- 6 Hot And In-Demand Tech Areas In 2024
- How To Forward Your Career With Cloud Skills?
- Top 7 On-Demand IT Certifications
- Most In-demand Technologies To Upskill Your Career
- Top 10 Hottest Tech Skills to Master in 2024
- Top Skills You Need to Become a Data Scientist
- Groovy Interview Questions
- Facets Interview Questions
- Crystal Reports Tutorial
- VAPT Interview Questions
- Flutter Tutorial
- Saviynt VS Sailpoint
- Flutter vs Xamarin
- PingFederate Interview Questions and Answers
- Dart vs Javascript : What's the Difference?
- Terraform Private Registry
- Cylance Interview Questions and Answers
- Sophos Interview Questions and Answers
- Top Camunda Interview Questions
- NUnit Interview Questions and Answers
- Impala Interview Questions and Answers
- ETL Tutorial
- Ionic Interview Questions
- Grafana Tutorial
- What is VAPT? - A Complete Beginners Tutorial
- SnapLogic Interview Questions
- Saviynt Interview Questions
- What is PingFederate? - A Complete Beginners Tutorial
- SnapLogic Tutorial
- Grafana Interview Questions
- RHCE Interview Questions and Answers
- Web Services Interview Questions
- Domo Interview Questions and Answers
- Terraform Interview Questions
- What is Sophos? | Sophos Turorial for Beginners
- Top Servlet Interview Question And Answers
- NLP Interview Questions and Answers
- Microsoft Intune Interview Questions
- Top XML Interview Questions And Answers
- Tosca Commander
- Katalon vs Cypress
- SQLite Tutorial
- Tosca Tutorial - A Complete Guide for Beginners
- Xamarin Interview Questions and Answers
- UiPath vs Automation Anywhere - The Key Differences
- OpenShift Interview Questions
- What is Katalon Studio - Complete Tutorial Guide
- Kronos Interview Questions
- Tosca Framework
- Mendix Interview Questions
- Power Platform Interview Questions
- Burp Suite Interview Questions
- What is Mendix
- What is Terraform ?
- Burp Suite Alternatives
- Dart vs Kotlin
- What is Kronos?
- ES6 Interview Questions
- Entity Framework Interview Questions
- COBOL Interview Questions
- Express JS Interview Questions
- OSPF Interview Questions
- LINQ Tutorial
- CSS3 Interview Questions and Answers
- Auth0 Tutorial
- MS Access Interview Questions
- What is SPARQL - A Complete Tutorial Guide
- ExpressJS Tutorial
- UML Tutorial
- HTML vs XML
- Cypress vs Jest
- Impacts of Social Media
- OWASP Interview Questions
- Security Testing Interview Questions
- OpenShift vs Docker
- ES6 Tutorial
- Spark SQL Interview Questions
- Spark SQL Tutorial
- What is OWASP?
- AppDynamics Interview Questions
- Dynatrace Interview Questions
- Rest Assured Tutorial
- New Relic Interview Questions
- REST API Tutorial
- Datadog Interview Questions
- Rest API Interview Questions
- Rest Assured Interview Questions
- PTC Windchill Interview Questions
- Easiest Tech Skills To Learn
- Python SQLite Tutorial - How to Install SQLite
- Datadog Tutorial - Datadog Incident Management
- What is AppDynamics - AppDynamics Architecture
- RabbitMQ Interview Questions And Answers
- What is Dynatrace
- Datadog Vs Splunk
- Web Developer Job Description
- JP Morgan Interview Questions
- Types of Corporate Training
- Benefits of Corporate Training
- What is Corporate Restructuring?
- Blended Learning in Corporate Training
- What is Corporate Level Strategy?
- Flutter Projects and Use Cases
- How to Become a Web Developer
- How To Install Keras?
- How to Install Flutter on Windows?
- How to Install Cypress on Windows?
- How to Become a Computer Scientist?
- How to Install Katalon Studio in Windows
- How to Become a Programmer
- OWASP Projects and Use Cases
- How to Install Sophos?
