- Home
- Blog
- Cyber Security
- Penetration Testing Interview Questions

- Cyber Security Career Path
- Cyber Security Certifications
- Cyber Security Frameworks
- Cyber Security Interview Questions
- Cyber Security Threats and Prevention Methods
- Top 10 Cyber Security Tools In 2024
- How to Become a Cyber Security Engineer
- Reasons to Learn Cyber Security
- Cyber Security Best Practices
- What is Cyber Security?
- New Technology Trends in 2024
- Spoofing vs Phishing
- Network Security vs Cyber Security
- What is Penetration Testing?
- Bug Bounty Interview Questions
- CRISC VS CISA
- Cyber Security VS Data Science
- Cybersecurity Projects and Use Cases
A specific skill called pen-testing, otherwise known as penetration testing, is used in ethical hacking to discover potential security problems at a company proactively. Candidates seeking cybersecurity jobs with significant responsibility should be familiar with their aggregate form and procedures, according to hiring managers. By being familiar with these common interview questions, you can be more prepared for interviews for positions such as penetration tester or penetration testing engineer.
This blog has covered the top-most interview questions in three categories:
Top 10 Penetration Testing Interview Questions:
Penetration Testing Interview Questions and Answers for Freshers:
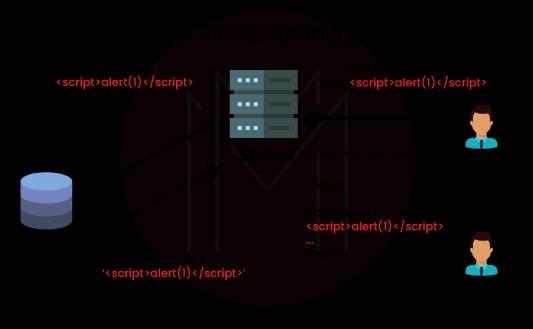
1. Define Cross-Site Scripting (XSS).
Malicious scripts get injected into otherwise innocent and trustworthy websites in Cross-Site Scripting attacks. Cross-Site Scripting (XSS) attacks take place when a hacker sends malicious code, typically in a browser-side script form, to a separate end user using an application online. These kinds of attacks can be successfully conducted everywhere an online application incorporates user input without verifying or encoding it before using it to produce output.
2. What are the different types of encryption?
The two main encryption types are symmetric and asymmetric. Symmetric encryption uses keys, which allows users and information owners to both encrypt and decrypt data using the same key. Asymmetric encryption uses a private key and a public key to safeguard more sensitive data.
| Looking forward to become a master in Cyber Security and SIEM Courses? Check out the "Penetration Testing Training" and get certified today. |
3. Tell us the advantages of Penetration Testing.
Penetration testing ensures the security of the data bank and guarantees the accuracy of all the information contained in the software. Penetration testing assists a business in swiftly identifying additional issues such as viruses, bugs, glitches, etc., in addition to providing protection against hacker attacks.
4. What is the main purpose of pen-testing?
Performing a "deep dive" into a company's or organization's IT infrastructure is the major goal of a pentest, with the primary objective being to get access to any (and, if possible, all) of the available electronic-based assets. It is vital to remember that the purpose of the pentester isn't just to attempt to strike a hard blow straightaway at the very beginning; rather, they raise the power of the cyber-attack over a timeframe.
5. Define Information Security?
The practice of protecting information from unwanted access is known as information security. This word can be defined as information availability, integrity, and confidentiality preservation. Notably, additional qualities can also be relevant, including accountability, authenticity, non-repudiation, and reliability.
6. Define pen testing in your own words.
Companies utilize a sort of testing called pen testing to find and stop security problems. This aids businesses in proactively managing risks in their networks, systems, and programs through a variety of techniques.
7. Explain Symmetric and Asymmetric Encryption.
First, encryption modifies the sequence in which data appears from its original format to prevent access from those without the necessary authorization. One passkey is used for both encryption and decryption in symmetric encryption. In such instances, the owner and end-user use the identical key and can encrypt and decode the data using the same password.
