- 6 Hot And In-Demand Tech Areas In 2024
- How To Forward Your Career With Cloud Skills?
- Top 7 On-Demand IT Certifications
- Most In-demand Technologies To Upskill Your Career
- Top 10 Hottest Tech Skills to Master in 2024
- Top Skills You Need to Become a Data Scientist
- Groovy Interview Questions
- Facets Interview Questions
- Crystal Reports Tutorial
- VAPT Interview Questions
- Flutter Tutorial
- Saviynt VS Sailpoint
- Flutter vs Xamarin
- PingFederate Interview Questions and Answers
- Dart vs Javascript : What's the Difference?
- Terraform Private Registry
- Cylance Interview Questions and Answers
- Sophos Interview Questions and Answers
- Top Camunda Interview Questions
- NUnit Interview Questions and Answers
- Impala Interview Questions and Answers
- ETL Tutorial
- Ionic Interview Questions
- Grafana Tutorial
- What is VAPT? - A Complete Beginners Tutorial
- SnapLogic Interview Questions
- Saviynt Interview Questions
- What is PingFederate? - A Complete Beginners Tutorial
- SnapLogic Tutorial
- Grafana Interview Questions
- RHCE Interview Questions and Answers
- Web Services Interview Questions
- Domo Interview Questions and Answers
- Terraform Interview Questions
- What is Sophos? | Sophos Turorial for Beginners
- Top Servlet Interview Question And Answers
- NLP Interview Questions and Answers
- Microsoft Intune Interview Questions
- Top XML Interview Questions And Answers
- Tosca Commander
- Katalon vs Cypress
- SQLite Tutorial
- Tosca Tutorial - A Complete Guide for Beginners
- Xamarin Interview Questions and Answers
- UiPath vs Automation Anywhere - The Key Differences
- OpenShift Interview Questions
- What is Katalon Studio - Complete Tutorial Guide
- Kronos Interview Questions
- Tosca Framework
- Burp Suite Tutorial
- Mendix Interview Questions
- Power Platform Interview Questions
- What is Mendix
- What is Terraform ?
- Burp Suite Alternatives
- Dart vs Kotlin
- What is Kronos?
- ES6 Interview Questions
- Entity Framework Interview Questions
- COBOL Interview Questions
- Express JS Interview Questions
- OSPF Interview Questions
- LINQ Tutorial
- CSS3 Interview Questions and Answers
- Auth0 Tutorial
- MS Access Interview Questions
- What is SPARQL - A Complete Tutorial Guide
- ExpressJS Tutorial
- UML Tutorial
- HTML vs XML
- Cypress vs Jest
- Impacts of Social Media
- OWASP Interview Questions
- Security Testing Interview Questions
- OpenShift vs Docker
- ES6 Tutorial
- Spark SQL Interview Questions
- Spark SQL Tutorial
- What is OWASP?
- AppDynamics Interview Questions
- Dynatrace Interview Questions
- Rest Assured Tutorial
- New Relic Interview Questions
- REST API Tutorial
- Datadog Interview Questions
- Rest API Interview Questions
- Rest Assured Interview Questions
- PTC Windchill Interview Questions
- Easiest Tech Skills To Learn
- Python SQLite Tutorial - How to Install SQLite
- Datadog Tutorial - Datadog Incident Management
- What is AppDynamics - AppDynamics Architecture
- RabbitMQ Interview Questions And Answers
- What is Dynatrace
- Datadog Vs Splunk
- Web Developer Job Description
- JP Morgan Interview Questions
- Types of Corporate Training
- Benefits of Corporate Training
- What is Corporate Restructuring?
- Blended Learning in Corporate Training
- What is Corporate Level Strategy?
- Flutter Projects and Use Cases
- How to Become a Web Developer
- How To Install Keras?
- How to Install Flutter on Windows?
- How to Install Cypress on Windows?
- How to Become a Computer Scientist?
- How to Install Katalon Studio in Windows
- How to Become a Programmer
- OWASP Projects and Use Cases
- How to Install Sophos?
- Workato Tutorial
- Workato Tutorial - What is Workato?
In an era of a rapidly changing technological landscape, we must keep our data safe. The Internet and digital revolution have made our life easier, but at the same time, we cannot deny the fact that the world has become even more complex. Websites and applications have become elemental for businesses. There is a pool of opportunities for people, but this also brought up dangerous and threatening competition. There are more cases of data and identity theft than ever. Thankfully, we have a technological solution for that as well. Software like Burp Suite is important for securing websites and web apps. And thus, the demand for Burp Suite professionals is constantly growing.
Burp Suite Interview Questions and Answers 2024 (updated) have been divided into three stages they are:
| Table of Content: Burp Suite Interview Questions |
Top 10 Burp Suite Interview Questions and Answers
- Name some tools that Burp Suite has.
- How Burp Suite tool can be used for penetration testing?
- Is Burp Suite a DAST tool?
- How can you add extensions in Burp Suite?
- What is an infiltrator in Burp Suite?
- Is Burp Suite available on Windows?
- How can you install Jython Burp?
- Elaborate on Burp Suite Professional Edition.
- What are the features of the Burp Suite tool?
- Is Burp Suite safe to use?
Burp Suite Interview Questions for Freshers:
1. In which language can Burp Suite be written?
Burp Suite is written in Java, although you can create your Burp extensions using Java or Python. However, before running a python extension, you will have to download Jython and start configuring Burp with its location.
2. Name some tools that Burp Suite has.
Various tools are responsible for performing different tasks. Some of them are:
- Mobile assistant
- Extender
- Comparer
- Decoder
- Sequencer
- Repeater
- Intruder
- Scanner
- Proxy
- Logger
- Inspector
- Collaborator
- DCM invader
- Clickbandit
3. Is Burp suite a vulnerability scanner?
At its heart, yes! But it is much more than that. It helps in navigating and crawling obstacles automatically. It also saves a huge amount of time and effort. Its architecture works on the model of fewer requests and faster scans.
4. What are the other tools that we can use from web application security apart from Burp Suite?
Following is the list of some popular alternatives to Burp Suite:
- Veracode
- Metasploit
- Acunetix
- Immuniweb
- Nessus
- Netsparker
- Qualys WAS
- OWASP ZAP
- ERPScan
- Checkmarx etc.
5. How Burp Suite tool can be used for penetration testing?
- Use Burp's browser which doesn't require any additional configuration. For this, go to Proxy>Intercept tab and click Open Browser.
- Once it runs, go to Proxy>Intercept and ensure that the intercept is on. You can now go to the browser and visit any URL.