- Workato Tutorial
- Workato Tutorial - What is Workato?
Burp Suite is the automation-based security software used in web applications. With Burp Suite, you can identify threats and vulnerabilities in applications. Not only this, it is considered one of the best software to fight against cyberattacks because of its powerful scanning tool, known as Burp Scanner. Using this tool, Burp Suite scans web applications faster and automatically. As a result, it offers a wide range of benefits such as good reliability, scalability, flexibility, and integration.
Considering other key technological aspects of Burp Suite software, it accelerates workflows with 200+ extensions, performs faster brute-forcing and fuzzing attacks, and conducts deeper manual testing. Free plugins are the strength of Burp Suite, which is used to achieve extensibility when you use this software. Apart from all these, Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) are the two methodologies used in testing web applications in Burp Suite.
Let’s read on to explore more about Burp Suite in this tutorial. This tutorial covers the following topics.
Burp Suite Tutorial Table of Content:
What are the Vulnerabilities that may occur in Web Applications?
Cross-Site Scripting (XSS):
This vulnerability allows attackers to access application data and carry out all the activities that users can do. And it allows avoiding origin policy designed to segregate different websites from each other. This skipping is carried out by manipulating the victim’s web application by sending malicious JavaScript to users. So, when the malicious code runs on the browser, it compromises the application's security. Know that there are three types of XSS vulnerabilities – Reflected XSS, Stored XSS, and DOM-based XSS.
SQL Injection:
In this type of vulnerability, attackers interfere with the queries generated by an application to its database. Next, the attacker accesses the data and modifies or changes the content in the database. For example, the attacker can access sensitive data such as passwords, credit cards, etc. Also, this vulnerability could compromise the server and make a DoS attack. Know that following are a few examples of SQL injection – retrieving hidden data, UNION attacks, subverting application logic, examining databases, and blind SQL injection.
Cross-Site Request Forgery (CSRF):
It is the type of security vulnerability capable of diverting users to do some other activity that the user does not actually intend. Like XSS vulnerability, this one also avoids origin policy and allows attackers to gain control over the victim’s user account. CSRF can occur in three scenarios: Cookie-based session handling, a relevant action, and no unpredictable request parameters.
XML External Entity Injection:
It is also known as XXE, which is a web security vulnerability. It allows attackers to interfere with the processing of XML data of an application. Also, it allows attackers to access the server file system and interact with the back-end or external systems. Besides, it leads to server-side forgery attacks.
Directory Traversal:
This web security vulnerability is also called ‘file path traversal’. This vulnerability allows attackers to access arbitrary files in the server running an application. The arbitrary files may include application code and data, crucial OS files, and credentials of back-end systems. Attackers can write on arbitrary files and change the behaviour of the server.
Server-Side Request Forgery (SSRF):
It is another type of SSRF vulnerability. It allows attackers to induce applications to make requests to unintended locations. In other words, it allows attackers to make unauthorised access to data and make arbitrary command execution. Following are the types of SSRF attacks – attacks against the server and attacks against back-end systems. Note that you can overcome these attacks by using white-based input filters, bypassing SSRF filters via open redirection, and blind SSRF vulnerabilities.
| Looking forward to a career in a Software Automation Testing Courses? Check out the "Burp Suite Training" and get certified today |
Why Burp Suite?
As mentioned earlier, Burp Suite is one of the technically sound web application security software. Now, let's discuss the reasons for the same.
Automated Scanning:
With multi-AST technology, Burp Suite helps overcome friction in testing and supports streamlining software development. Scanning with configurable scan routines identifies vulnerabilities in web applications. As a result, the Signal to Noise Ratio (SNR) can be increased to an optimum value. In addition, Role-Based Access Control (RBAC) and Single Sign-On (SSO) ensure the security of applications while scanning.
