Courtesy of the constantly evolving security threats, safeguarding business information has become quite arduous and challenging. The increased need for exchanging business information has made businesses more prone to advanced cyberattacks. Herein, one minor data breach can cause serious troubles and damages to the business and can also impact future survival. To counter the ever-evolving security breaches and threats, Fortinet comes into play as an advanced cybersecurity solution for businesses operating across the globe. In this Fortinet tutorial, let’s find out more about this cybersecurity solution.
Here’s what you’ll learn in this Fortinet Tutorial:
Fortinet Tutorial: Table of Content
- What is Fortinet?
- Fortinet History
- Is Fortinet a VPN?
- What is a Fortinet analyzer?
- Advantages of Fortinet
- What is Fortinet Firewall?
- How does the Fortigate Firewall work?
- How to configure the FortiGate firewall step by step?
- Fortinet Products
What is Fortinet?
Fortinet is one cybersecurity solution provider that caters to almost every type of industry and business, right from the one operating at a small scale to the one functioning at a large scale. Currently, more than 50,000 businesses are using this solution to secure their systems from security threats.
Fortinet helps support customers with the capabilities needed to securely exchange information across the world by offering intelligent, advanced, and effortless protection across networks. The modern Security Fabric architecture provides 360-degree security to counter challenges in regard to mobile, cloud, or network environments.
| If you want to enrich your career and become a professional in Fortinet, then enroll in "Fortinet Training" - This course will help you to achieve excellence in this domain |
Currently, Fortinet is leading the custom Security Processing Unit (SPU) technology domain. It makes use of significant Machine Learning (ML) and artificial intelligence systems to process 100 billion+ events every day. In addition to this, Fortinet can also help customers by sending threat intelligence insights in real-time and suggesting measures.
Fortinet History
Fortinet was established back in 2000 by Michel Xie and Ken Xie. Its office is headquartered in Sunnyvale, California. The first product of this company was FortiGate - a physical firewall. Today, Fortinet is developing and marketing an extensive range of software solutions, such as intrusion prevention systems, endpoint security components, anti-virus protection, messaging security, and sandboxing.
Is Fortinet a VPN?
Fortinet can be used for VPN access into the network. It offers transitions of the working scenario quite smoothly. The Fortinet VPN secures access from users who are working from home, offers easy implementation and setup, and also combines VPN access and antivirus within one tool.
What is a Fortinet analyzer?
FortiAnalyzer is quite a powerful log management, reporting, and analytics platform that provides single-pane orchestration, response, and automation for simplified security operations, remediation of risks, proactive identification of threats, and comprehensive visibility of the attack surface.
[ Related Article: Fortinet Tutorial ]
Advantages of Fortinet
If you wish to assess the advantages of Fortinet, jotted down below are some points for your reference:
- Delivers products and tools for every type of security-related issue
- Easy to learn the configuration of every product
- Enhances performance while decreasing the cost
- Ensures secure access to every network
- Offers 24/7 coverage to keep your network protected
- Acquires detailed knowledge of security
- Easy management and handling of network devices
- Detailed logging for all events
- Interactive UI for users to navigate
- Offers a comprehensive solution for content-based threats
- Offers visibility for detecting hidden threats
What is Fortinet Firewall?
The FortiGate Next-Generation Firewalls (NGFWs) have been curated to offer better visibility, high performance, multi-layered security, and more such advantages to manage advanced threats and decrease complexity. The FortiGate firewalls are available with advanced builtin processors that provide the best threat protection for traffic that is SSL-encrypted.
The NGFWs provide advanced threat protection. Furthermore, you also get precise visibility into users, IoT devices, and applications and can discover issues instantly.
How does the Fortigate Firewall work?
The firewall acts as the front-line security personnel to discover security threats. However, the advanced methodologies that the attackers are using can manipulate the firewalls into believing that the source is dependable. To counter this issue, the Fortigate firewall helps detect the threats and evaluate the encrypted traffic that the business is receiving.
To put in simple words, the Fortigate Firewall is made to assess the data that is flowing into your network. And then, it decides whether the data should be passed through your site or not.
How to configure the FortiGate firewall step by step?
Here are some steps that you can follow to configure your FortiGate firewall. Your default username would be admin and there will be no password. To configure the WAN and internal interfaces, follow these steps:
- Go to system > choose Network > choose Interfaces
- There, you can configure the WAN interface and configure the internal interface
- If you are using Mac, you will have to assign the IP address and the mac address of the administrator PC
To configure the default route, follow these steps:
- Go to Router > choose Static > choose Static Routes
You can set the Destination IP/Mask to 0.0.0.0/0.0.0.0.
- DNS settings can be kept as default.
- In terms of policies, you can create two of them - general policy is for restricted internet access and the administrator PC policy is for unrestricted internet access
Fortinet Products
Following are some of the best and varying products that Fortinet offers to meet the organizational requirement of multiple security across the world. These products could be extremely beneficial to safeguard the operations of your company. Let’s find out more about them:
1. FortiGate
FortiGate is referred to as the next-generation firewall. Being the core product of the company, FortiGate provides threat protection to every business type, working across every sector. Considering that the domain of IT is surrounded by a wide range of threats, this product is equipped with intelligent features that help countering breaches.
Moreover, Fortinet provides a variety of models of FortiGate that further help meeting the development requirements of every business type by providing a variety of series that range from FortiGate-20 series to FortiGate-1500 series.