- Every HTTP request made will be displayed on the Intercept tab only. You can view and edit each message as per your requirement
- Now click the forward button.
- For more help, you can click on Getting started with Burp proxy.

- For seeing the history, you can click on Proxy>HTTP.
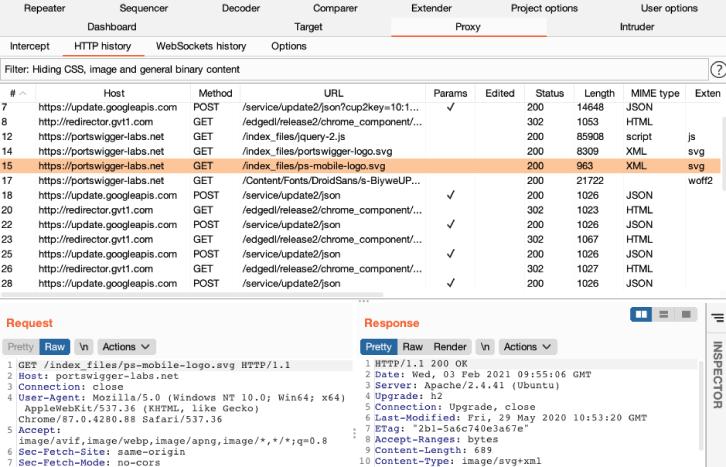
- While browsing, it builds a map of all the target applications by default. For viewing this, click on Target>Site map tab.
- For more help, you can click on Using the target tool.
| Looking forward to a career in "Software Automation Testing" Courses? Check out the "Burp Suite Training" and get certified today |
6. What vulnerabilities are detected by Burp Suite?
Following is the list of vulnerabilities that are detected by Burp Suite:
- Insecure Direct Object references
- Security misconfiguration
- Sensitive Data exposure
- Missing Function Level Access Control
- Cross-Site Request Forgery CSRF
- Using Burp to Test for Components with known vulnerabilities
- Unvalidated Redirects and Forwards
- Injection
- Broken Authentication and Session management
- Cross-Site scripting
7. Is Burp Suite a DAST tool?
Yes. Portswigger is a Dynamic Application Security Testing Software. This means that it provides insights into how your web applications behave and function while they are in production and after that. It helps enable your business or organization to find, address, and handle potential vulnerabilities on the websites and applications before a hacker uses them to attack.
8. What is active and passive scan in Burp Suite?
We already know that Burp Suite scans vulnerabilities. There are two types of them- active and passive. Active scanners are those that are responsible for sending transmissions to the network nodes and also examining the responses they receive. This leads to evaluating whether a weak point is present within that network or not. On the other side, a hacker can also use an active scanner to attack the network or application. They are capable of taking actions autonomously. They do this by blocking a potentially harmful IP address.
Passive scanners are responsible for monitoring the activities of different operations systems and applications for the determination of vulnerabilities. They are only capable of providing information about a potentially dangerous IP address but cannot take action against it like active scanners. The network administrator can use passive scanners to run on their systems at certain intervals.
9. What is Burp Suite intercept, and how does it work?
Burp Proxy allows the user to intercept HTTP requests sent between Burp's browser and the server targeted by the user. This helps them to study the behavior of your website or application during different actions. Follow the following steps for interception:
- Launch Burp's browser
- Click on Open Browser
- Intercept a request
- Forward the request
- Switch off interception
- View the HTTP history
- Click on any of them to view the HTTP request.
10. What is a Burp Suite collaborator?
Burp Suite collaborator can be described as a tool or a network service that is used to help the user in the discovery of different kinds of vulnerabilities. This happens when it runs as a single server. It also uses its domain names.
11. How long does it take to learn Burp Suite?
If you want to learn Burp Suite, the training is provided by Port Swigger itself. It has options for self-study as well. You can take the development and learning pathways and practice examination to get a certification. It is available for both freshers and advanced Burp Suite users across the globe. It depends on your interest, skill set, and grasping power.
12. What is the use of intruders in Burp Suite?