Penetration Testing:
Compared to manual testing, automated testing provides many benefits. This way, penetration testing is one of the automated testing methods, which performs testing by penetrating systems deeply. Know that penetration testing uses the method known as fuzzing. In the same line, Burp repeater is one of the burp suite tools designed to repeat HTTP(S) requests many times. And it allows testers to edit requests manually.
| Related Article: What is Vulnerability Assessment and Penetration Testing (VAPT) |
Bug Bounty Hunting:
Starting with Burp Proxy, individual web application components are allowed for testing in this method. After that, these components will be sent to bug hunting tools to detect vulnerabilities. Following is the list of popular bug hunting tools of Burp Suite – Burp proxy, Burp scanner, Site map, Burp Repeater, Content Discovery, Burp Extender API, and Burp Intruder.
DevSecOps:
Know that automation increases the chances of identifying more bugs and supports to resolve them quickly. Mainly, it ensures security while developing software. For example, integration with CI/CD pipeline ensures security in the software developing environment. DevSecOps prioritises security based on the threat level and helps to remove bottlenecks securely.
Compliance:
Burp Suite works against data breaches in web applications, reviews more websites, and takes the next course of action to reduce risks. As a result, it supports ensuring complete security over all the web applications and generates real-time reporting. Besides, it minimises the cost of external tools significantly. Note that Burp Suite ensures the security compliances for PCI DSS, NIST 800-53, HIPAA, OWSAP Top10, and GDPR.
What is Burp Scanner?
Burp Scanner is a powerful pen-testing tool used in Burp Suite to find various vulnerabilities in web applications. It allows scanning for individuals and groups, and saves custom configurations. Here, Burp Scanner's attack engine is a powerful ally. And it automates the routines of pen-testers, thankfully.
Why Burp Scanner?
Burp Scanner is a powerful security testing tool for web applications. Let’s know the reasons for the same below:
Crawl Engine:
Burp Scanner Crawl Engine identifies obstacles like CSRF tokens, stateful functionalities, and overloaded or volatile URLs. This feature helps to scan JavaScript-heavy applications very quickly.
Advanced Algorithms:
Burp Scanner uses advanced crawling algorithms to build profiles as a tester does. This scanner can handle dynamic content, API definitions, unstable internet connections, and many web applications.
Finger Printing Techniques:
Burp Scanner uses fingerprinting techniques that support avoiding sinkholes in requests. It helps reduce the number of requests during the testing, thereby increasing the scanner's performance and saving enough time. Also, it provides increased SNR producing a low rate of false positives.
Dynamic Scanning:
Burp Scanner conducts OAST – Out of band Application Security Testing. This testing supports identifying the interaction between the target and the external server. This dynamic scanning can identify the vulnerabilities such as SQL injection and blind SSRF.
The Products Offered by Burp Suite:
The following are the products offered by Burp Suite. Here’s the list:
- Burp Suite Enterprise Edition
- Burp Suite Professional Edition
- Burp Suite Community Edition
What is Burp Suite Enterprise Edition?
The Burp Suite enterprise edition carries out automated vulnerability scanning for web applications. This edition is bundled with scheduled scans, intuitive remediation advice and reporting, and CI/CD integrations. The teams such as AppSec, CISO and CTO, software development, and AppSec centres of excellence can use this software. Making concurrent scanning in multiple applications is possible in this software.
Why Burp Suite Enterprise Edition?
Burp Suite enterprise edition is bundled with many good features. That is why users prefer enterprise edition to secure their web applications.
Scanning Features:
Thanks to Burp Scanner, which deeply identifies vulnerabilities in web applications. For this, Burp Scanner uses the embedded chromium browser. This way, automated OAST supports conducting dynamic scans and identifying vulnerabilities with high accuracy. With ‘point-and-click’ scanning, Burp Scanner allows an easy scanning setup.
And it can be done through a URL or Trigger via CI/CD. Primarily, fast crawl and critical vulnerability are performed easily and quickly. And you can scan modern web applications using the methods such as JavaScript scanning and API security scanning. Nonetheless, you can make automatic scanning daily, weekly, and monthly using Burp Scanner.
