As businesses grow in this fast-paced world, they must protect their digital assets and identities with effective IAM solutions.
For instance, IT teams must manage thousands of employee and customer credentials across multiple devices. Thus, even a single security lapse can cause a disaster for any business.
This is where Okta Identity and Access Management comes in. Okta is one of the leading IAM solutions that helps secure your IT resources across cloud and on-premises environments.
In this post, let’s explore how Okta IAM can address modern security threats and reduce IT friction.
Table of Contents
- What is Identity and Access Management?
- Okta Identity and Access Management - Overview
- Okta Integration Network (OIN)
- Okta Single Sign-On
- Active Directory and LDAP Integration
- Okta Identity and Access Management as a Framework
- How to Mitigate Risk with Okta Identity Management?
- Frequently Asked Questions
What is Identity and Access Management?
Identity and Access Management is an effective solution for securing identities against internal and external threats. To achieve this, IAM solutions employ authentication, authorisation, and access control.
IAM ensures that authorised users sign in to business networks, thereby strengthening organisations' cybersecurity initiatives.

Want to learn more? Continue reading to delve deeper into the fundamentals of Okta identity management.
| If you want to enrich your career and become a professional in OKTA, then enroll in "OKTA Training". This course will help you to achieve excellence in this domain. |
Okta Identity and Access Management - Overview
Okta is an enterprise-grade IAM solution that secures identities for everyone—from AI agents to organizational stakeholders.
Okta IAM helps connect people with any device or application. It runs on a secure, audited, and reliable cloud platform that integrates seamlessly with directories, identity management systems, and on-premises applications.
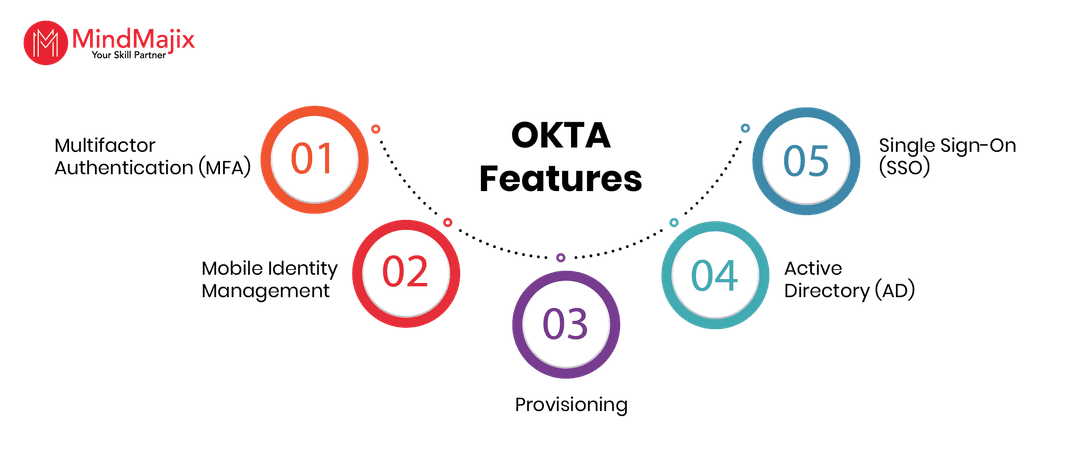
Okta has a wealth of features, such as:
- Provisioning
- Active Directory (AD)
- Single Sign-On (SSO)
- LDAP Integration
- Centralized Deprovisioning of users
- Multifactor Authentication (MFA)
- Mobile Identity Management.
All these features and policies come together through a network of pre-integrated applications known as the OKTA Integration Network (OIN). We will explore OIN in the coming section.