Burp Suite intruder can be defined as a tool that helps automate customized attacks on your web applications or websites. You can also use it to perform various tasks such as simple brute force guessing to exploit complex blind SQL injection vulnerabilities. It works by making an HTTP request and analyzing responses. You can also save it from intruder attacks.
13. How can you add extensions in Burp Suite?
Follow the given steps to install an extension in Burp Suite:
- Open the BApp store first.
- Select the extension you wish to install by clicking on Install.
- The extensions you will install will be displayed on the Extensions tab.
- Now you can add, remove, and reorder all these with the help of the extension table.
14. How can you download Burp pro?
Following are the steps you need to follow to download Burp pro:
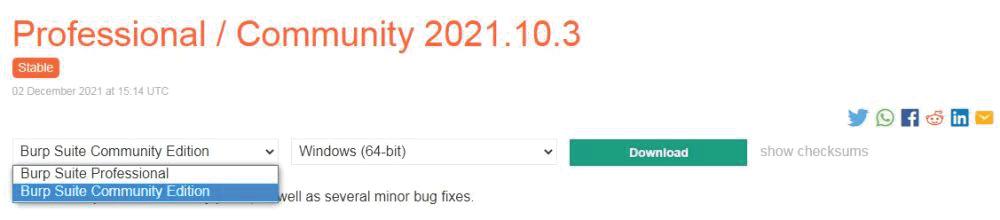
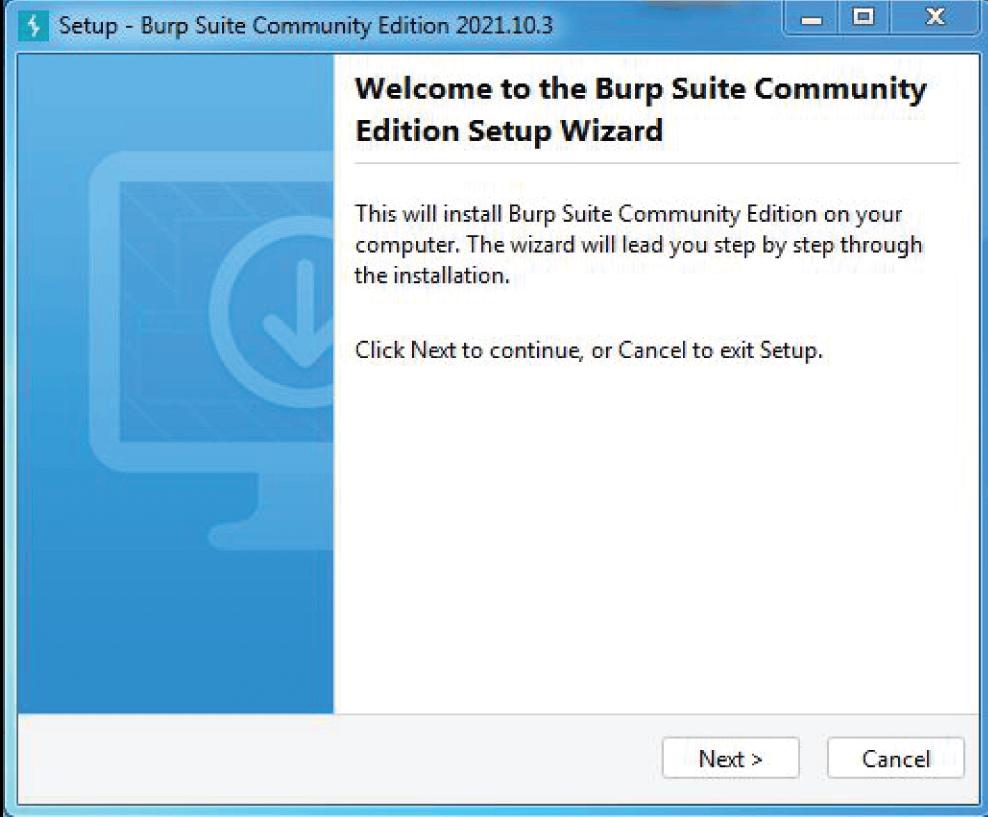
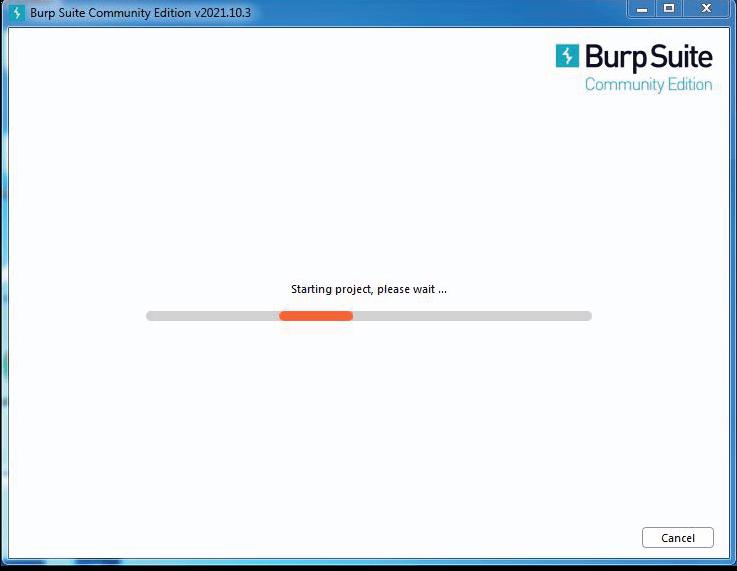
- Download the latest version of Burp Suite Professional Edition. The Community edition can also be installed.
- The next step is to install. For this, run the installer and launch.
- Start exploring Burp Suite directly.
You need to keep in mind when you're using Burp Suite Professional to enter your license key when asked. If you do not have it, you can also subscribe to a free trial while doing this process.
Burp Suite Interview Questions for Experienced
15. What is a sniper in Burp Suite?
Sniper is one of the many types of attacks in Burp Suite. It enumerates them one by one in every parameter. This means that it uses a single payload set on one parameter and moves to another. The positions which are not targeted by snipers remain unaffected. This attack might result in an odd number of requests- more than one at a time. One way you can detect this attack is to see if the number of requests generated is the product of the positions and number of payloads.
16. What is an infiltrator in Burp Suite?
Burp Infiltrator can be described as a tool that instruments target applications and websites to facilitate testing with the help of Burp Scanner. Please note that the Burp infiltrator should not be used on systems like production. This is because these systems require correction in either performance or operation. The changes made by the Burp infiltrator might result in defaults like service outage, application errors, poor performance, and several other problems. This eventually changes the overall behavior of the application. And thus, there is even more danger in disclosing sensitive information to anyone who interacts with it. Thus, it is advised to use Burp Infiltrator only for testing purposes.
17. What is a Burp proxy?
We can say that the main element of the Burp Suite workflow is the Burp proxy. It allows the user to drive workflow, intercept, view, and modify all those responses between the browser and target web servers. There is also a term called Burp invisible proxy. When it is enabled, any non-proxy-style usual requests get passed out of the reader's contents, and the targeted host is used for that request.
18. Name some payload types in Burp Suite.
Burp Suite intruder includes the following types of payloads:
- Simple list
- Runtime file
- Recursive grep
- Custom Iterator
- Character substitution
- Case modification
- Illegal Unicode
- Character black
- Numbers\
- Date
- Brute forcer
- Null payloads
- Character robber
- Bit flipper
- Username generator
- ECB block shuffler
- Extension generator
- Copy other payloads
19. How can you attach a Burp Suite to Chrome?
Chrome doesn't have its proxy settings like other browsers. So, here's how you can configure Burp Suite to Chrome:
- Open Chrome
- Click on Customise.
- Selecting settings and then Advanced settings.
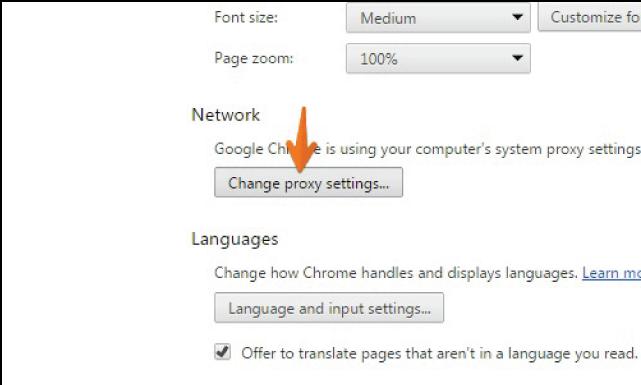
- In Advanced settings, click on Open Computers proxy settings.
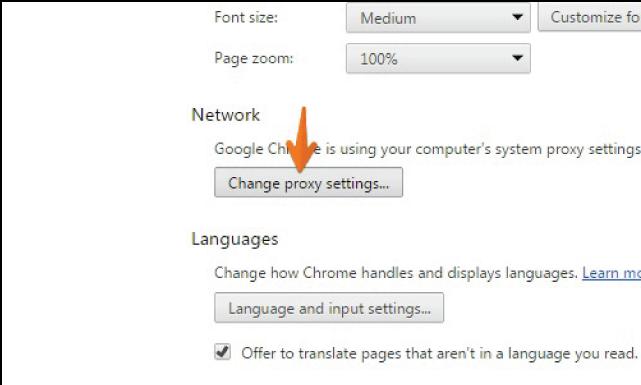
- Change proxy settings
20. Is Burp Suite available on Windows?
Yes! Here's how you can install Burp Suite on Windows:
- Go to the official website of Burp Suite.