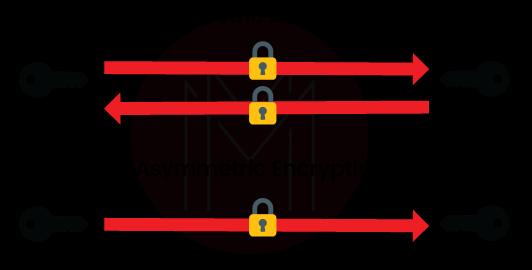
Owners of the software have a private pass key, and end users have a public pass key in asymmetric encryption. This is done to separate high-level data from the available data that the general public cannot access.
8. What is "Vulnerability"?
Every information security professional wants to get rid of the word "vulnerability" from the IT system. A system might be compromised intentionally or unintentionally if certain vulnerabilities were to be exploited.
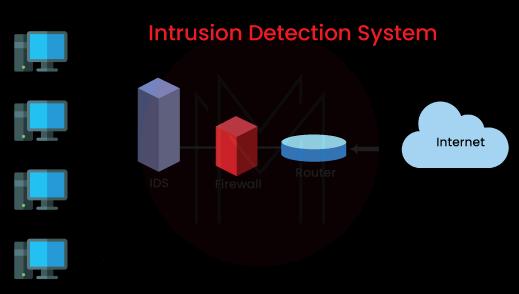
9. What's most important in data protection?
To prevent unwanted assaults on our databases, I believe it is crucial to have advanced network security measures. Since threats can occasionally be unavoidable, intrusion detection systems might even be more vital. These tools can support businesses in swiftly responding to risks and routinely monitoring safety.
[ Check out Penetration Testing Tutorial ]
10. What is the motive for conducting a pen testing exercise?
The motives are as follows:
- To assess adherence to the security policies that the business has created and executed
- To evaluate an employee's proactivity and understanding of the security environment they are in.
- To completely understand the potential impact of a significant security breach on a business organization, as well as how soon they can respond to it and resume regular business activities after being affected.
11. Define the term Intrusion Detection.
The process of identifying an external force attempting to get access to the software which is unauthorized is known as intrusion detection. As the name suggests, any sort of unauthorized access is reported as soon as it’s found so that the appropriate actions can be taken to stop the incursion. It is similar to when some burglary gets detected and found and then an alert is set off by the technology. The business shall check the software's intrusion detection technology automatically during penetration testing to ensure it’s operating properly.
12. The terms "pen-testing" and "vulnerability testing" are frequently used hand in hand. What distinguishes the two in particular?
With the aid of vulnerability testing, one is merely searching for any potential flaws in any IT infrastructure component. In a pentest, a full-scale cyberattack or series of cyberattacks are launched with the client's (or the requester's) express consent to identify any weaknesses that the IT security team has not yet identified.

13. What kind of penetration is possible with the Diffie Hellman exchange?
One of the first public-key protocols was the Diffie-Hellman key exchange (DH), which allows users to safely exchange cryptographic keys across a public channel.
With the help of this technology, poor ephemeral Diffie-Hellman parameters in detecting SSL/TLS services can be accomplished.
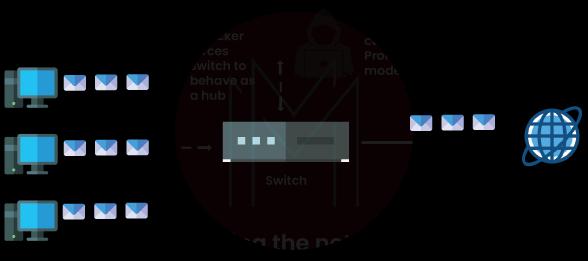
14. Describe data packet sniffing?
The method of examining network traffic to spot any odd activities or unauthorized users is known as data packet sniffing. With this, we could continuously watch over the security of our networks. I would examine the data for any new threats to see if we could identify the source or perpetrators.
15. What Are the Possible Causes of Security Vulnerabilities?
The software may be deemed vulnerable for a number of different reasons. Determining the degree of a software vulnerability is often the responsibility of penetration testers. Programming mistakes can leave software open to attack. The software can be made vulnerable through improper private and public encryption. Not having sufficient intrusion detection systems and insufficient surveillance equipment. The software can be deemed insecure if its data are not sufficiently backed up or safeguarded.