Integration Features:
Burp Suite enterprise edition can be integrated with other vulnerability management systems and bug tracking systems. Also, it can be integrated with existing systems for scanning web applications and obtaining results with REST API. With GraphQL-based API, you can integrate Burp Suite with the CI platform and functions. Know that configurations of this edition can be integrated with the automated Burp Suite professional environment.
Deployment:
With an interactive installer, standard deployment is achieved in this Burp Suite enterprise edition. Not only interactive installer but Kubernetes deployment can also be performed in this edition using Helm Chart.
Dashboard and Reporting Features:
When considering the dashboard in the enterprise edition, it helps to know the status of all security parameters of web applications in one place. For example, you can understand the severity of bugs or types of bugs through dashboards. Also, the dashboard shows scan history, which provides metrics about bugs and types of issues.
Considering the reports generation of this Burp Suite edition, it sends reports to teams through email. And it allows you to export bespoke HTML reports to destination sources. Moreover, ‘Security Poster Graphing’ helps to know the visual image of security parameters in web applications. In the same line, ‘Aggregated Reporting’ categorises security issues based on their class.
What is Burp Suite Professional Edition?
This Burp Suite professional edition also conducts penetration testing, bug bounty testing, and manual testing. In fact, this software uses Burp extensions (BApps) for customising workflows. And it will be supportive for frontline AppSec engineers, bug bounty hunters, and penetration testers to perform scanning web applications effectively.
Why Burp Suite Professional?
The Burp Suite professional edition is faster and enriched with many fantastic features than the enterprise edition. Let's discuss them in the following in detail:
Manual Penetration Testing:
Basically, a penetration test is performed by creating a Burp proxy for intercepting HTTP(S) requests. It allows you to modify and reissue individual HTTP(S) and web socket messages. And it shows responses and analyses by which you can speed up workflows.
The Burp tools for penetration testing include Burp Scanner, Burp Repeater, Burp Intruder, and Burp Sequencers. While conducting penetration testing, target data is aggregated and stored in a target site map. Then, invisible content and hidden attacks are identified for the next course of action. What’s more! Burp penetration tools control ‘clickjacking attacks’ with special tools.
Advanced Automated Attacks:
By performing faster automated attacks such as brute-forcing and fuzzing, this Burp Suite edition analyses the behaviour of web applications deeply. You can make these automated attacks by deploying custom sequences of HTTP requests. Also, this edition carries out ‘proof of concept’ attacks and ‘deep manual testing'; as a result, it identifies issues like XSS.
Burp Suite performs active scans through URLs; not only that, Burp Suite identifies the location of issues too. Moreover, you can achieve fine-grained control over web applications by running ‘point and click’ scans in this edition.
Moreover, this Burp Suite professional edition helps achieve a high SNR through friction-free OAST. The hybrid AST and built-in JavaScript analysis engine support identifying flaws in client-side attack places. This edition can get custom descriptions and remediation suggestions for every bug. Besides, you can customise your audits, fine-tune insertion points, and skip specific checks.
Productivity Tools:
Burp Suite professional edition comes with a few productivity tools that support effective scanning of web applications.
Deep-dive Message Analysis:
The feature-rich HTTP editor of Burp Suite professional edition shows the details such as follow-up, reference, analysis, discovery, and remediation.
Auto-save:
This edition allows you to auto-save all projects on storage and add configurations to the pre-saved projects.
Printing Codes:
In this edition, you can print codes using the following formats – JSON, CSS, XML, JavaScript, and HTML.
Scan Reporting:
This edition allows you to generate HTML/XML reports with issues and evidence.
Data Transformation:
You can perform data encoding and decoding with multiple built-in operations in this software.
What are the Extensions used in Burp Suite Professional Edition?
Burp Suite professional comes with many extensions in which each one serves its unique purpose. BApp Store is where you can find over 250 extensions used by Burp users. Let’s go through the listicles of a few popular extensions as follows:
Extender API: This extension provides universal adaptability.