- Click on Products.
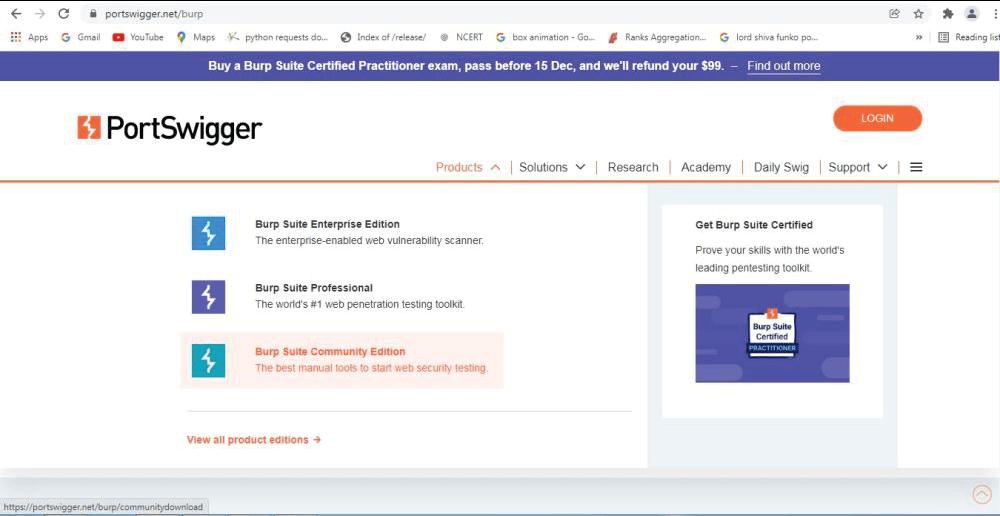
- Choose the Burp Suite Community Edition.
- Choose the option of Go straight to downloads.
- Download the Burp Suite Community Edition.
- Check and run the file in your system.
- It will be loaded in a few seconds.
- Proceed by clicking on next.
- Choose the location of installation that has sufficient memory space.
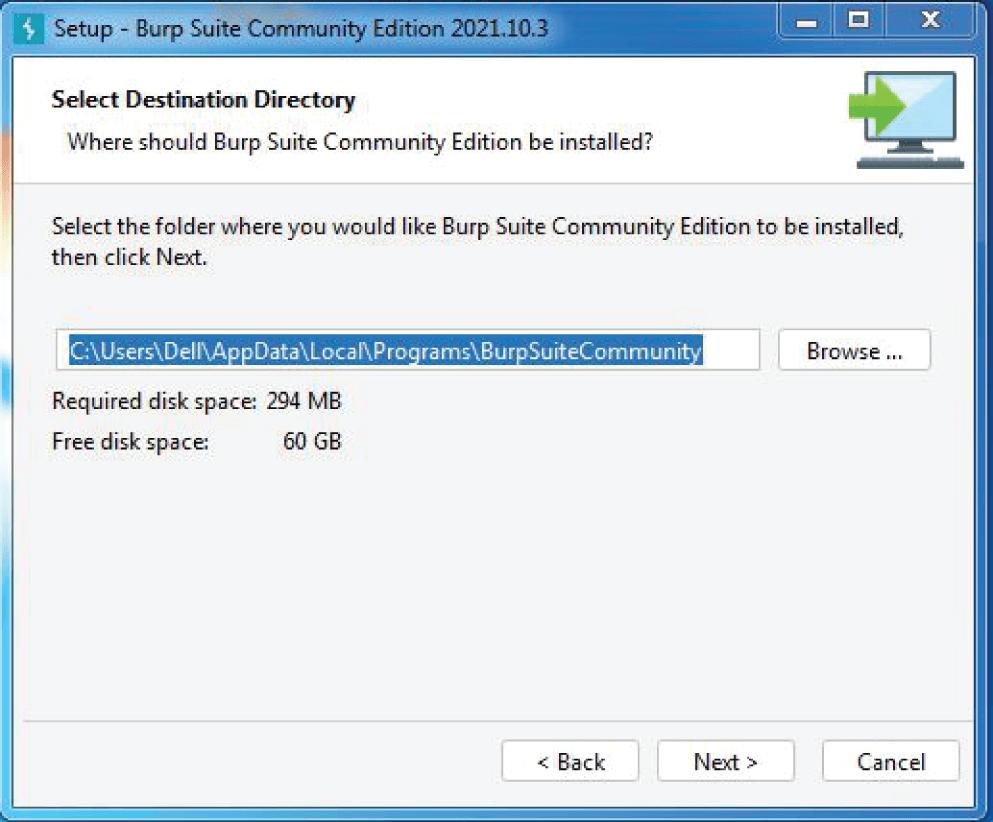
- Click on next.
- Finish the installation process.