Penetration Testing Interview Questions and Answers for Experienced:
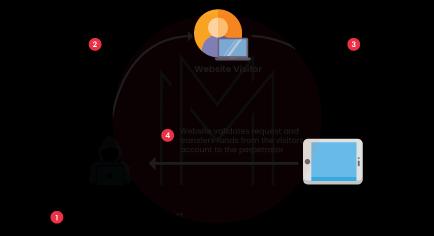
1. How can CSRF be avoided during a pentest exercise, and what exactly is it?
Cross-site request forgery, as the name implies, preys on the degrees of trust built during an authenticated user experience. In these cases, for instance, Web-based apps normally don't run any kind of testing to make sure that a given request originally came from an authenticated user; instead, the only type of verification is sent by the specific Web browser at the end user is using. Here is how to avoid this from happening:
- Verify the specific CSRF token being used by double-checking it.
- Verify that the requests in question originate from the same origin.
2. We got a Penetration Test proposal which was quoted quite lower than the rest proposals we received - why so?
The cost of penetration testing varies from firm to company. In general, a quotation of penetration testing rates is based on the security tester's pay, the cost of the tools used, the scope of the project, etc. Additionally, due to market competition, some infosec organizations charge less than others.
3. Elaborate on USSD Remote Control?
An incredible resource for vulnerability testing is USSD Remote Control. The special USSD over GPRS signaling protocol is used by USSD Remote Control. This can be used to send and receive data over GPRS with numerous devices. Utilizing USSD Remote Control for penetration testing has numerous advantages.
The penetration tester can remotely manipulate many different devices thanks to USSD Remote Control. Devices that aren't always online are included in this. A highly effective tool that may be used to manage a variety of devices is USSD Remote Control. Additionally, it enables the penetration tester to work remotely on numerous projects. For instance, the penetration tester can check devices for vulnerabilities using USSD Remote Control.
4. What are the systems on which Penetration Testing can be performed?
Penetration testing can be done on a variety of systems, including—
- Servers
- Endpoints
- Mobile devices and computers
- Web applications
- Cloud services
- Hardware systems
- Virtual private networks (VPN)
- Transmission technologies
- Public networks and wireless networks
Although we have been exclusively focused on using the term software to generalize.
To increase security, anything that can be compromised should undergo penetration testing.
5. Tell us about the three different types of cross-site scripting (XSS)?
The three types of cross-site scripting (XSS) are as follows:
- Persistent/Stored XSS: This type of attack occurs when the malicious input is saved on the target server, like a database, and then shown on the page where the end-user provided their information (example, "Contact Us" form).
- Reflected XSS: The Web-based program immediately returns any malicious user input as an "Error Message." As a result, the Web browser considers this data to be hazardous and does not save it in any way.
- DOM-based XSS: This allows any client programming language (like Java) to retrieve and maliciously alter the input from the user. Additionally, it has the ability to subtly change a webpage's content, design, also structure. The objects of the types that can be manipulated are:
- Document.URL
- Document.location
- Document.referrer
- Document.URL

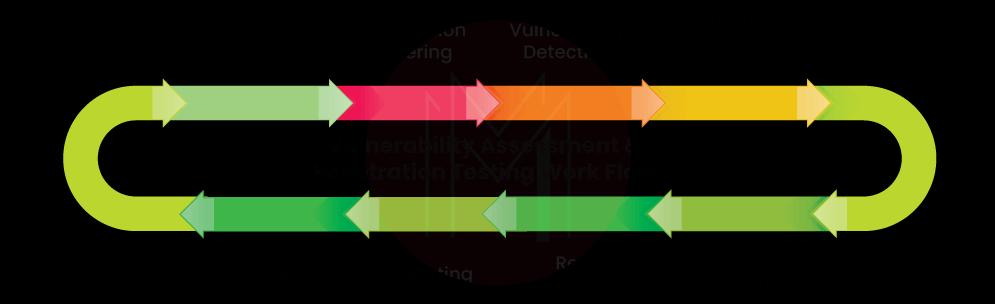
6. What are the phases of Penetration Testing?
Several efficient strategies are used in penetration testing. One of the best tactics involves the phases listed below:
- Examining the system that will be put to the test.
- Creating a backup of all the system's info.
- Modeling threats are being made.
- A hacking system attempt.
- Evaluating the vulnerabilities and holes that were found, fixing all the problems, and installing an intrusion detector.
