- Home
- Blog
- Blockchain
- Blockchain Interview Questions and Answers

- Bitcoin Interview Question and Answers
- Bitcoin Pros and Cons
- Bitcoin Tutorial - What is Bitcoin?
- Bitcoin vs Ethereum vs Blockchain
- Blockchain Tutorial
- How Does BlockChain Technology Work?
- How to Implement Blockchain - 7 Strategies You Should Know
- Hyperledger Tutorial
- Reasons Why You Should Learn More About Bitcoin
- 10 Reasons Why Blockchain is Worth Getting Excited
- Redefining Electronic Health Records with Blockchain Technology
- Tangle Technology
- Theory of Blockchain Explained
- An Insight Into Blockchain Technology
- What is Bitcoin and how does it work?
- Introduction to Distributed Ledgers
- What is Cryptocurrency?
- Ethereum VS Hyperledger
- Components of Blockchain
- Blockchain Projects and Use Cases
In this Blockchain Interview Questions blog, we have listed the most important Blockchain interview questions and answers that will set you apart in the interview process.
All the questions presented here are frequently asked in many interviews, and help you to acquire a dream career in this domain. But before we start with the interview questions, let's take a quick look at Blockchain's demand in the market.
- According to Gartner, the business value of blockchain will exceed $3.1 trillion by 2030.
- The Blockchain job market is booming with ample opportunities across various industries - Glassdoor.
- The median salary of a Blockchain professional ranges around $1,32,000 per annum.
The above figures indicate that Blockchain has a huge demand in the market and you can have a great career as a Blockchain developer. However, there is high competition among Blockchain career aspirants and clearing the interview is no easy task.
| If you want to enrich your career and become a professional in Blockchain, then visit Mindmajix - a global online training platform: "Blockchain Training" This course will help you to achieve excellence in this domain. |
To help you perform best in the Blockchain job interview, we have divided the interview questions into three parts based on the complexity. Let’s start and discuss every topic in detail.
| Learn the Following Interview Questions on Blockchain |
Blockchain Interview Questions - List of Contents
- What is Blockchain?
- How does blockchain work?
- Why is blockchain a trusted approach?
- What are the major elements of a block?
- What are the different types of blockchains?
- What is the difference between public and private keys?
- What is Cryptocurrency?
- What are the key principles in a blockchain that help in eliminating security threats?
- What is Secret Sharing?
- What is an RSA algorithm?
Blockchain Interview Questions - Basic Level
1. What is Blockchain?
Blockchain is an incorruptible digital ledger of economic transactions that can be programmed to record not only financial transactions but virtually everything of value.
In simple terms, it is a decentralized distributed database of immutable records that are managed by a cluster of computers but not owned by any single entity. Blockchain is stored as a database or a flat-file.
| Related Article: Blockchain Development Tutorial |
2. Mention the popular blockchain platforms.
The popular Blockchain platforms are as follows:
| Blockchain Platform | Consensus Algorithm | Ledger type | Governance |
|
Ethereum
| Proof of Work | Permissionless | Ethereum Developers |
| Hyperledger Sawtooth | Pluggable Framework | Permissioned | Linux Foundation |
| Hyperledger Fabric | Pluggable Framework | Permissioned | Linux Foundation |
| Hyperledger Iroha | Chain-based Byzantine Fault Tolerant | Permissioned | Linux Foundation |
| OpenChain | Partitioned Consensus | Permissioned | Linux Foundation |