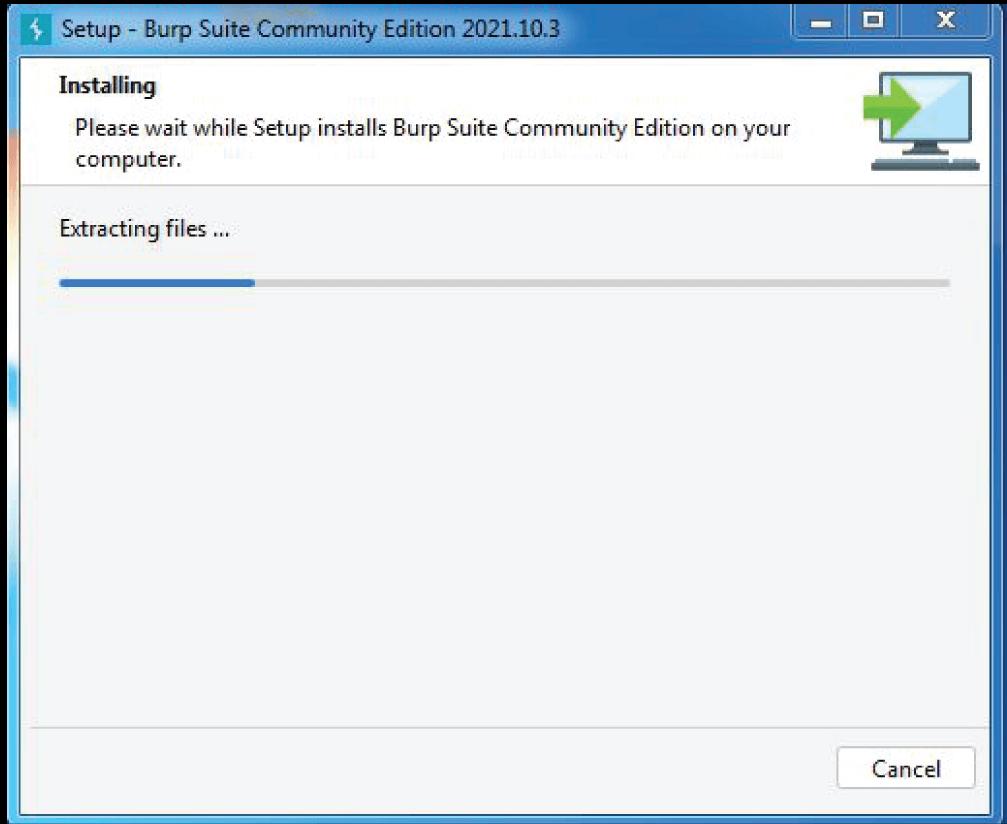
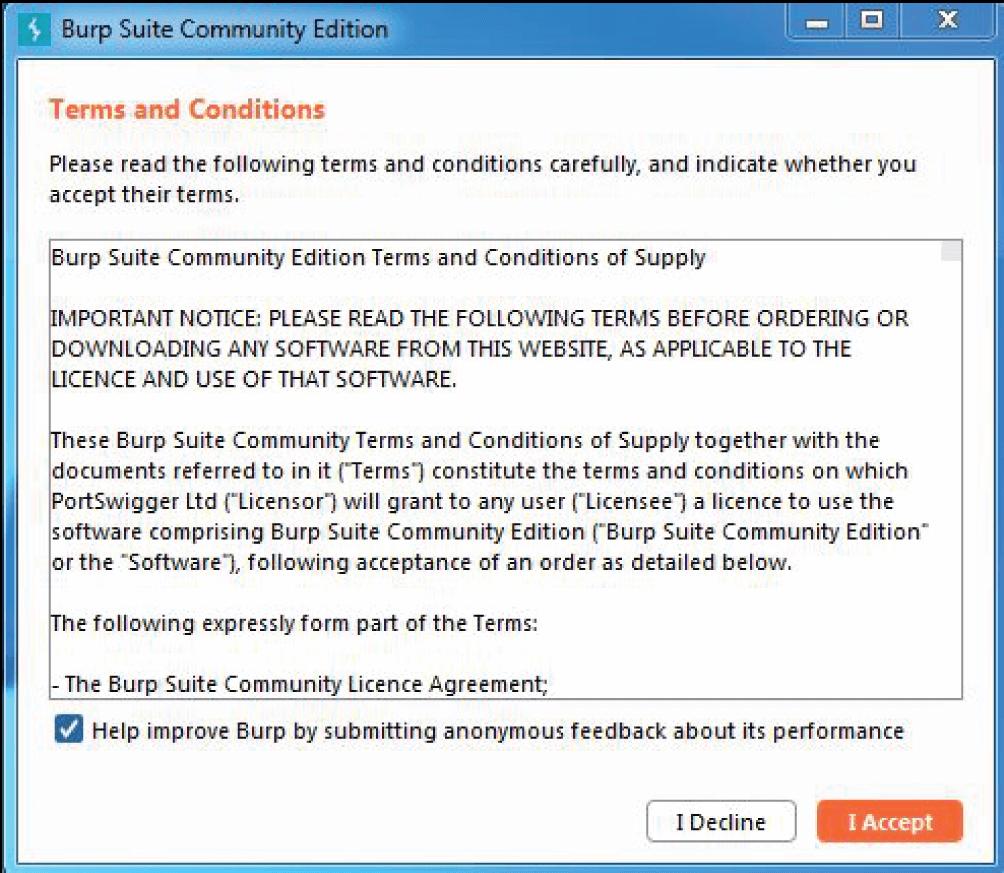
- Accept the terms and conditions.
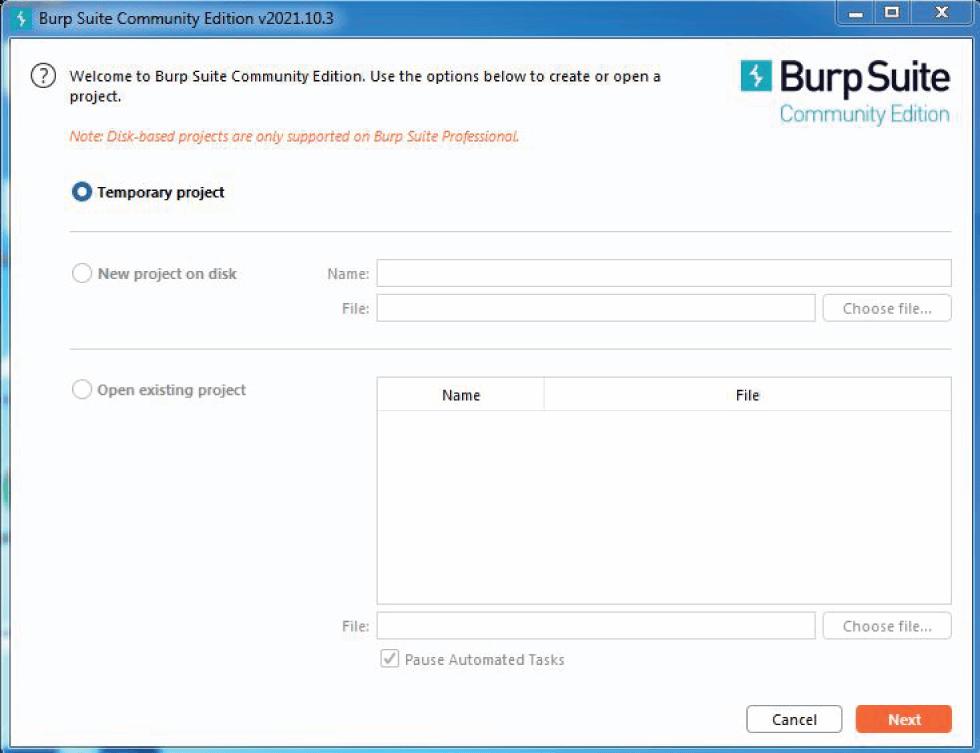
- Choose a temporary project and click Next.
- Choose Use Burp Defaults.