- Making thorough records throughout the entire process
- Setting up a basic penetration testing kit.

7. Define us "STRIDE"?
STRIDE is an acronym made for the threat modeling system. It aids in categorizing all kinds of cyberattacks into the below methods:
- Spoofing
- Tampering
- Repudiation
- Information disclosure
- Denial of service (DoS)
- Elevation of privilege
8. Should Penetration Testing Be Carried out by a Third Party and why?
Many businesses frequently overlook the perimeter when it is about security. While most of the time this is reasonable, failure to adequately safeguard your internal network might result in the shutdown of your network due to breaches that frequently come from outside sources, such as malware and phishing attacks.
By delivering accurate and reliable information regarding vulnerabilities inherent in your company's systems or networks, a third-party penetration testing company can assist in alleviating some of these issues. They can also offer advice on the most effective ways to address them, such as through vulnerability remediation or assessment.
9. Tell us about the different phases of a network intrusion attack.
The phases are listed below:
- Reconnaissance: In this phase, the pentester gathers more information about the victim they will soon attack. Either an active or passive approach to this is possible. You know more about the following in this step:
- The present IP address range of the target
- Identifying its domain name
- DNS records
- Scanning: The pentester gains knowledge of the specific target's vulnerabilities at this phase. The network architecture and related software applications both have flaws. This encompasses, for instance, the following:
- Identifying the services that are being used right now
- Any open ports
- The detection of any firewalls
- Weaknesses of the operating system
- Gaining the required access: Based on the flaws and vulnerabilities they have identified in the previous step, the pentester begins to actually launch the cyber-attack at this point.
- Maintaining the access: In order to collect as much sensitive data and private information as possible, the pentester has already entered the target and is working to maintain that access point open.
- Covering their tracks: This is the final step where the pentester makes sure that no "footprints" left behind in the course of their attack are visible. This ensures that they can't be detected. This involves:
- The deletion of log-related files (if any)
- Closing off backdoors (if any)
- Hiding all controls that have been used
10. Describe the differences between risk analysis and penetration testing.
While penetration testing involves lawfully assaulting the system to identify the software's weaknesses, risk analysis basically studies all potential faults that could lead to issues with the software. While penetration testing employs a more technical approach, risk analysis is a more practical method of problem solutions.
A finance expert with some probability knowledge can perform a risk analysis; however, a penetration tester needs to be an expert in information technology with knowledge of computer programming and, ideally, hacking. When compared to penetration testing, risk analysis is more practical.
11. During penetration testing, what are some of the common ports to focus on?
Nmap tool can be used for the port scan. We've listed the common ports to focus on during pen-testing:
- FTP (port 20, 21)
- HTTP (port 80)
- HTTPS (port 443)
- NTP (port 123)
- SMTP (port 25)
- SSH (port 22)
- Telnet (port 23)
12. In penetration testing, what are the functions of the Java applet popup?
Making a Java applet popup is an easy process. First, a Java program must be written by the tester to serve as the popup. A file with the.html extension must then be created by the tester and placed in the same directory as the Java program. The file must be in the same directory as the Java program and end in.html.
Divide the file into two halves. The HTML code which is used to present the Java applet popup is found in the second portion, while the first part provides the code that'll be used to build the Java applet popup.
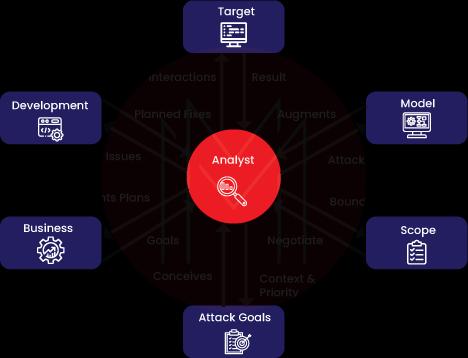
13. Give an explanation of the theoretical elements of a threat model that could be applied to a pen-testing activity.
A threat model is based on the following concepts:
- Assembling the required documentation
- Accurately recognizing and classifying the digital assets present in an organization's or business's IT infrastructure
- Accurately classifying and identifying any kind of cyber threat that might be directed at digital assets.