| Stellar | Stellar Consensus Protocol | Both public and private | Stellar Development Foundation |
| NEO | Delegated Byzantine Fault Tolerance | Permissioned | On-chain governance through votes of NEO holders and Off-chain governance through NEO Foundation support. |
| EOS | Delegated Proof of Stake | Permissioned | EOSIO Core Arbitration Forum (ECAF) |
| Hedera Hashgraph | Asynchronous Byzantine Fault Tolerance | Permissioned | Hedera Hashgraph Council |
| R3 Corda | Asynchronous Byzantine Fault Tolerance | Permissioned | Hedera Hashgraph Council |
| Quorum | Majority Voting | Permissioned | Ethereum Developers and JP Morgan Chase |
| Ripple | Permissioned | Ripple Labs |
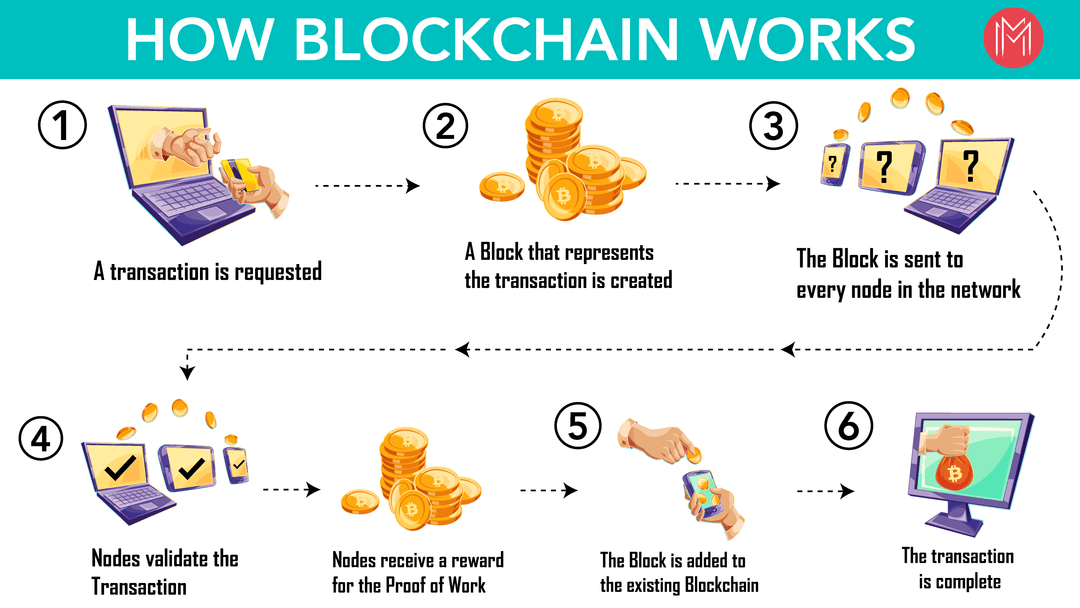
3. How does blockchain work?
Blockchain consists of immutable records of data called blocks which are linked using cryptography. Cryptography is nothing but a process to encrypt and secure data communication from third parties in reading private messages.
In Blockchain, once the data has been recorded, it will not be changed. Blockchain works like a digital notary with timestamps to avoid tampering with information.
| Related Article: How Does Blockchain Technology Work |
4. Why is blockchain a trusted approach?
The following reasons will help you understand why blockchain is a trusted approach:
- Its compatibility with other business applications due to its open-source nature.
- Its transparency level and security are nearly unprecedented.
- Improves efficiency and speed.
- It is safe and hack-proof.
- There is no central authority you need to depend on, and this trustlessness makes Blockchain a trusted technology.
5. What is a block in a blockchain, and how is it recognized?
A block in a blockchain is nothing but a digital safe to store the data and lock it forever. The data added on the block is immutable, i.e., data cannot be changed or deleted.
Blocks can be recognized by their block height and block header hash. The data in the block is detected through a computerized algorithm known as a Hash function.
It not only locks the data to be seen by the participants in the Blockchain but also makes the data immutable. Every block has its hash function.
6. What are the major elements of a block?
The following are the major elements of a block:
- A hash pointer to the previous block
- Timestamp
- List of transactions
7. Is it possible to remove one or more blocks from the networks in blockchain?
Yes, it is possible. Sometimes, only a particular portion of this online ledger needs to be considered. By using default filters and options, we can remove the blocks.
8. Is it possible to change the data once it is written in a block?
No, it is not possible to do so. In case any modification is required, the organization has to erase the information from all other blocks too.
9. What are the types of records that are available in the blockchain database?
Two types of records are available in the Blockchain database. They are:
- Transactional Records
- Block Records
Both the records can be easily accessed and integrated without following any sophisticated algorithm.
| Related Article: Blockchain Explained |
10. Which type of records can be kept in the blockchain?
We can put any records in the blockchain. Some of the common types of records are listed below:
- Transaction processing
- Identity management
- Events related to organizations
- Management activities
- Documentation
- Records of medical transactions
11. What are the different types of blockchains?
The three major types of blockchains available are listed below:
Public Blockchain: As the name suggests, here no one is in charge, and anyone can read/write/audit the blockchain.
Private Blockchain: As the name suggests, it is the private property of an individual or an organization.