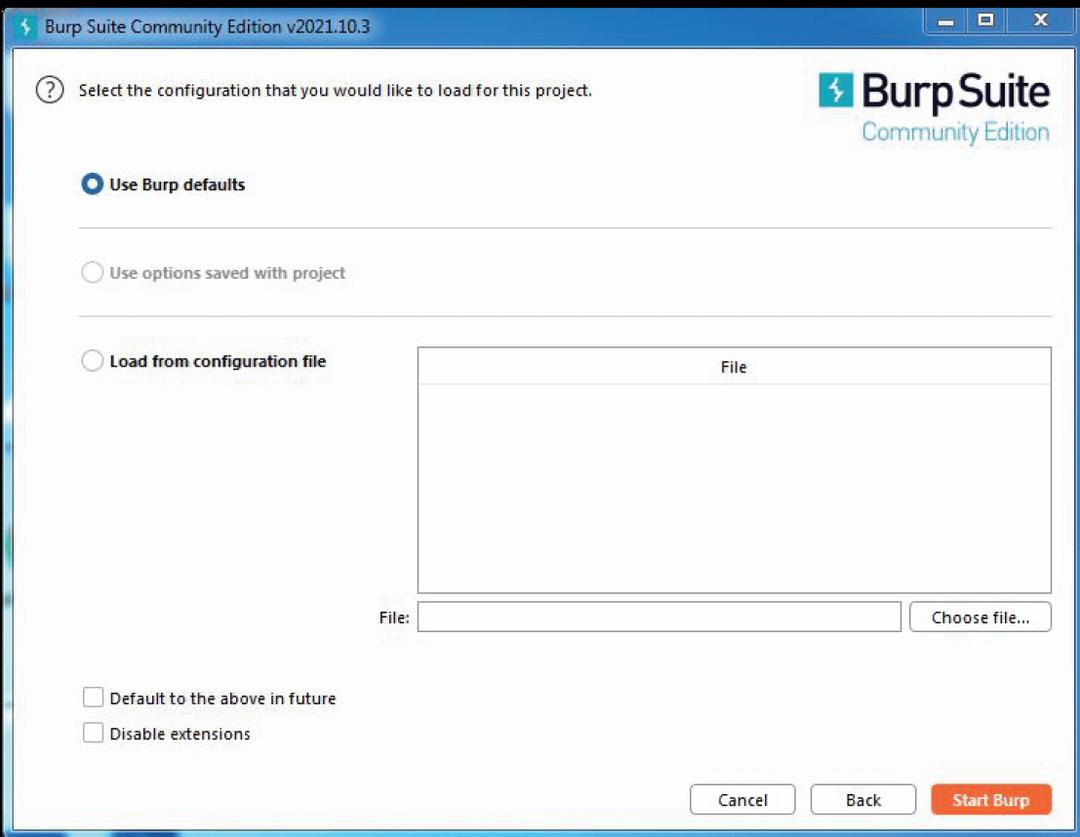
- The installation will be complete.
21. How can you launch a Burp Suite on Linux?
To launch Burp Suite on Linux, look for 'terminal,' 'console,' or 'shell.' Now, for running a . JAR version, make sure that Java is installed. Type- java-version. If installed, a message emerges saying- "1.7.0_67".
22. Why Burp Suite is called the best ethical hacking software?
Burp Suite can be termed as the go-to tool when it comes to ethical hacking. Burp Suite Pro is often called 'the ethical hacker's Swiss Army knife' by ethical hackers. Even after being in the market for quite a while, people are still amazed by its versatility and flexibility. The main focus of ethical hacking is to focus on the target audience, and it is difficult to find a tool that does everything. Its Proxy tools, Reconnaissance tools, automated scanning tools, brute force tools, and limitless expansion options make it the favorite software for hackers. More than 50,000 people from 140 different countries will agree to that.
23. How can you update your Burp Suite tool license?
Here's how you can update your Burp Suite tool license:
- Enter your license key.
- Click next.
- Enter your proxy details.
- Click next.
- Your license will be activated.
- Proceed with the wizard.
- Select copy URL.
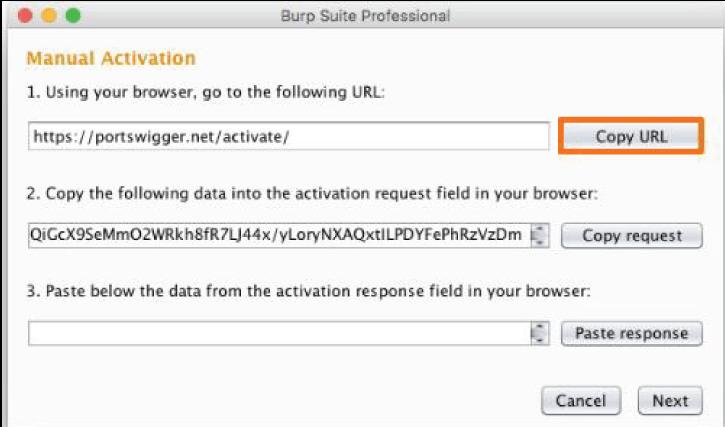
- Paste it into the browser to access the manual license activation page.
- Go back to the wizard.
- Click on Copy request.
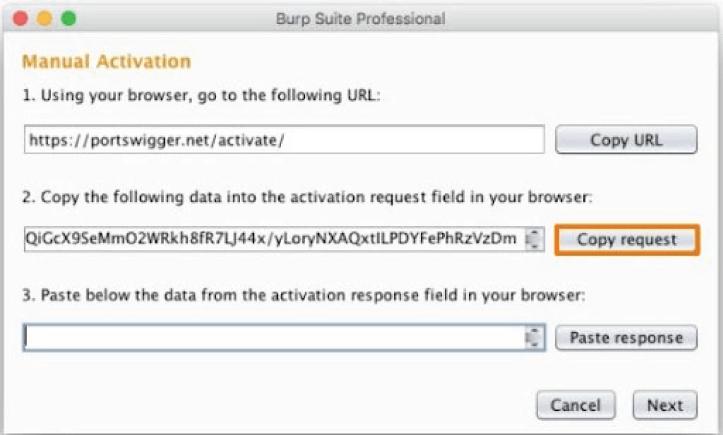
- Return to the page.
- Paste the request in the Activation request field.
- Click send.