Logger++: It provides in-depth vulnerability details with an accessible table where vulnerability details are neatly provided.
Authorise: This extension helps to perform repeat requests while testing authorisation vulnerabilities by which you can save time significantly.
Turbo Intruder: With the support of a custom HTTP stack, this extension manages thousands of requests in a second
J2EE Scan: It identifies vulnerabilities and hunts bugs in Java-based applications.
Upload Scanner: It supports uploading and testing multiple file type payloads.
Authmatrix: It helps to identify access-level vulnerability authorisation checks
Param Miner: It helps to identify unkeyed inputs and is capable of guessing up to 65000 parameter names per second.
Backslash Powered Scanner: It allows you to identify research-grade bugs and supports bridging human intuition and automation.
What are the Key Features of Burp Suite Community Edition?
This community edition is the free version of web security testing. This edition has the features such as HTTP/Web sockets proxy and scan history. Know that Repeater, Sequencer, Comparer, and Decoder are the essential tools used in this edition. Besides, Burp Intruder plays a crucial role in this edition.
How to Get Started with Burp Suite?
Getting started with Burp Suite professional and community edition is achieved in the following five steps:
- Download and install Burp Suite Software
- Intercept HTTP traffic with Burp Proxy
- Modify requests in Burp Proxy
- Reissue requests with Burp Repeater manually
- Run the first scan
1. Download and Install:
- Step 1: You can download the latest version of Burp Suite professional and community edition using the links provided on the PortSwigger website.
- Step 2: Now, run the installer and open the Burp Suite software.
2. Intercepting HTTP traffic with Burp Proxy:
Burp Proxy allows you to intercept HTTP requests and responses in this stage. These requests are usually sent between Burp’s browser and the target server.
- Step 1: launching Burp’s Browser: Select the 'proxy' and 'intercept' tab in the Burp Suite window. And select ‘Intercept is on’. Now, click ‘Open Browser’ by which you can launch Burp’s browser.
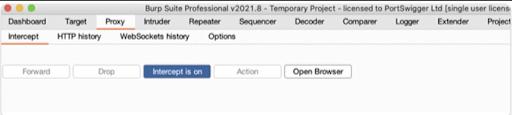
- Step 2: Intercepting a request: Now, use Burp’s browser and try to load a webpage, but you can notice that the target site is not yet loaded. It happens because the ‘intercept’ tab is ON. Burp’s Proxy intercepted the HTTP request before it reaches the target server. To view the details of intercepted requests, you can click the ‘intercept’ tab.
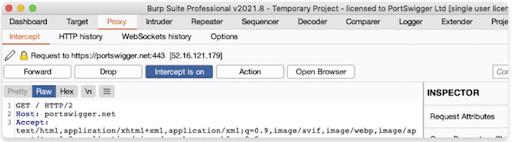
- Step 3: Forward the Request : If you want to load the page in the Burp browser, click the forward button. This action will allow you to connect with the target server and open the required page.
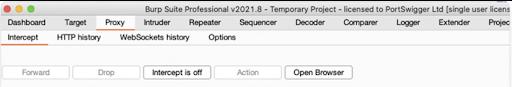
- Step 4: Switching off the interception : If you don’t want to intercept the requests, you can switch off the ‘intercept on’ button. After that, it will show you that ‘intercept is off’
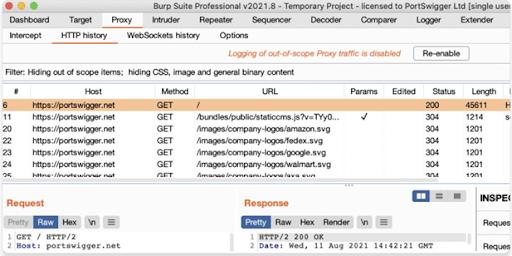
- Step 5: Viewing the HTTP history : To view the HTTP history, click the proxy tab and HTTP history. So, you can see all the HTTP traffic that happens in the Burp browser. This history will show you the requests sent while ’intercept is on' and the history while 'intercept is off'. If you click a specific HTTP request from the history, you can see the details of the response from the server.