Consortium or Federated Blockchain: Selected members of the Consortium can read/write/audit the blockchain
Watch this video on “Top 10 Highest Paying IT Jobs in 2021” and know how to get into these job roles.
12. What are ledgers and name the common types of ledgers that are considered by users in blockchain?
A ledger is a file that is growing continuously. It stores the permanent record of all the transactions taking place between the two parties on the blockchain network.
The common types of ledgers considered by the users in the Blockchain are as follows:
- Centralized Ledgers
- Decentralized Ledgers
- Distributed Ledgers
13. What is the difference between public and private keys?
In the blockchain, public keys are required for identification and private keys are used for encryption and authentication purposes.
The sender can send a message using the public key of the receiver and the receiver can decrypt the message or the transaction using a private key. By using both keys, communication or transaction is kept safe and tamper-proof.
14. What are the major features of blockchain?
The major features of Blockchain are listed below:
- Decentralized system
- Increased capacity
- Minting
- Faster settlements
- Immutability
- Safe and secure ecosystem
15. In what order blocks are linked in blockchain?
All the blocks in the blockchain are linked in backward order or each block links with its previous block.
16. What does BIP stand for?
BIP stands for Bitcoin Improvement Proposal.
Blockchain Interview Questions - Intermediate Level
17. What is encryption and what is its role in blockchain?
Encryption is one of the methods of data security that helps organizations keep their data secure. In encryption, any type of data can be converted from a readable format to an encrypted version and can only be decoded by another entity who actually has access to the decrypted key.
In the blockchain, this approach is useful as it adds more to the overall security and authenticity of blocks and keeps them secure.
18. How is a blockchain ledger different from an ordinary one?
The primary difference is Blockchain is a digital ledger that can be decentralized very easily and the chances of errors are far less in blockchain ledger when compared with the original ledger.
Blockchain performs all of its tasks automatically, while in the ordinary ledger, every task is completed with hands or human efforts.
19. What is the consensus algorithm?
A consensus algorithm is a method through which all the peers of the blockchain network reach a standard agreement of the present state of a distributed ledger.
It achieves high reliability and establishes trust between unknown peers in the distributed computing environment.
20. What are the types of consensus algorithms?
The most popular consensus algorithms available are listed below:
- Proof-of-Work(PoW)
- Proof-of-Capacity (PoC)
- Proof-of-Activity (PoA)
- Delegated Proof-of-Stake(DPoS)
- Proof-of-Stake(PoS)
- Proof-of-Authority
- Proof-of-Burn
- Unique Node Lists
- Proof-of-Weight
- Proof-of-Elapsed Time
- SIEVE
- Byzantine Fault Tolerance
21. Which cryptographic algorithm is used in Bitcoin Blockchain?
Different blockchains use different cryptographic algorithms. Bitcoin Blockchain uses a SHA256 Hashing algorithm.
22. What is Cryptocurrency?
- A cryptocurrency is a digital asset that can be used as a medium of exchange for conducting financial transactions using cryptographic functions.
- Cryptocurrencies leverage blockchain technology to gain transparency, decentralization, and immutability.
- Cryptocurrencies can be sent directly between two parties using public and private keys with minimal processing fees.
23. What are the benefits of using blockchain technology?
The key benefits of using blockchain technology are as follows:
- Enhanced security
- Improved traceability
- Cost-saving
- User pseudonymity
- Immutability
- Transparency of transactions
- Automatic reconciliation of accounts
- Fraud control
- No payment for intermediaries services
| Related Article: How to Implement Blockchain |
24. What are the core components of blockchain architecture?
The below-mentioned ones are the core components of blockchain architecture:
- Node - User/computer within the blockchain architecture.
- Transaction - It is the smallest building block of the blockchain system.
- Block - It is used for maintaining a set of transactions that are distributed to all the nodes in the network.
- Chain - Sequence of blocks.
- Miners - Specific nodes that perform a block verification process before adding to the blockchain structure.
- Consensus protocol - Set of rules to carry out blockchain operations.
25. Is it true that a block in the blockchain can never have more than one parent block?
Yes, it’s true that blockchain can never have a parent block. Every block is independent in Blockchain.
Blockchain Interview Questions - Advanced Level
26. What is double-spending?
Double-spending is considered to be a potential flaw in the digital cash scheme because the same digital tokens are used multiple times. The tokens generally consist of digital files that can be easily cloned.