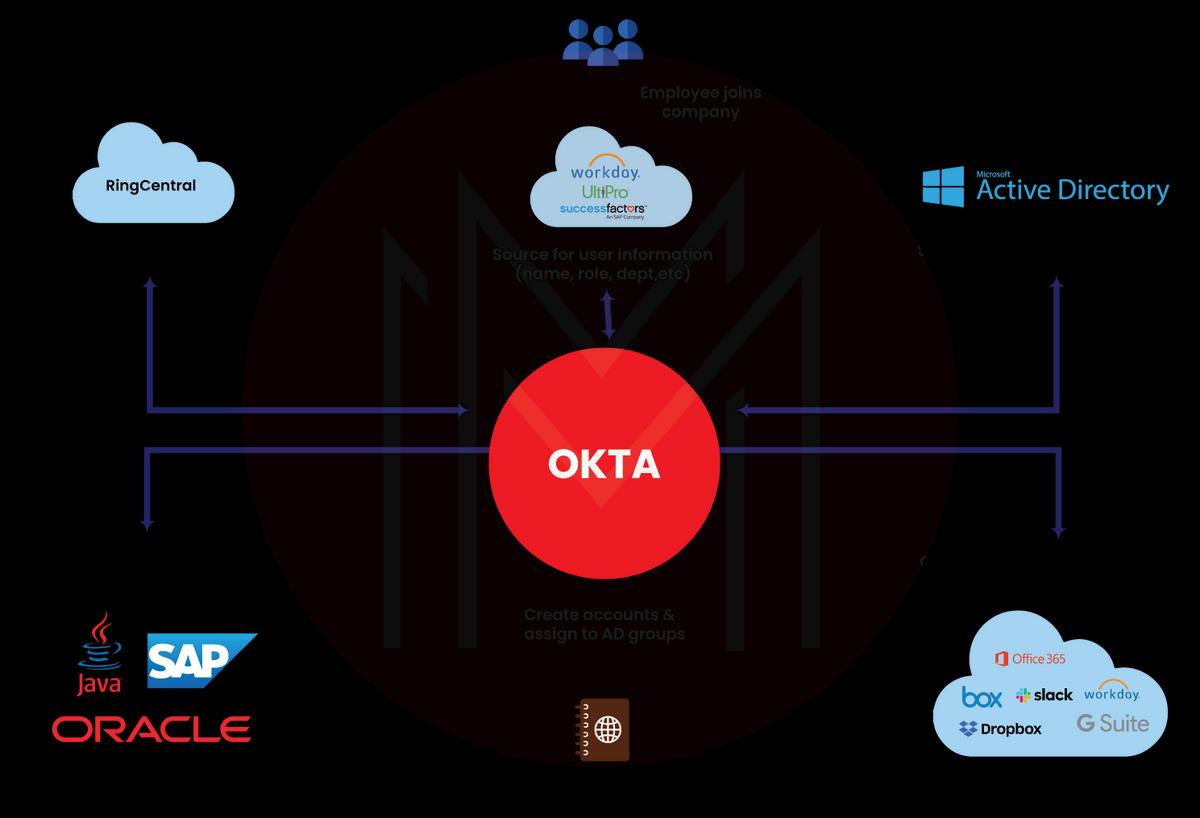
Okta Integration Network (OIN)
OIN offers many prebuilt integrations to ensure secure third-party integrations and protect your organisation from the threat landscape.
This OIN enables SSO login for every application you will use in a business day. It also simplifies integration with external applications that adhere to strict security standards. For example, OIN requires that every integration undergo a verification process before it can function.
OIN focuses on implementing automated integrations and verifies that every integration follows a consistent protocol for authentication and provisioning.
Okta Single Sign-On
Let’s dig into how Okta leverages SSO to enable identity security.
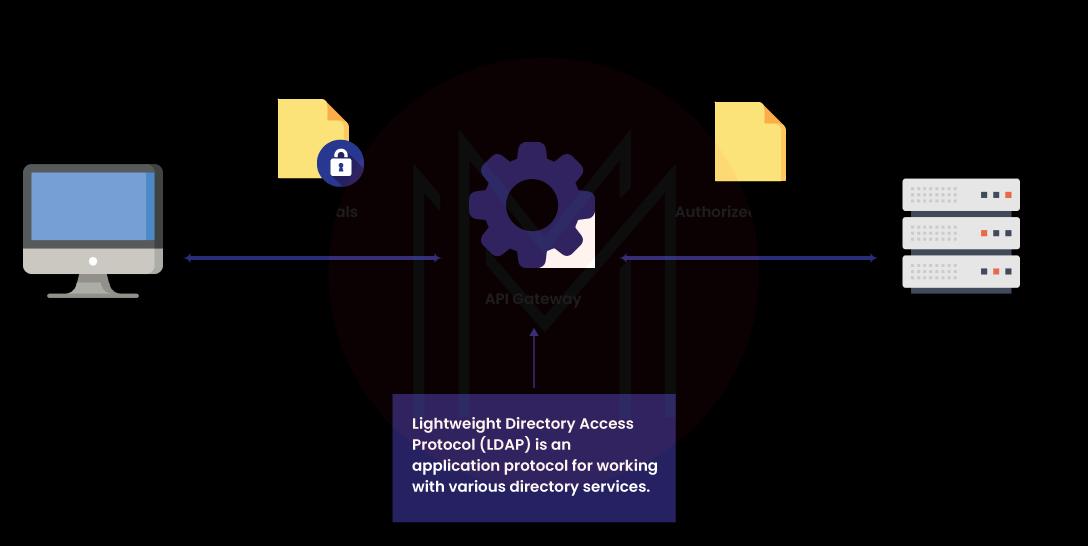
SSO eliminates the need for passwords and enables phishing-resistant authentication flows. It helps users log in easily and securely. You can use SSO to integrate with all identity storage systems, like AD and LDAP.
