As the number of products and services utilized by companies has risen, corporate access control has become an important layer of security. Access control, on the other hand, is not restricted to the cloud. It directly affects the majority of the company's IT assets, ranging from desktop logins to physical access to server vaults. As a result, in order to guarantee optimal security in your company, you should develop a centralized access control strategy.
Two important access management approaches that can help you with this work are PAM and PIM. In this article, we'll look at the differences between PIM and PAM.
Listed below are the topics covered in this blog
PAM vs PIM - Table of Content
- What is privileged access management (PAM)?
- Principles of privileged access management
- PAM Features
- PIM Tools
- PAM Pros and Cons
- How does PAM work?
- What is Privileged Identity Management?
- PIM Features
- How does PIM work?
- PIM Pros and Cons
- PIM vs PAM: Comparison
What is privileged access management (PAM)?
Privileged access management (PAM) is a toolkit and technology that enables a company to safeguard, limit, and track access to even more sensitive data and resources. Shared folders password policy, privileged access control, vendor privileged access management (VPAM), and app access management are all subcategories of PAM.
Because they have increased privileges, disclosure of personal information, and the ability to change settings, privileged user accounts are a significant target for hackers. If the system is breached, the organization's operations could be severely harmed. Emergency cybersecurity measures, localized administrator, Microsoft Active Directory, application or service, and domain administrator accounts all use PAM
| If you want to enrich your career and become a professional in CyberArk, then enrol in "CyberArk Training" - This course will help you to achieve excellence in this domain. |
Principles of privileged access management
- Guiding Principle One: Prevent Credential Theft
For assigning and tracking privileged account credentials, many organizations rely on inefficient manual methods. Passwords and keys can sometimes stay the same for months or even years after being given out. Former employees, contractors, and business partners frequently keep access to vital applications and systems after leaving the company, exposing it to data breaches and hostile attacks.
To launch complex attacks, disgruntled workers or external intruders can exploit dormant accounts or outdated passwords.
- Guiding Principle Two: Stop Lateral and Vertical Movement
An adversary will frequently pivot from lower-value devices to greater targets that hold sensitive information or can be utilized to govern an environment once they have credentials. There are two ways to do this:
- Moving laterally inside the same "risk tier" in the hopes of discovering better, more valuable credentials.
- Moving vertically from one risk layer to the next (for example, from workstations to servers) to get closer to the target.
- Guiding Principle Three: Limit Privilege Escalation and Abuse
Privileged accounts are all around us. Each host, application, database, and platform comes with its unique set of administrative credentials. Many businesses manually manage privileged credentials and have limited visibility and control over privileged session activity.
To make problems worse, many companies over-privilege end-users and application processes, giving them full admin capabilities regardless of their actual needs. The proliferation of privileged accounts, as well as a lack of administrative visibility and control, offer a large attack surface for hostile insiders and foreign attackers to take advantage of.
PAM Features
For firms developing or having an extensive, complicated IT system.
Many well-known companies, including BeyondTrust, Centrify, CyberArk, SecureLink, and Thycotic, have begun to offer enterprise PAM solutions.
The following features are commonly seen in PAM tools and software:
- Multi-Factor Authentication (MFA) is required for administrators.
- Authorizations and confidential user data manage
- A password vault that securely stores privileged passwords;
- Once you've been granted privileged access, you'll be able to track your sessions.
- Dynamic authorization capabilities, such as providing access just for a set amount of time
- To reduce insider threats, automate provisioning and de-provisioning; and
- Audit logging software that assists organizations in achieving compliance.
PIM Tools
Privileged Access Management (PAM) Software: The Best of the Best
- JumpCloud
- Microsoft Azure Active Directory
- AWS Secrets Manager
- strongDM
- Ping Identity
- BeyondTrust Privileged Remote Access
- CyberArk Privileged Access Security Solution
- SecureLink Enterprise Access
- ARCON | Privileged Access Management (PAM)
- Delinea Secret Server
PAM Pros and Cons
Advantages of PAM:
- Their customer service and a team of Customer Success Managers are outstanding; they are constantly available and have never failed to resolve an issue.
- Compared to our previous custom in-house system, it is simple to use, scale, and manage.
- Significant features and functionality perform as intended, ensuring that our users have reliable and secure access to applications.
- It allows for remote administration of any operating system. The tool records user sessions and auditing logs, which comes in handy during forensic investigations. It offers threat analytics capabilities and can spot unusual password-stealing activity.
- Provides a more straightforward login mechanism for all users and extra security settings for particular applications via MFA.
- Easy and secure SSO connection with MFA Get all of your everyday apps on a single page that you can access with a single click.
- Installing and using the product is simple. Compared to other items, it is more user-friendly. The UI makes it simple to identify and monitor systems.
Disadvantages of PAM:
- It's a little difficult to connect with some of our bespoke apps, but it's not a big deal.
- New feature releases don't always appear to have been thoroughly tested in all potential scenarios. Documentation may be out of date at times. Inconsistent product expertise across members of the support team.
- Physical servers may be recommended for password vaults, and numerous physical servers may be required for high availability and backup. Continuous session recording necessitated a larger storage space.
- It can be challenging for applications that don't support SAML. Learning passwords, for example, can be time-consuming.
- During product version transitions, the screens can get shaky. It can be difficult at times to keep track of the overall situation of the additional resources.
- It can occasionally fail without warning, appearing to work but really logging you out of several products and needing a restart. This is a rare problem.
- The original product cost is a tad on the high side, which may put small and medium businesses off. Because it is about security, it includes a lot of hardware/software needs for the initial setup, which could extend the rollout duration.