Bitcoin users protect themselves from double-spending frauds by waiting for confirmations while making payments on the blockchain; the transactions become more irreversible as the confirmations rise.
27. What is a blind signature?
A blind signature is a form of digital signature in cryptography where the content of the message is blinded before it is signed or considered.
It is mostly used in privacy-related protocols where the author and signing parties are different. It is a verified approach.
Ex: Digital cash scheme
28. What are the key principles in a blockchain that help in eliminating security threats?
The following are the key principles in a blockchain that help in eliminating security threats:
- Continuity planning
- Auditing
- Securing testing and similar approaches
- Database security
- Securing applications
- Digital workforce training
29. What is the difference between Proof-of-Stake and Proof-of-Work?
Proof-of-Work is the original Consensus algorithm in the blockchain. It is used for confirming transactions and producing new blocks to the chain. In this miners compete with each other to complete the transactions on the network and get rewarded.
Proof-of-Stake makes the consensus mechanism completely virtual. In this, a set of nodes decide to stake their cryptocurrencies of the transaction validation.
Visit here to learn Blockchain Online Course in Hyderabad
30. What is a 51% attack?
A 51% attack or double-spend attack refers to an individual or group of miners on a blockchain who try to control more than 50% of the network’s mining hash rate or computing power.
These attackers try to prevent the new transactions from gaining confirmations and enable them to halt payments between some or all the users.
They are also capable of reversing transactions that are completed while they are in control of the network; it means they could double-spend coins.
31. What is a Coinbase transaction?
A Coinbase transaction is a unique type of bitcoin transaction that is created by miners. It is the first transaction in the new block.
The miners use it to collect the block reward of their work. Any transaction fees collected by the miners are also sent in this transaction.
32. What are the Merkle trees? What is its importance in blockchain?
Merkle tree plays a major role in blockchain technology. It describes a mathematical data structure that is composed of various blocks of data. It also summarizes all the transactions in a block by providing a digital fingerprint of the entire set of transactions.
It allows efficient and secure verification of content across a large body of data. Merkle tree is also known as a Hash tree and mostly used by Ethereum and Bitcoin.
The importance of a Merkle tree in the blockchain is that if anyone wants to verify the specific transaction in a block, they can download the chain of block headers instead of downloading every transaction and every block.
33. What keeps your transaction data safe in blockchain?
Blockchain, as the name implies, is a chain of digital blocks that stores records of transactions. Every block is connected to all the blocks before and after it.
This makes it difficult for hackers to tamper with the single record as they need to change the entire block containing the record along with the block connected to it for avoiding detection. Blockchain offers an excellent level of security.
In addition to the above, it also offers the following inherent characteristics:
- Records are protected through cryptography on the blockchain.
- Network participants have their own private keys for transactions, and they act as personal digital signatures.
- If a record is altered, the signature will become invalid
34. What is Secret Sharing?
Secret Sharing is one of the primary methods used for providing data security in blockchain.
This approach segregates personal or secret information into various units and sends them to the users on the network. The original information is shared for participants to whom the share of the secret is allocated.
35. What exactly do you know about executive accounting? Does blockchain support the same?
Executive accounting is a special type of accounting that is designed for the business to offer services to the people. In fact, there is no upper limit on the services and the business can manage any through executive accounting.
Blockchain has algorithms that are specially designed for executive accounting, and it cuts down the problems that are associated with the same.
36. What is a security policy?
A security policy is a formal and brief plan that embraces the organization's goals, objectives, and procedures for information security.
In simple terms, it defines what exactly needs to be secured from threats and how to handle the situation when they occur.
37. What is a trapdoor function in blockchain development?
A trapdoor function is a one-way function, i.e., easy to compute in one direction but hard to compute in the opposite direction unless you have the special information.
These functions are essential for public-key encryption and are most widely used in blockchain development to represent the ideas of addresses and private keys.
38. Why does Blockchain need coins or tokens?
Tokens/Coins are used as a medium of exchange between the states. They are digital assets built in to perform a specific function within a blockchain.
When someone does a transaction, there is a change of state, and coins are moved from one address to another address. Apart from that, transactions contain some additional data; this data can be mutated through the change of state.
For this reason, blockchains need coins or tokens to incentivize the participants to join their networks.
39. What is the difference between a scriptPubKey and a P2SH address?
- A scriptPubKey is found in transaction output and also known as a locking script.