SSO helps eliminate identity sprawl and manage all identities from a single control plane.
Active Directory and LDAP Integration
Many organisations use Microsoft’s Active Directory (AD) as an authoritative user directory that governs access to primary business applications.
When it comes to SaaS apps, they are usually developed with their native user directories. Since they run outside the firewall, they are generally beyond AD’s administrative control.
The drawback is that users must manage multiple logins and usernames. IT teams are required to create, handle, and map user accounts in AD and around their SaaS apps. Okta overcomes this drawback with a complete, robust, and easy AD SSO integration.
| Check out OKTA Alternatives |
OKTA Identity and Access Management as a Framework
An IAM framework helps organise services, policies, concepts, and other components.
In simple terms, a good IAM framework helps you govern who exactly the business network's target audience is and what services they can or cannot access.
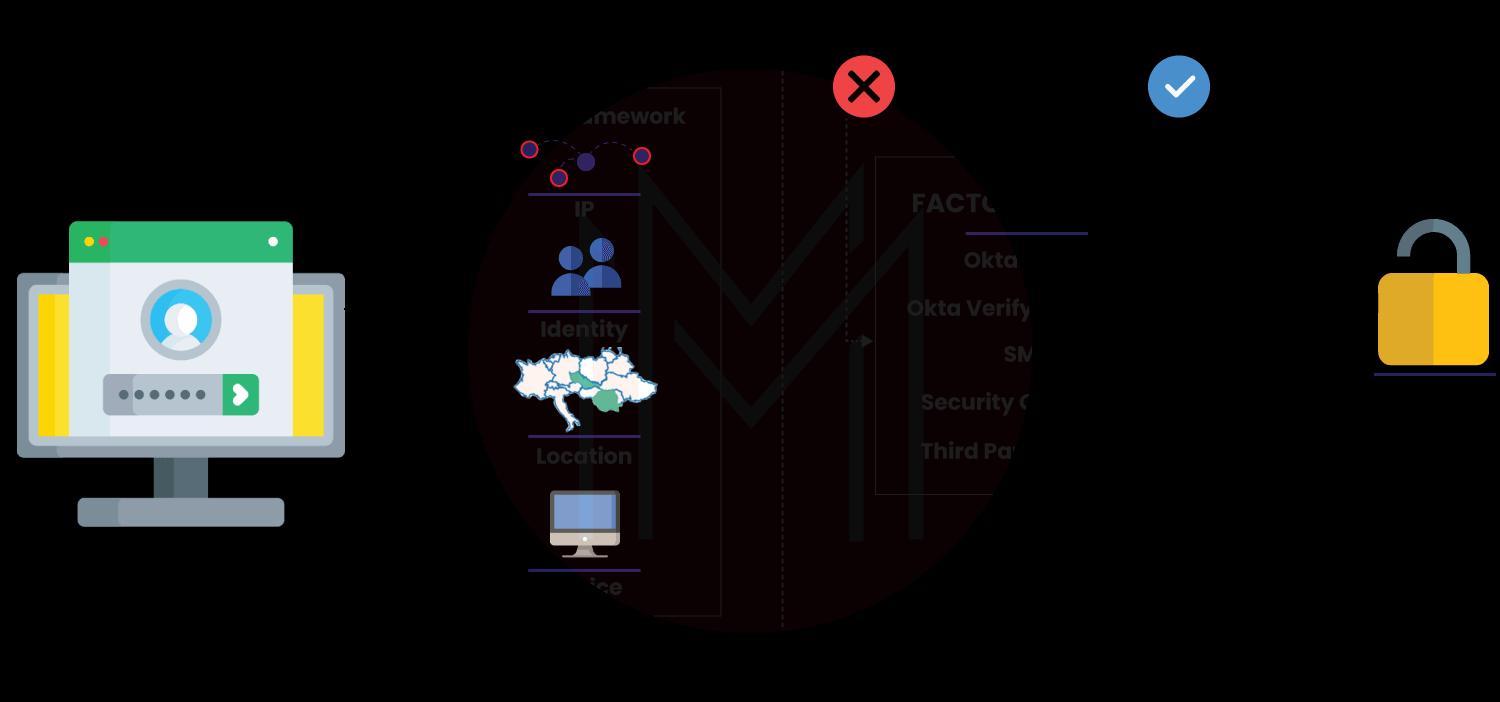
An Okta IAM framework builds a comprehensive user profile based on the devices they use, the operating systems they run, and their usage trends.