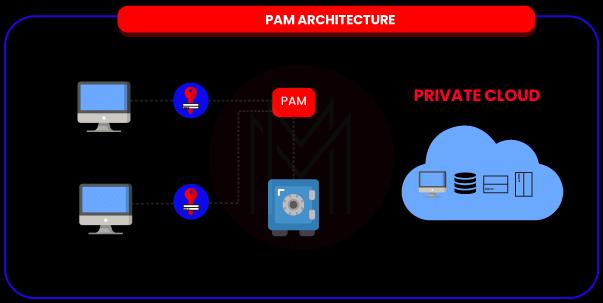
How does PAM work?
PAM systems store privileged account credentials in a vault, such as admin accounts. System administrators must access the PAM system's credentials while inside the vault, where they will be authorized, and their access will be logged. Whenever a password is tried to check in, it is reset, requiring administrators to use the PAM system the next time they need it.
What is Privileged Identity Management?
Privileged Identity Management (PIM) is an Azure Active Directory (Azure AD) service that allows you to manage, regulate, and monitor access to critical resources in your company. Azure AD, Azure, and other Microsoft Online Services, including Microsoft 365 and Microsoft Intune, are examples of these resources.
A privileged account is an administrator account with the ability to modify configuration settings permissions, add users, and download software, among other things. Secure privileged accounts with a privileged identity management system. These are super administrators with special access rights to sensitive data.
PIM Features
Privileged Identity Management allows you to activate roles on a time and approval basis, reducing the risk of excessive, unneeded, or inappropriate accessing permissions on resources you care about. Privileged Identity Management has several significant aspects.
- Provide privileged access to Azure AD and Azure resources on a per-request basis.
- With start and end dates, assign moment access to resources.
- Activate privileged roles only with permission.
- To activate any role, set up multi-factor authentication.
- To learn why people activate, use reasoning.
- If privileged roles are turned on, you'll be notified.
- Perform access audits to confirm that users' roles are still required.
- During internal or external audits, download the audit history.
- The previous active Global Administrator role allocation will not be removed.
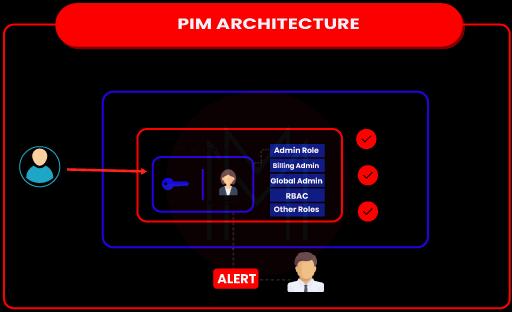
How does PIM work?
A PIM product oversees the lifespan of all user accounts with access to an IT infrastructure, with a particular focus on privileged accounts. It first locates and documents all essential IT assets and the privileged accounts and roles that have access to them. It then makes sure that restrictions for those accounts are followed, such as password difficulty and time of use. It also logs, monitors, and audits each privileged access request, issuing alarms whenever one is deemed suspicious or inappropriate.
The potential to centralize track, manage and audit affiliations and authorizations throughout the entire Network aligns special rights with every worker's duties and functions, immensely minimizing the chances of privilege creep, which happens whenever a user progressively acquires privileges.
In contrast, the privileges of previous roles are not removed. It can also help prevent insider threats by notifying administrators of every strange behaviour by an on-premises privileged user. When granting appropriate access privileges to internal resources, individuals in charge of privileged identity management will profit from a well-implemented data classification policy. Regular audits ensure that linked permissions are realigned effectively, especially when employing automated role-assignment technology. The sensitivity of data held on multiple servers and databases can change over time.
| Read these latest CyberArk Interview Questions and Answers that help you grab high-paying jobs. |
PIM Pros and Cons
Advantages of PIM:
- Allow privileged access only when needed.
- Provides resources with time-limited access.
- To activate roles, you should use multi-factor authentication.
- Access to privileged accounts can be restricted.
- Password changes on a schedule and in response to events
- The logs of events and sessions are kept.
- Access to privileged accounts can be tracked.
Disadvantages of PIM:
- The ongoing costs are extremely significant.
- Failing to Identify All Privy Accounts.
PIM vs PAM - Comparison
| Parameters | PAM | PIM |
| Definition | A system for securing, managing, monitoring, and controlling privileges. | A system for managing, controlling, and monitoring access to resources in the company that has admin/superuser access. |
| Technology | LDAP & SAML | LDAP |
| Applications | One Identity, Foxpass, Hitachi ID, etc. | ManageEngine, Microsoft Azure, Okta identity cloud, Auth0, etc. |
Conclusion
We've come to the end of the blog, and we've learned about the various differences between PIM and PAM. If you’ve any queries related to PAM vs PIM, let us know in the comments section below.
 On-Job Support Service
On-Job Support Service
Online Work Support for your on-job roles.

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs:
- Pay Per Hour
- Pay Per Week
- Monthly
| Name | Dates | |
|---|---|---|
| CyberArk Training | Jun 06 to Jun 21 | View Details |
| CyberArk Training | Jun 09 to Jun 24 | View Details |
| CyberArk Training | Jun 13 to Jun 28 | View Details |
| CyberArk Training | Jun 16 to Jul 01 | View Details |

Madhuri is a Senior Content Creator at MindMajix. She has written about a range of different topics on various technologies, which include, Splunk, Tensorflow, Selenium, and CEH. She spends most of her time researching on technology, and startups. Connect with her via LinkedIn and Twitter .
