- The P2SH address is a special type of address, i.e., it is used for replacing complex locking scripts with its hash. In addition to the unlocking scripts, the transactions must contain the script that matches the hash.
40. What is Mining?
In the context of blockchain technology, mining is the process of adding transactions to the large distributed public ledger by providing the proof of work to the network, i.e., generated block is valid.
It also adds new coins to the generated block. The term mining is best known for its association with bitcoin.
41. How is a hard fork different from a soft fork in blockchain?
- A hard fork in blockchain refers to a radical change to the software protocol, that makes previously invalid transactions/blocks valid. It requires all the users/nodes to upgrade to the latest software protocol.
- Soft fork refers to a change to the software protocol that makes previously invalid transactions/blocks invalid.
42. How to implement a blockchain project?
Follow the below stages to implement a blockchain project.
- Select your platform
- Initialize the blockchain
- Choose the right consensus protocol
- Perform your first smart contract
- Debug and scale
43. What is the difference between off-chain transactions and on-chain transactions?
On-chain transactions: These transactions are available on the blockchain and are visible to all the nodes on the blockchain network. It includes authentication and validation of a transaction by a defined number of participants.
Off-chain transactions: These transactions deal with the values outside the blockchain and can be carried out using various methods.
44. What is the difference between a centralized network, decentralized network, and distributed ledger?
Distributed ledger: It is a shared ledger and is not controlled by any central authority. It is decentralized by nature and acts as a database for financial, legal or electronic assets.
Centralized network: A centralized network has a central authority to facilitate its operations.
Decentralized network: The nodes connected in the decentralized network are not dependent on the single server point, and each node holds the entire copy of the network configurations.
Leave an Inquiry to learn Blockchain Certification Course in Bangalore
45. Which are the most widely used cryptographic algorithms?
The most frequently used cryptographic algorithms are listed below:
- Triple DES
- RSA
- Blowfish
- Twofish
- AES
46. What is an RSA algorithm?
RSA (Rivest-Shamir-Adelman) algorithm is the first algorithm that is used for signing data and encryption. It is most widely used for securing sensitive data.
It is also known as an asymmetric cryptographic algorithm that works on two different keys, namely public and private keys. The public key can be shared with anyone and the private key must be kept secret.
47. Can RSA be attacked? If so, how?
Yes, hackers can attack the RSA algorithm. However, being attacked is not equal to weak protection.
Mostly, there are two ways employed for attacking RSA:
- Brute force: Includes all potential secret keys.
- Mathematical attacks: In this, we use different techniques that are similar to factor the product of two primes.
48. What are the major elements of the blockchain ecosystem?
The blockchain has four major elements:
Shared ledger - It is decentralized in nature and is a central component of the blockchain.
Node application - It is software that lets your computer connect with the blockchain. Ex: Bitcoin uses the bitcoin wallet application to detect each mode on the network.
Virtual application - It handles all the tasks that blockchain undertakes.
Consensus algorithm - This is used for managing blockchain rules through which each node can come to a conclusion.
49. How will you handle risk management when it comes to securing the transaction records?
Based on the value of data, there are various approaches employed to handle risk management.
- First, identify the threats and vulnerabilities associated with the financial records of an organization and take the right countermeasures against them accordingly.
- Another approach is to pay attention to a backup plan.
- The third one is to buy a new risk management software.
50. Are there any network-specific conditions for employing Blockchain technology in an organization?
There are no network-specific conditions for employing Blockchain. However, the network must be a peer-to-peer network under specific protocols.
Blockchain approves the new blocks easily and helps organizations to keep up the pace without investing in third-party applications.
If you have any additional questions for us, please mention them in the comment section below and we will get back to you at the earliest.
 On-Job Support Service
On-Job Support Service
Online Work Support for your on-job roles.

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs:
- Pay Per Hour
- Pay Per Week
- Monthly
| Name | Dates | |
|---|---|---|
| Blockchain Training | Jun 06 to Jun 21 | View Details |
| Blockchain Training | Jun 09 to Jun 24 | View Details |
| Blockchain Training | Jun 13 to Jun 28 | View Details |
| Blockchain Training | Jun 16 to Jul 01 | View Details |

Madhuri is a Senior Content Creator at MindMajix. She has written about a range of different topics on various technologies, which include, Splunk, Tensorflow, Selenium, and CEH. She spends most of her time researching on technology, and startups. Connect with her via LinkedIn and Twitter .