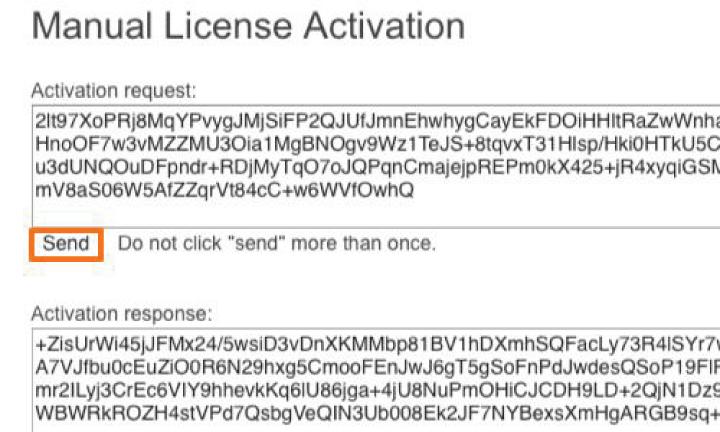
- Select and copy the text that appears.
- Go back to the wizard.
- Paste the response.
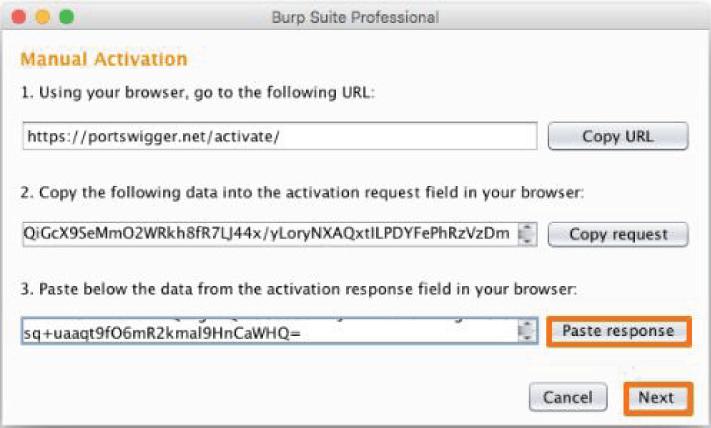
- Click next.
- Click Finish and let the Burp start-up wizard load.
24. How can you install Jython Burp?
Here's how you can install Jython in Burp:
- Download the latest . JAR file of Jython.
- Go to Extender options in the Python Environment category.
- Click on Select File.
- Select the location.
- Open the file.
- The Jython file will be loaded in the Python Environment category.
25. What is the difference between Python and Jython?
We can say that both Jython and Python are two different versions of the same language. Jython is nothing but an implementation of Python in Java. In simpler words, this means that this is like Python is running in a Java Virtual Machine environment. The codes are written like Python, but the extensive features of Java libraries can also be accessed. It is very compatible, versatile, free for use, etc. Jython uses .class as a file extension while Java uses .py. Jython is a cross-platform language but only with the help of Java Virtual Machine.
At the same time, Python is an independent cross-platform language. Jython libraries are written in Java, and Python libraries are written in C. Jython is the basis of web applications, embedded systems, and especially enterprise solutions when we talk about applications. On the other hand, Python is fundamental to Machine Learning applications and scientific computing.
26. Elaborate on Burp Suite Professional Edition.
It is the web security tester toolkit of choice. Users can use it to automate repetitive testing tasks and find vulnerabilities faster. They can also access, create, and share resources such as BApp extensions and use them according to their needs. It is also designed in a manner that helps in increasing scan coverage and minimizing false positives. This helps users, organizations, and network administrators to be more productive while testing and extending their capabilities.
27. Elaborate on Burp Suite Enterprise edition.
We know that Burp Suite is most suitable for enterprises and organizations. This is because it helps them secure their entire portfolio without any resource restrictions or limitations. It allows them to integrate security with development and also in preventing alert fatigue. Enterprises can achieve full visibility of their security posture with this. And lastly, it reduces risks without increasing any costs.
28. Elaborate on Burp Suite Community edition.
Burp Suite Community edition was the first version that was made available to the public right after it was launched. It comes with a basic toolkit that allows the users to experience working on it manually. The toolkit is manual, and it is perfect for beginners and newbies. It includes all the fundamental tools and demos.
| Check Out: Burp Site Tutorial |
Frequently Asked Questions in Burp Suite Interview:
1. What is the Burp Suite tool?
Burp Suite is a graphical tool used to perform security tests of different applications on the web. It consists of tools that work together to support the entire testing process. It also works as an integrated platform that takes care of your application right from the initial mapping of your application, analyzing it, and finding vulnerable things and threats that exploit the security of your application.
2. What is the Burp Suite tool used for?
As mentioned above, it is used for testing different applications on the web. Organizations make the most of it by performing automated scans on their websites and applications to find errors immediately. This saves their time, effort, and energy and cuts off the manual work to a larger degree. Burp Suite is the most preferred tool for optimizing and analyzing.
3. What are the features of the Burp Suite tool?
There are many features of the Burp Suite tool apart from performing security tests and vulnerability scanning. Some of them are:
- Assessment of your target application
- Assessment of randomness in your application.
- Management of data.
- Storing the data in the target site map
- Functions of filtering and annotation
- Finding and exposing hidden attack surface
- Modifying and speeding up granular workforces
- Stable and lightweight
- Supported in cross-platform
- Well-designed user interface
- Crawling websites and applications
- Customize attacks
4. Is Burp Suite easy to use?
Burp Suite is considered a potent tool and is a preferred choice for businesses and organizations because of being easy to configure. Even someone without a lot of experience can use it for multiple testing processes. It does not take much time and is super effective in its functioning. SQL injection operations which are believed to be extremely difficult, can be carried out with the help of Burp Suite.
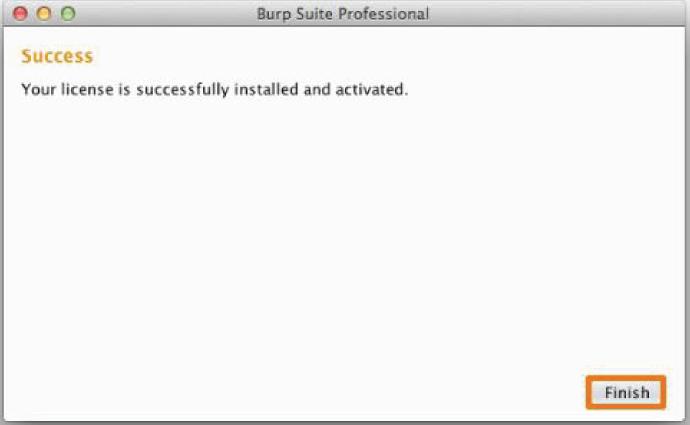
5. How to install the Burp Suite CA certificate on Chrome?
Burp Suite CA certificate can be installed on both Firefox and Chrome. Following are the steps for installation on Chrome-
- Open Menu- click Settings- Security- Manage certificate.