FortiGate Firewall Features
Below-mentioned are some of the essential features that FortiGate firewall offers:
- Virtual Private Network (VPN)
- Advanced options for web filtering
- Intrusion prevention
- Application behaviour analysis
- Anti-spam, antivirus and web filtering
- Three proxy-based antivirus database
- Four options of malware for antispyware and antivirus
- WAN optimization
- VoIP security
[ Related article: Fortinet vs Sonicwall - What’s the Difference? ]
2. FortiTester
The FortiTester is another product that comes from the basket of Fortinet. This one is an advanced security solution that helps building, managing and securing the infrastructure. FortiTester provides a consistent evaluation mechanism that secures the infrastructure.
In addition to this, FortiTester defines network performance testing as well as Breach Attack Simulation (BAS) that further helps security operations to evaluate technology, people and process.
FortiTester Features
Here are some noteworthy features that FortiTester has to provide:
- Performance testing
- Traffic generation testing
- Traffic mix
- Flexible form factor
- Protocol support
- Breach attack simulation
- Effortless third-party integration
- Comprehensive reporting
- Extensive API support
- Security testing
3. FortiCloud
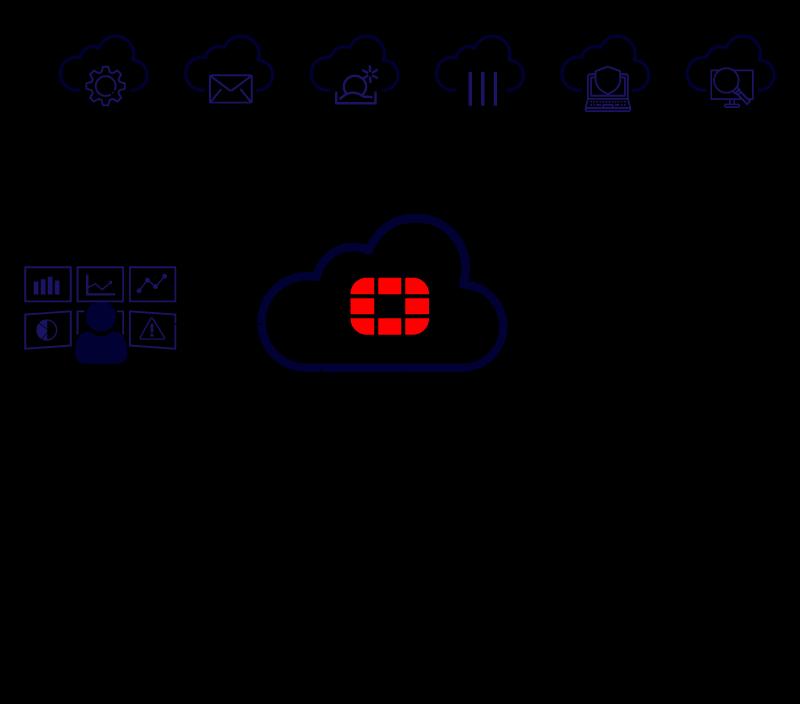
Coming to the third product of Fortinet, FortiCloud offers a simplified, intuitive environment that can be used to connect, exchange data as well as safeguard applications on both on-premises and in-cloud environments. FortiCloud comes as a Security-as-a-Service (SaaS) product and provides one single source to handle an extensive range of solutions.
Furthermore, it offers accessibility to manage varying Fortinet devices and accounts effortlessly.
FortiCloud Features
Here is a list of features you can expect in FortiCloud:
- Application and traffic visibility
- Hosted log retention
- Cloud provisioning
- Reporting and analytics
- Configuration management
4. FortiOS
FortiOS is one purpose-developed operating system that acts as the base for the company. This one is a unified operating system that lets users manage and control networking and security capabilities, irrespective of the type. Moreover, FortiOS comes with an extensive range of modern features and capabilities to provide unhindered visibility, integrated threat intelligence, and automated responses to meet the requirements and needs of digital businesses.
FortiOS Features
Here are some of the effective features you can find in FortiOS:
- Security-driven networking
- Zero-trust access
- Adaptive cloud security
- Central management and provisioning
- Cloud and SDN integration
- Advanced threat protection.
[ Check out: Fortinet vs Palo Alto ]
5. FortiAI
FortiAI is another advanced product that is AI-based and offers breach protection technology. This product has been specifically developed for short-staffed Security Operation Center (SOC) teams so that they can easily discover and fight against advanced and persistent threats.
FortiAI, as the name suggests, makes use of in-demand technologies, such as Machine Learning (ML) and Artificial Intelligence (AI) to detect threats before it’s too late.
FortiAI Features
Jotted down below are some features you can find in FortiAI:
- Network security
- Adaptive cloud security
- AI-driven security operations
- Networking and communications
Conclusion
Fortigate is constantly evolving to achieve newer heights. It is helping businesses by updating the existing products and bringing more into the collection so as to assist effectively in meeting the modern security breaches that are ever-evolving. Businesses across the world are using Fortinet and its products to secure from threats. If you haven’t given it a try, it’s time to do so now.
 On-Job Support Service
On-Job Support Service
Online Work Support for your on-job roles.

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs:
- Pay Per Hour
- Pay Per Week
- Monthly
| Name | Dates | |
|---|---|---|
| Fortinet Training | Jun 06 to Jun 21 | View Details |
| Fortinet Training | Jun 09 to Jun 24 | View Details |
| Fortinet Training | Jun 13 to Jun 28 | View Details |
| Fortinet Training | Jun 16 to Jul 01 | View Details |

Madhuri is a Senior Content Creator at MindMajix. She has written about a range of different topics on various technologies, which include, Splunk, Tensorflow, Selenium, and CEH. She spends most of her time researching on technology, and startups. Connect with her via LinkedIn and Twitter .
















