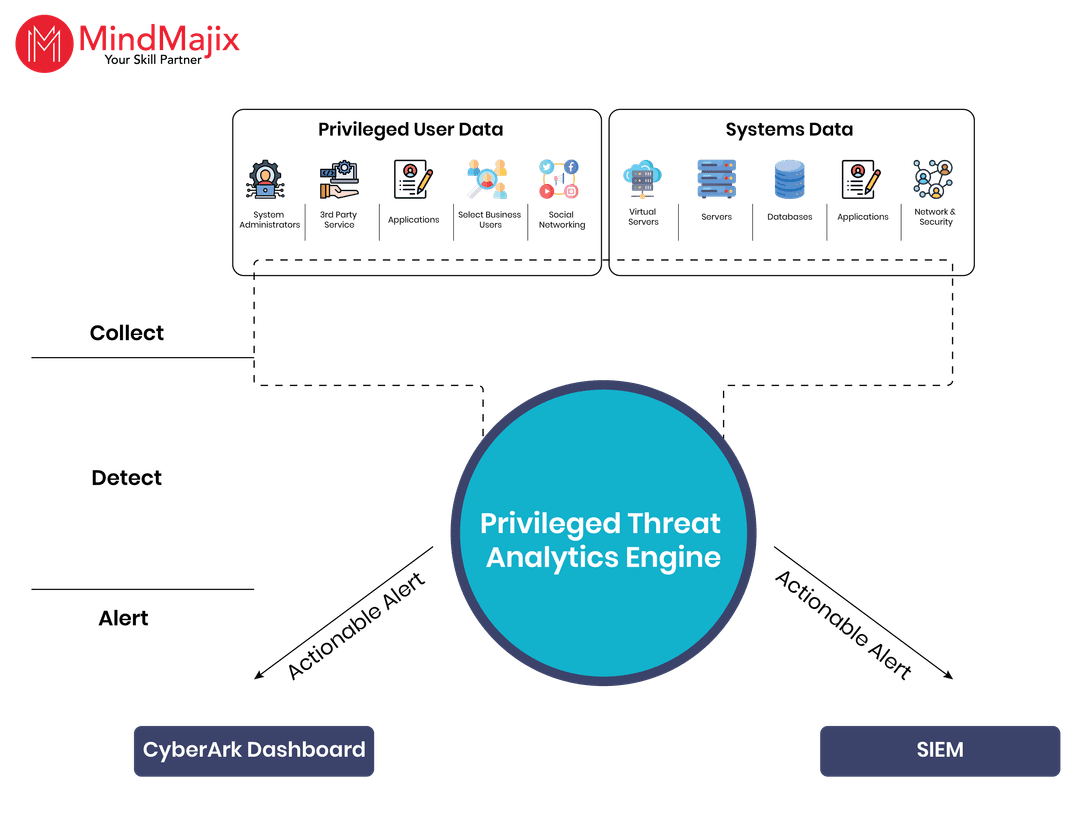
The solution collects a targeted set of data from multiple sources, including the CyberArk Digital Vault, SIEM, and network taps or switches. Then, the solution applies a complex combination of statistical algorithms.
It enables organizations to detect indicators of compromise early in the attack lifecycle by identifying malicious activity involving privileged accounts.
33) What do you understand by Privileged Session Manager?
Ans: Privileged Session Manager (PSM) secures, controls, and scrutinizes privileged user access and activities across various systems.
The systems can be Unix, Linux, and Windows-based systems, databases, virtual machines, network devices, SaaS applications, and more.
PSM provides a single point of access control, prevents malware from jumping to any target system, and records every keystroke and mouse click for continuous monitoring.
34) Explain the SSH Key Manager.
Ans: Privileged Unix/Linux users and applications use the SSH keys to validate privileged accounts.
Let’s see how the SSH key manager prevents unauthenticated access to private SSH keys.
- SSH Key Manager secures and rotates privileged SSH keys in accordance with the privileged account security policy and controls.
- It scrutinises the access to privileged accounts.
