- 6 Hot And In-Demand Tech Areas In 2024
- How To Forward Your Career With Cloud Skills?
- Top 7 On-Demand IT Certifications
- Most In-demand Technologies To Upskill Your Career
- Top 10 Hottest Tech Skills to Master in 2024
- Top Skills You Need to Become a Data Scientist
- Groovy Interview Questions
- Facets Interview Questions
- Crystal Reports Tutorial
- VAPT Interview Questions
- Flutter Tutorial
- Saviynt VS Sailpoint
- Flutter vs Xamarin
- Dart vs Javascript : What's the Difference?
- Terraform Private Registry
- Cylance Interview Questions and Answers
- Sophos Interview Questions and Answers
- Top Camunda Interview Questions
- NUnit Interview Questions and Answers
- Impala Interview Questions and Answers
- ETL Tutorial
- Ionic Interview Questions
- Grafana Tutorial
- What is VAPT? - A Complete Beginners Tutorial
- SnapLogic Interview Questions
- Saviynt Interview Questions
- What is PingFederate? - A Complete Beginners Tutorial
- SnapLogic Tutorial
- Grafana Interview Questions
- RHCE Interview Questions and Answers
- Web Services Interview Questions
- Domo Interview Questions and Answers
- Terraform Interview Questions
- What is Sophos? | Sophos Turorial for Beginners
- Top Servlet Interview Question And Answers
- NLP Interview Questions and Answers
- Microsoft Intune Interview Questions
- Top XML Interview Questions And Answers
- Tosca Commander
- Katalon vs Cypress
- SQLite Tutorial
- Tosca Tutorial - A Complete Guide for Beginners
- Xamarin Interview Questions and Answers
- UiPath vs Automation Anywhere - The Key Differences
- OpenShift Interview Questions
- What is Katalon Studio - Complete Tutorial Guide
- Kronos Interview Questions
- Tosca Framework
- Burp Suite Tutorial
- Mendix Interview Questions
- Power Platform Interview Questions
- Burp Suite Interview Questions
- What is Mendix
- What is Terraform ?
- Burp Suite Alternatives
- Dart vs Kotlin
- What is Kronos?
- ES6 Interview Questions
- Entity Framework Interview Questions
- COBOL Interview Questions
- Express JS Interview Questions
- OSPF Interview Questions
- LINQ Tutorial
- CSS3 Interview Questions and Answers
- Auth0 Tutorial
- MS Access Interview Questions
- What is SPARQL - A Complete Tutorial Guide
- ExpressJS Tutorial
- UML Tutorial
- HTML vs XML
- Cypress vs Jest
- Impacts of Social Media
- OWASP Interview Questions
- Security Testing Interview Questions
- OpenShift vs Docker
- ES6 Tutorial
- Spark SQL Interview Questions
- Spark SQL Tutorial
- What is OWASP?
- AppDynamics Interview Questions
- Dynatrace Interview Questions
- Rest Assured Tutorial
- New Relic Interview Questions
- REST API Tutorial
- Datadog Interview Questions
- Rest API Interview Questions
- Rest Assured Interview Questions
- PTC Windchill Interview Questions
- Easiest Tech Skills To Learn
- Python SQLite Tutorial - How to Install SQLite
- Datadog Tutorial - Datadog Incident Management
- What is AppDynamics - AppDynamics Architecture
- RabbitMQ Interview Questions And Answers
- What is Dynatrace
- Datadog Vs Splunk
- Web Developer Job Description
- JP Morgan Interview Questions
- Types of Corporate Training
- Benefits of Corporate Training
- What is Corporate Restructuring?
- Blended Learning in Corporate Training
- What is Corporate Level Strategy?
- Flutter Projects and Use Cases
- How to Become a Web Developer
- How To Install Keras?
- How to Install Flutter on Windows?
- How to Install Cypress on Windows?
- How to Become a Computer Scientist?
- How to Install Katalon Studio in Windows
- How to Become a Programmer
- OWASP Projects and Use Cases
- How to Install Sophos?