3. Modify HTTP requests with Burp Proxy:
- Step 1: Accessing the vulnerable website : First of all, make sure that interception is switched off. Next, use the following link to open ‘Lab’ in Burp Suite to modify requests. After opening the lab page, you can see a fake shopping website.
https://portswigger.net/web-security/logic-flaws/examples/lab-logic-flaws-excessive-trust-in-client-side-controls- Step 2: Logging in to the shopping account : Now, open ‘My account’ using the following credentials.
User Name: wiener; Password: peter - Step 3: Finding a product to buy : Go to the ‘home’ page and select a product to buy.
- Step 4: Going through the ‘add to cart’ function : After switching on the intercept, identify the POST/CART request from the intercept tab.
- Step 5: Modifying the Request : Now, you can make changes to the page; the change could be either price or quantity. For example, see the below image.

- Step 6: Exploit the Vulnerability : Now, you can open the page in Burp Browser and see the modification made for the product.
4. Reissuing Requests with Burp Repeater:
- Step 1: Launch Burp’s Browser : Like you have done in the earlier step, you can open ‘Lab’ in Burp’s browser. And then, you can open the fake website.
- Step 2: Browse the Target Site : Now, explore the site by navigating through a few pages
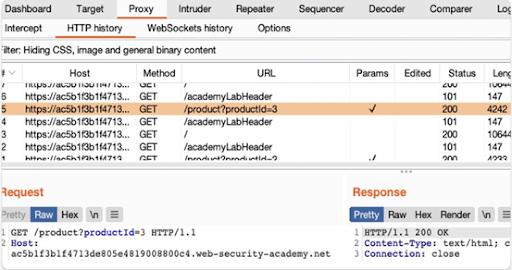
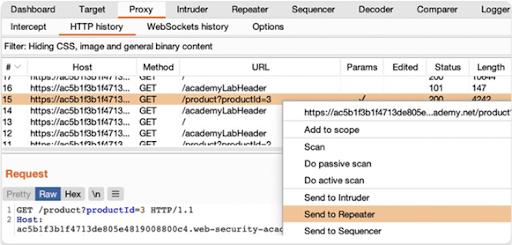
- Step 3: Study the HTTP History and Identify a Request : Now, you can open HTTP history in the proxy tab and see the list of requests. Then, identify a request and find its GET/Product request with a product ID. For example, see the below image to identify a request and GET/product request.
- Step 4: Sending the Request to Burp Repeater : Right-click on the GET/product request and select the ‘send’ to repeater, and you can view the list of requests in the repeater tab.
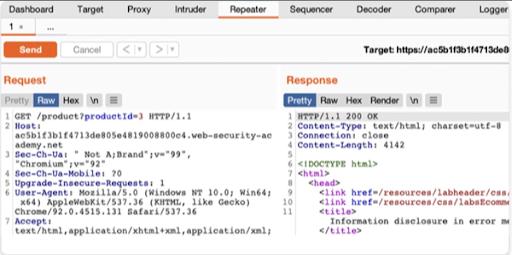
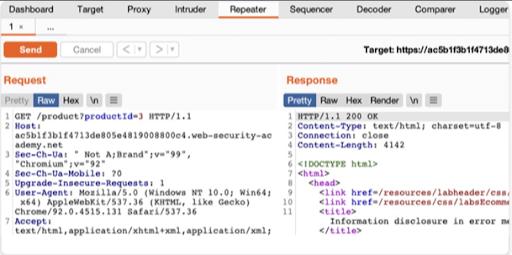
- Step 5: Issuing the Request and Viewing the Response : Now, you click the ‘send’ button to issue the request and see the response from the server, as shown below. You can resend this request many times and get the responses.