- It enables organizations to gain control over SSH keys, which provide access to privileged accounts.
35) Which component of CyberArk enables commands to be whitelisted or blacklisted on a per-user and/or per-system basis?
Ans: The On-Demand Privileges manager enables the commands to be whitelisted or blacklisted.
36) Can CyberArk Vault be managed manually?
Ans: CyberArk Vault can be managed using PrivateArk Client, PrivateArk Web Client, and Private Vault Web Access.
CyberArk Interview Preparation Tips
Only enhancing your technical skills is not adequate to ace your interviews. You also need to look into other aspects to succeed in your interviews.
Let’s take a look at them here.
- Understand the role specifications – Before attending the interview, thoroughly review the role requirements and plan your preparation accordingly. It will help you focus on your preparation process and perform better in your interviews.
- Strong technical expertise – You must have a strong knowledge of cybersecurity fundamentals and advanced concepts.
- Showcase your leadership qualities – Speak about the leadership roles you played in your recent projects, team management, and project deliveries. Highlight how your decisions positively impacted your past projects and the team's overall efficiency.
- Prepare for behavioural questions – In addition to technical interviews, you must prepare for behavioral and coding-based questions. They are essential to acing your interviews.
- Review and relax – The day before your interview is crucial. Go over your preparation notes and take some time to relax. Plan the next day carefully. Make clear-cut plans to reach the interview location or to arrange a virtual interview.
Frequently Asked Questions
1) Is learning CyberArk easy for beginners?
Ans: Yes, beginners can learn CyberArk easily. MindMajix offer expert-led CyberArk training for learners of all levels, regardless of prior technical background. Our training curriculum covers basic and core CyberArk concepts to provide comprehensive knowledge to all learners.
2) What roles can I apply for after completing this training?
Ans:
- CyberArk Engineer
- CyberArk Architect
- CyberArk Support Specialist
- Network Security Engineer
- CyberArk Analyst
- Information Security Engineer
3) How long will it take to complete CyberArk training?
Ans: You can learn CyberArk quickly. MindMajix offers 20-hour CyberArk training in live online mode and 10-hour training in self-paced mode. You can choose the learning mode that suits your convenience and schedule.
4) Does your CyberArk training help me clear CyberArk interviews?
Ans: Yes, absolutely. We offer all learners post-training support, covering interview preparation support and a job search assistance program. Along with technical training, you will go through mock interviews and resume preparation guidance to help you crack your interviews effortlessly.
5) Which industries commonly hire CyberArk professionals?
Ans: The University of San Diego reports that key industries such as financial services, government, healthcare, manufacturing, and retail are hiring CyberArk professionals with soaring salaries.
6) Do you offer any other learning materials in addition to this CyberArk IQA?
Ans: Yes, we provide the following eLearning materials to reinforce your understanding of the CyberArk platform.
Conclusion
Well! You have gone through the most sought-after CyberArk interview questions and answers. We hope you will feel confident after thoroughly learning all these questions and answers.
If you want to learn more about CyberArk, contact MindMajix, which offers CyberArk training in live online and self-paced modes. At the end of the training, you will gain the expertise to breeze through your CyberArk interviews easily and build a strong career in cybersecurity.
 On-Job Support Service
On-Job Support Service
Online Work Support for your on-job roles.

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs:
- Pay Per Hour
- Pay Per Week
- Monthly
| Name | Dates | |
|---|---|---|
| CyberArk Training | Jun 06 to Jun 21 | View Details |
| CyberArk Training | Jun 09 to Jun 24 | View Details |
| CyberArk Training | Jun 13 to Jun 28 | View Details |
| CyberArk Training | Jun 16 to Jul 01 | View Details |

Ravindra Savaram is a Technical Lead at Mindmajix.com. His passion lies in writing articles on the most popular IT platforms including Machine learning, DevOps, Data Science, Artificial Intelligence, RPA, Deep Learning, and so on. You can stay up to date on all these technologies by following him on LinkedIn and Twitter.
