- Workato Tutorial
- Workato Tutorial - What is Workato?
PingFederate® is the most widely used enterprise federation server for single sign-on (SSO) and user authentication for employees, partners, and customers. Concerns about security and user experience are becoming more prominent as businesses embrace digital business activities. PingFederate enables enterprises to move away from costly, inflexible old identity and access management solutions and instead use a modern identity and access management solution that can handle complex enterprise demands.
This blog outlines some key questions you can expect to be asked during your PingFederate interview.
Top 10 Frequently Asked PingFederate Interview Questions
- What is PingFederate
- What is PingFederate used for?
- What is Adapter in PingFederate?
- What is the difference between PingAccess and PingFederate?
- How does PingFederate SSO work?
- What is Bundled token plug-ins in PingFederate?
- What is transaction logging in PingFederate?
- What is WS- Federation?
- What is metadata in PingFederate?
- How do I enable MFA in PingFederate?
Top PingFederate Interview Questions For Freshers
1. What is PingFederate?
PingFederate is the industry's most widely used business federation server for user authentication and standards-based single sign-on (SSO) for employee, partner, and customer identities. Concerns regarding security and user experience are moving to the forefront as businesses embrace digital business activities.
| If you want to enrich your career and become a professional in PingFederate, then enroll in "PingFederate Training". This course will help you to achieve excellence in this domain. |
2. What is PingFederate SAML?
PingFederate SAML (Security Assertion Markup Language) is an open standard that allows users to log in with just one click (SSO). You can give seamless access to resources and minimize insecure password proliferation by allowing many resources to be accessed with only one set of login credentials.
3. What is PingFederate used for?
PingFederate enables organizations to move away from costly, inflexible legacy identity and access management solutions and instead use a modern identity and access management solution built to satisfy the needs of complex enterprises.
4. Is PingFederate an identity provider?
PingFederate is a federation server that helps businesses manage their identities, single sign-on, and API security. PingFederate enables companies to streamline employee access to all of their company's applications. With a single set of credentials, employees can log into a corporate dock and open all their applications with a single click.
 5. What is Adapter in PingFederate?
5. What is Adapter in PingFederate?
PingFederate can use adapter selectors to choose from a list of configured IdP adapter instances for a single sign-on request. The IP address of the user, the authentication context, and other factors are used to make the decision.
In the "first mile" of application integration, an IDP adapter gathers information about the identity authenticating and sends it to the PingFederate server to continue the federated authentication action.
6. What features are there in PingFederate?
The following are some of the features offered in PingFederate:
- Secure and standards-based
- Support diverse identity types and use cases
- Easily configurable
- Adaptive authentication
- Customizable branding
- Lightweight, scalable architecture
- Pre-built adaptors and integrations
- Multi-protocol support
- Advanced user management
Related Article: What is PingFederate? - A Complete Beginners Tutorial
7. What are the supported Federation Standards?
The following are some of the Federation's supported standards:
- SAML
- WS-Federation
- WS-Trust
- OAuth
- OpenID
- OpenID Connect
- SCIM
8. What is the difference between PingOne and PingFederate?
PingOne is a cloud-based service. Thus you'll have to integrate it as a SaaS application. PingFederate is a piece of software that you can operate on your server or the cloud. You would connect PingFederate to your application and set up a Service Provider IdP connection.
9. What is the difference between PingAccess and PingFederate?
| PingAccess | PingFederate |
| PingAccess is an identity-enabled access management product that applies security controls to client requests to safeguard Web applications and APIs. | PingFederate is a standards-based single sign-on technology that connects Identity Providers and Service Providers via a reliable SAML connection. |
| It integrates identity-based access management rules utilizing a federated corporate identity repository and open standards access protocols with PingFederate. | This connection allows an adequately authenticated user to access the SP's target application to fulfill the IdP's credential criteria without re-entering their password. |
| Access requests are either forwarded to the target Site via a PingAccess Gateway or intercepted by a PingAccess Agent at the target web application server, coordinating access policy choices with a PingAccess Policy Server. | Multi-factor authentication, automated provisioning, user self-service, application integration, and mobile and API access are just a few of the features and benefits that PingFederate has to offer. |
| In either case, policies applied to target Application access requests are reviewed, and PingAccess decides whether to give or restrict access to the requested resource depending on the guidelines. | Here's a handy data sheet that summarizes the many advantages of PingFederate. |