The framework fine-tunes access control by granting or restricting access based on real-time risk assessment, without compromising security.
Above all, the Okta framework bridges the gap between traditional identity security approaches and modern, flexible IAM strategies.
- Core components of the Okta IAM framework
The core components of the IAM framework help manage access controls and user identities, enhancing security across an organisation's digital space.
Let’s outline the core components.
- Identity management and user lifecycle – It includes user provisioning and deprovisioning, profile management and privileged account management.
- Role-based access – It includes role management, dynamic assignment and analytics.
- User authentication methods – There are knowledge-based and possession-based user authentication methods. They also include MFA, biometric, and passwordless methods.
- Authorization and access control – It covers policy-based and attribute-based access control, JIT access and separation of duties.
- Directory services - They manage centralized repositories, as well as meta and virtual directories.
How to Mitigate Risk with OKTA Identity Management?
Previously, employees often reused the same password across multiple apps. It forced IT admins to spend most of their working hours managing credentials, thereby compromising productivity.
As companies increasingly shift to cloud-based tools, IT admins are increasingly using IAM solutions, such as Okta, to manage identities more efficiently and mitigate risk.
Let’s understand how Okta IAM reduces security risks.
By pairing adaptive multi-factor authentication with SSO, you can secure an organization’s IT assets from single-password-related threats.
It also allows you to set conditional access that verifies users' networks, devices, and locations in real time, significantly reducing risk.
- Effective Okta identity lifecycle management
Moreover, Okta excels in identity lifecycle management, especially when organisations experience frequent employee turnover.
In this scenario, you must effectively modify, grant, or revoke employees' access to several applications. You can automate this task and mitigate the associated risks by integrating a lifecycle management solution.
| Learn OKTA Interview Questions and Answers |
Frequently Asked Questions
1. Is it hard to learn Okta?
Ans: No, anyone can easily learn Okta. If you gain a basic understanding of IT security and IAM processes, you will find it easier to learn Okta.
2. How long will it take to learn Okta with MindMajix?
Ans: You can learn Okta quickly. MindMajix offers 15 hours of on-demand Okta training and live online classes for the Okta administrator role, and 20 hours for the Okta developer role. You can choose either one course based on your role, or both together.
3. Does Okta offer a free trial?
Ans: Yes, Okta offers a 30-day free trial option, which you can use for your learning needs.
4. What are the platforms with which Okta integrates?
Ans: You can integrate Okta with the following:
- Microsoft
- Workday
- Slack
- AWS
5. Which companies use Okta extensively?
Ans: According to Okta, the following major companies use Okta for their IAM solutions.
- Zapier
- Hitachi
- McLaren
- Navan
- HPE
- Zoom
Conclusion
Undeniably, the Okta identity and access management platform plays a vital role in implementing identity security in organizations. We have highlighted the core features of Okta IAM in this blog, which should be helpful to you.
If you are interested in pursuing a career in Okta, then you can reach out to MindMajix. We offer comprehensive Okta training with a curriculum tailored to both beginners and advanced learners.
 On-Job Support Service
On-Job Support Service
Online Work Support for your on-job roles.

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs:
- Pay Per Hour
- Pay Per Week
- Monthly
| Name | Dates | |
|---|---|---|
| OKTA Training | Jun 06 to Jun 21 | View Details |
| OKTA Training | Jun 09 to Jun 24 | View Details |
| OKTA Training | Jun 13 to Jun 28 | View Details |
| OKTA Training | Jun 16 to Jul 01 | View Details |

Viswanath is a passionate content writer of Mindmajix. He has expertise in Trending Domains like Data Science, Artificial Intelligence, Machine Learning, Blockchain, etc. His articles help the learners to get insights about the Domain. You can reach him on Linkedin