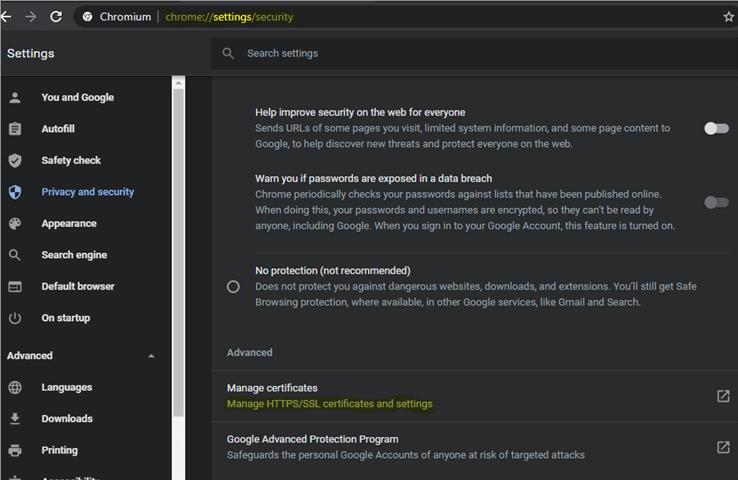
- Next open Certificate Dialog Box, then Clock on the Trusted Root Certification Authorities tab and click Import.
- Now Click on the Browse button and select cacert.der from the downloaded file's location.
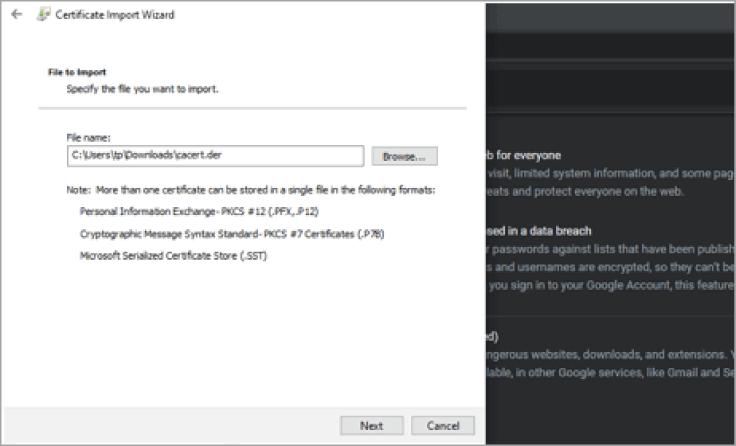
- From the given options, select the first- Place all certificates in the following store and then click on Trusted Root Certification Authorities.
- Then click on Next.
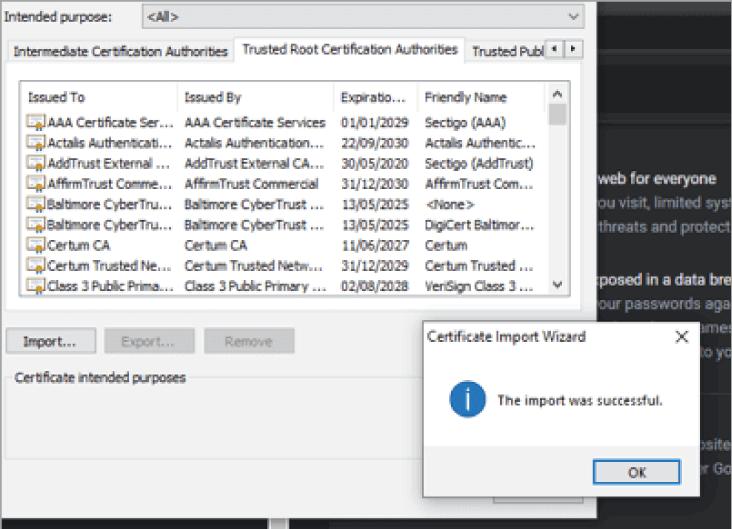
- Lastly, close Chrome, restart it and confirm the running of Burp Suite. You can now go and browse any HTTPS application and note the response. You will no longer be receiving any security notification after this.
6. Why is the Burp Suite tool popular?
The Burp Suite tool is the number one for web security testing. Its popularity is evident because it uses over 60000 tests. One of the reasons is that it is accessible to everyone and is ready to nurture the next generation of security professionals. Another point that makes it the leading choice is the huge community base. It continues to launch new extensions with the rapid technological advancement and according to the industry demands.
7. Is Burp Suite safe to use?
Yes! Burp Suite is safe, reliable, and secure. It also allows the users to proxy all the requests sent and received on the web without fail. This again contributes to making it a loved choice. A community of over 15000 organizations testifies to this fact. Various surveys are conducted over time, and everyone agrees that Burp Suit is a best-in-class software.
8. Is Burp Suite open-source?
Burp Suite allows its user's free trials for the first time. But the Burp Suit professional version cost starts from 299$. Those who are licensed users can upgrade to their new versions without any extra charge. This price has remained constant for quite some time despite being majorly updated. At the same time, it only gives permissions to certain domains. You cannot use it on those that you don't own. In this way, it takes care of your security and legality.
9. Who owns Burp Suite?
Burp Suite was developed by a company called Portswigger. It is also commonly known as Portswigger Web Security. It has always been known for its three editions, i.e., the Community edition, which is free of charge, the Professional edition, and an Enterprise edition which gives the option of a free trial before purchase. It now contains extensive options of a spider, a repeater, a decoder, an extender, etc.
10. When was Burp Suite created?
The founder of Burp Suite or Portswigger is Dafydd Stuttard. He wrote the first version of Burp between 2003 and 2006. In August, it was officially launched in the year 2005 with all four of its tools, i.e., Burp Proxy, Sock, Spider, and Repeater.
Conclusion:
These were some of the Burp Suite interview questions that could be asked in your next interview. Remember that it is very useful software for every company, enterprise, and operator now. And it opens the doors of opportunities in many ways. You cannot miss a chance to grab them, and this article will make you even well-versed with the software. Keep practicing, and we wish you good luck!
 On-Job Support Service
On-Job Support Service
Online Work Support for your on-job roles.

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs:
- Pay Per Hour
- Pay Per Week
- Monthly
| Name | Dates | |
|---|---|---|
| Burp Suite Training | Jun 06 to Jun 21 | View Details |
| Burp Suite Training | Jun 09 to Jun 24 | View Details |
| Burp Suite Training | Jun 13 to Jun 28 | View Details |
| Burp Suite Training | Jun 16 to Jul 01 | View Details |

