10. How does PingFederate help modernize an enterprise’s application portfolio to include SaaS apps and APIs?
Tokens are supplied to SaaS applications in the form of SAML assertions or standards-based SSO using PingFederate's context-based authentication policies. PingFederate issues all access tokens for API requests made from an OAuth client to a backend API resource that is OAuth-enabled or truly identity-enabled.
PingFederate Interview Questions For Experienced Professionals
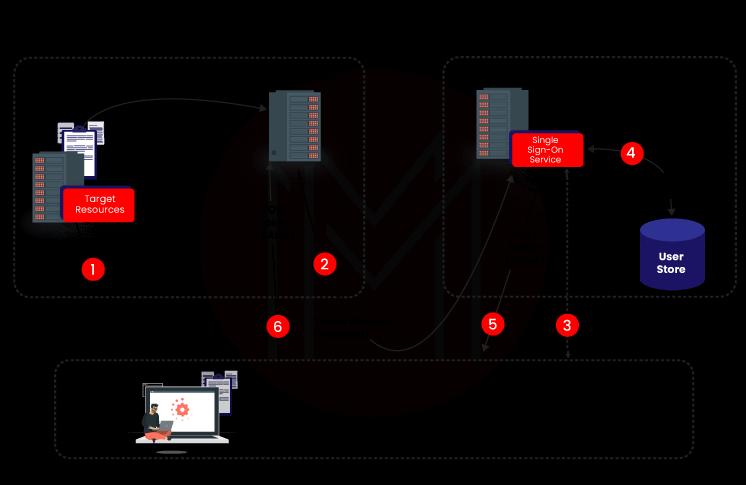
11. How does PingFederate SSO work?
Single sign-on (SSO) allows users to log in with a single set of credentials and access various applications and services. To use SSO, an identity provider (IdP) must set up a centralized authentication server that all apps can use to verify a user's identity. This server can verify user IDs and issue access tokens, encrypted data that prove a user's identity and rights.
The username and password are sent to the identity provider for verification the first time the user signs on. The authentication server compares the credentials to the directory containing the user's data and launches an SSO session in the browser. Instead of requiring a password, the service provider requests that the identity provider validate the user's identity when seeking access to an application within the trusted group.
12. How does PingFederate integrate?
PingFederate offers commercial integration kits that contain adapters that plug into the PingFederate server and agents that interface with local IdM systems or applications to allow both the Identity Provider (IdP) and Service Provider (SP) sides of this integration.
13. What is a PingFederate certificate?
Ping Identity is a Ping Identity Certified Professional. The Ping Identity Certified Professional - PingFederate certification assesses the applicant's ability to illustrate how to do basic setup and configuration tasks.
14. Is it possible to coordinate session timing between PingFederate and PingAccess?
In general, PingFederate and PingAccess are free to use; however, we use OpenID Connect to start the PingAccess meeting. You can put it at that meeting, together with an entry token, so that PingAccess periodically replenishes the meeting token's credits. It can also do renouncement checks and stop sliding.
15. What is Bundled token plug-ins in PingFederate?
PingFederate is an IdP that accepts and authorizes SAML 1.1 and 2.0 tokens and is integrated with token processors. Token generators are supported in an SP configuration, resulting in local SAML 1.1 or SAML 2.0. 2.0 tokens (approaching SAML tokens are approved, by and large, through the use of built-in abilities).
16. What is identity mapping in PingFederate?
The foundation of identity federation is identity mapping. One of the main aims of SAML is to allow an identity provider (IdP) to provide a secure token (the assertion) containing user-identity information that a service provider (SP) may map to local user storage.