- Matching the digital assets' vulnerability to cyber threats appropriately (Alternatively, this might be seen as a mapping effort where a digital asset is linked to a specific cyber threat).
A pen-testing team may employ one of the following three threat model categories, which are also crucial to note:
- Cyber-Attacker-Centric
- Software Application-Centric.
- Digital Asset-Centric
What we discussed above is one of the examples of a Digital Asset-Centric Threat Model.
14. What network controls would you suggest strengthening an organization's network security?
The following top network controls aid in enhancing an organization's network security:
- Installing and using just the software and applications on the whitelist.
- All active software and applications should receive regular updates.
- Install the most recent security updates on your OS.
- Reduce administrative rights.
15. Describe Frame Injection vulnerability.
A frame injection vulnerability is a kind of security hole that enables an attacker to inject any frames they want into the stream of traffic going through a website or application. By changing the elements in an HTTP request header or by inserting frames into the answer the server sends to the browser, this can be achieved.
Small chunks of HTML or XML called frames are used to create document content and display it on a web page as if it were a part of the original document. Attackers may be able to inject code straight onto users' screens of websites and applications by injecting malicious frames into these responses, which might seriously harm those individuals personally, steal their data, and even result in a loss of income for online businesses.
| Do you want to know more about Ethical Hacking? Take a Look at this Ethical Hacking Tutorial |
Frequently Asked Penetration Testing Interview Questions and Answers:
1. Name the 5 stages of penetration testing.
The Five Phases of Penetration Testing are:
- Reconnaissance
- Scanning
- Vulnerability Assessment
- Exploitation
- Reporting

2. Tell us about the 3 types of penetration testing.
The method of penetration testing is divided into three types of testing: black-box assessment, white-box assessment, and gray-box assessment.
3. What's SOP in penetration testing?
SOP stands for Standard Operating Procedure for Pen Testing.
4. What is the meaning of white box pen testing?
White box penetration testing, also known as crystal or oblique box pen testing, entails providing the tester with complete network and system details, including network maps and credentials. This contributes to time savings and lowers the overall engagement cost.

5. What does SAST mean?
Static application security testing (SAST) is one of the methods of testing for security vulnerabilities.
6. What are the differences between vulnerability scanning and pen-testing?
Systems are searched for known vulnerabilities using vulnerability scans and vulnerability assessments. An environment is actively targeted for weaknesses during a penetration test. While a vulnerability scan can be automated, different levels of skill are needed for a penetration test.
7. Define the VAPT process?
Pen testing, often known as penetration testing, is a methodical procedure for identifying an application's vulnerability. It is also known as vulnerability assessment and penetration testing (VAPT).
8. Why is it necessary for us to stay within the pen test scope?
Proper scoping can help get rid of problems
The scope of a penetration test can also affect how well it goes by affecting how many issues are avoided. Simply said, a penetration test's scope informs the test team which objects can be targeted and examined.
9. Is penetration a test?
In a penetration test (pen test), a computer system is subjected to a legitimate simulated attack in order to evaluate its security. To identify and illustrate the financial effects of a system's vulnerabilities, penetration testers employ the same resources, strategies, and methods as attackers.
10. How long is pen testing?
It can take one to three weeks to complete a penetration test. The length of a penetration test varies on its kind, the kinds and numbers of systems it examines, and the quality of your current cybersecurity.
Conclusion
So these are some of the questions that you need to be prepared with if you are sitting for a pen-testing-based interview. This interview is normally given by a penetration tester, penetration testing engineer, or fresher looking for a job in this field. Ethical hacking is a very intricate field with high demand in the cyber world. We hope that this series of questions and answers will help you with your interview. Please make a note that we do not claim these are all the questions they ask. What is asked ultimately depends on the interviewer.
 On-Job Support Service
On-Job Support Service
Online Work Support for your on-job roles.

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs:
- Pay Per Hour
- Pay Per Week
- Monthly
| Name | Dates | |
|---|---|---|
| Penetration Testing Training | Jun 09 to Jun 24 | View Details |
| Penetration Testing Training | Jun 13 to Jun 28 | View Details |
| Penetration Testing Training | Jun 16 to Jul 01 | View Details |
| Penetration Testing Training | Jun 20 to Jul 05 | View Details |
