5. Running the First Scan using Burp Suite
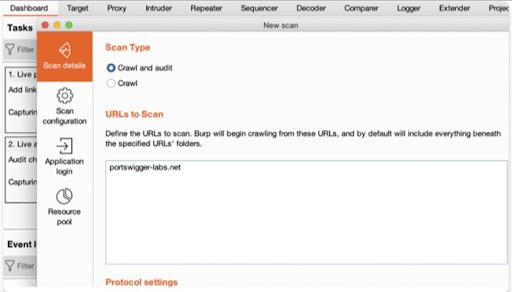
- Step 1: Open the Scan Launcher : Open the dashboard tab and click the ‘New Scan’ button. When the Scan Launcher dialog box opens, copy and paste the URL to be scanned. Then click ‘OK’ to launch the scan, so Burp Scanner will start scanning now.
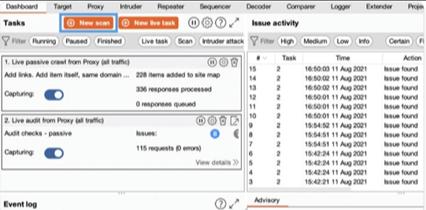
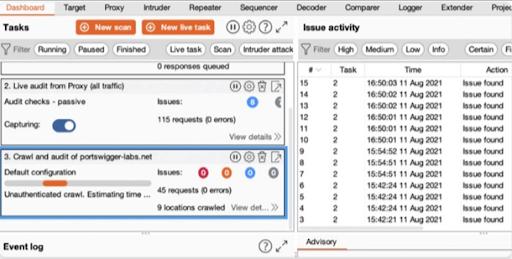
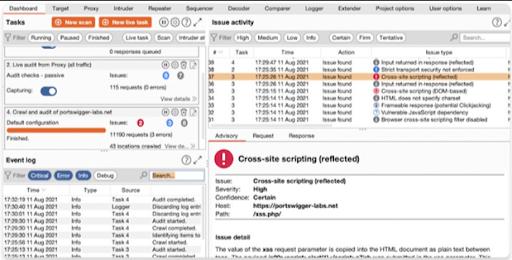
- Step 2: View the Crawling in action : In Burp Window, select the ’target’ and ‘site map’ tab entry, where you can find the new entry for the URL. After a few minutes, Burp Scanner will list the identified issues in the dashboard. If you open the advisory tab, the advisory tab will show all the key information about issues, detailed descriptions, and remediation advice.
Benefits of Burp Suite:
Here, you can find all about the benefits of Burp Suite software. Let’s look at them in detail.
Automated Processes: With automated processes, you can find more vulnerabilities in web applications by scanning.
Better Reporting: Scanning can be done at scale with the support of HTML and XML scan reports, and intuitive dashboards display detailed scan reports.
Robust Integration: Burp Suite can be integrated with ticketing systems. And CI/CD feedback will be helpful for developers.
Increased Productivity: With automated tools and workflows, you can speed up the testing of web applications. You can get expert remediation advice and increase productivity by managing busy workloads.
Vast Extensions: Burp Suite offers customisation options for pro-specific BApps and robust APIs, which in turn increases the efficiency of scanning.
Conclusion:
Let's wrap off! We hope you must have imbibed some good knowledge on different vulnerabilities, Burp Suite editions, Burp Scanner, and many more through this tutorial. You must have got a concrete idea of how to safeguard your web applications with burp suite software. In addition to all these, you might have understood how to get started with burp suite software. Keep reading this tutorial multiple times because – at the end of the day, all that matters is not what you have read but what stays on your mind.
 On-Job Support Service
On-Job Support Service
Online Work Support for your on-job roles.

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs:
- Pay Per Hour
- Pay Per Week
- Monthly
| Name | Dates | |
|---|---|---|
| Burp Suite Training | May 26 to Jun 10 | View Details |
| Burp Suite Training | May 30 to Jun 14 | View Details |
| Burp Suite Training | Jun 02 to Jun 17 | View Details |
| Burp Suite Training | Jun 06 to Jun 21 | View Details |

