- PingFederate supports account linkage and account mapping for browser-based SSO.
- The WS-Trust STS uses account mapping.
17. What is transaction logging in PingFederate?
PingFederate provides basic transaction logging and observation. All federated-identity transactions are logged in a customizable, scalable way using PingFederate (inbound and outbound messages). For debugging or as a one-step method of raising or reducing all connection logging modes to the same level, administrators can adjust transaction logging to any of the four ways on a per-connection basis or override the logging mode for all SP connections, IdP connections, or both. The transaction.log log file can be found in the pingfederate/log directory of the pf install> directory.
18. What do Certificates, SSL, and XML Encryption do in PingFederate?
SSL, certificates, and XML Encryption is the name of the PingFederate security foundation, which supports scrambled data, endorsements, and automated tagging. These features are built into PingFederate's design screens, allowing complete control over endorsement age and confirmation verification.
19. Is there an automated way of migrating a dev environment of PingFederate to production?
PingFederate has a configuration-migration option for automating the transfer of administrative-console configurations and configuration property files from one server to another, such as from a test environment to production. It's also possible to use the program to manage the target server's certificates.
20. What is WS- Federation?
As long as a trust relationship is established, WS-Federation allows users to access resources and services across many security domains or networks. It's only for Microsoft products.
Frequently Asked Questions
21. How does WS- Federation work?
- A user requests access to a resource protected by a service provider (SP). The user isn't logged in. To handle authentication, the request is forwarded to the federation server.
- The SP sends the browser to the identity provider's WS-Federation implementation and generates a security token request.
- If the user has not previously logged on to the identity provider (IdP) site or if re-authentication is required, the IdP will prompt the user for credentials, such as an ID and password, and log on.
- For inclusion in the SAML response, further information about the user can be collected from the user data store. Specific characteristics are predetermined as part of the federation agreement between the IdP and the SP.
- The federation server generates a POST response that includes a signed SAML assertion or a JSON Web Token and sends it to the SP.
- The SP starts a session for the user and redirects the browser to the destination resource if the signature and assertion, or JWT, are valid.
22. How do I deploy PingFederate?
Deploy the Agentless Integration Kit files in your PingFederate directory to get started with the integration.
Steps
- Download the Agentless Integration Kit.zip bundle from the PingFederate downloads page's Add-ons menu.
- PingFederate must be stopped.
- Remove pf-referenceid-adapter-version>.jar from pf install>/pingfederate/server/default/deploy if you're upgrading an existing deployment.
- Copy the contents of the dist directory to your pf install>/pingfederate/server/default directory after extracting the.zip archive.
- If your pf install>/pingfederate/server/default/lib directory has multiple versions of the pf-authn-api-sdk-version>.jar file, delete all but the most recent version.
- Begin using PingFederate.
- Repeat steps 2-6 for each engine node if you're using PingFederate in a cluster.
23. What is the latest version of PingFederate?
PingFederate Version 9.3. 2 is a cumulative maintenance release that includes new authentication APIs, Identifier First Adapter, notification publishers, CIBA compatibility, Amazon CloudHSM support, a faster setup experience for PingID VPN use cases, and more.
24. What is metadata in PingFederate?
The SAML standards define a metadata exchange schema for exchanging XML-formatted data between SAML entities. Endpoint URLs, binding kinds, characteristics, and security-policy information are all examples of metadata that might help federation partners speed up their settings.
You can export metadata to an XML file on the System Metadata Export screen by selecting any SAML Browser SSO connection or manually entering the relevant information. The former is also available on the Connections screen as a per-connection action item. The latter is helpful if you haven't set up a SAML connection yet or wish to generate a single SAML metadata XML file for several partners.
25. How do I export PingFederate metadata?
Export a metadata file that defines the setup of your PingFederate identity provider.
Steps:
- Go to the Metadata Export pane in the PingFederate administration console.
- Go to System Protocol Metadata Metadata Export in PingFederate 10.1 or later.
- Go to System Metadata Export in PingFederate 10.0 or before.
- Select I am the identity provider if the Metadata Role tab appears (IdP). Next should be selected.
- Select information to include in metadata manually on the Metadata Mode tab. Next should be chosen.
- Click Next on the Protocol tab.
- Click Next on the Attribute Contract tab.
- Select a signing certificate from the Signing Key tab. Next should be selected.
- Optional: Select a certificate to sign the metadata XML file on the Metadata Signing tab. Next should be selected.
- Select the certificate you want to encrypt the XML content from the XML Encryption Certificate tab. Continue by pressing the Next button.
- Select Export from the Export & Summary tab.
- Save the metadata.xml file.
- Click the Done button.
26. How do I set up PingFederate?
You can use this procedure to help you set up PingFederate.
- PingFederate should be downloaded.
- Pingfederate should be installed.
- Open the administrator console after starting PingFederate.
- PingFederate walks you through the setup wizard the first time you enter the administration console.
- Learn how to use the PingFederate administration console.
- Menus, windows, and tabs make up the PingFederate user interface.
27. How do I access the PingFederate console?
After the automated deployment is complete, you can log onto the PingFederate administrative console. You can configure clients and do other tasks using the PingFederate administration console.
Access the PingFederate Administration Console to manage your PingFederate account. Use a combination of the PingFederate public hostname, the PingFederate Administration port, and the route to the PingFederate application to open the PingFederate Administration Console in your browser.
28. How do you upgrade PingFederate?
You can upgrade your PingFederate installation using either the PingFederate installer for Windows or the Upgrade Utility, which migrates existing PingFederate installations from version 6.0 and later to the latest version automatically. The Upgrade Utility is no longer a separate download with PingFederate 10.0. It is now included with the software installation.
29. How do I enable MFA in PingFederate?
In PingOne, enable multi-factor authentication (MFA) policy for your applications.
- Click Settings in the PingOne dashboard.
- Click +Add Policy under Authentication Policies.
- For the initial Step Type, choose one of the options.
- Several options are available, depending on how you want your user experience to be. Login was chosen as an example.
- Select Multi-factor Authentication after clicking +Add Step.
- Choose which methods you'd like your users to have access to.
- If you've built a mobile app for MFA, you'll be able to correlate this login logic with it.
- When a user is processed through this policy, choose relevant rules to be assessed.
- See Add a multi-factor authentication step for additional information on these choices.
- After you've double-checked your choices, hit Save.
- Connections should be selected.
- Click the Pencil symbol next to the chosen connection to apply your new policy.
- The Policies tab will appear. Click.
- Drag and drop your policy to the Applied Policies list from the All Policies list.
- Save your work.
30. How does PingFederate allow SiteMinder for the organization?
If you only require Federation support, such as SAML or WS-Federation, you can use either PingFederate or CA Siteminder as an alternative. However, if you want to use PingAccess for access control and PingFederate for authentication, you'll need both PingAccess and PingFederate.
So, if you're simply utilizing CA Federation, PingFederate is the product you're probably using, and the flow is virtually the same as CA's because they're both supporting standards. An excellent place to start would be the PingFederate manual.
Conclusion
This blog has now come to an end. These PingFederate Interview questions will give you an idea of the types of questions that might be asked during your job interview.
 On-Job Support Service
On-Job Support Service
Online Work Support for your on-job roles.

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs:
- Pay Per Hour
- Pay Per Week
- Monthly
| Name | Dates | |
|---|---|---|
| PingFederate Training | May 26 to Jun 10 | View Details |
| PingFederate Training | May 30 to Jun 14 | View Details |
| PingFederate Training | Jun 02 to Jun 17 | View Details |
| PingFederate Training | Jun 06 to Jun 21 | View Details |

Viswanath is a passionate content writer of Mindmajix. He has expertise in Trending Domains like Data Science, Artificial Intelligence, Machine Learning, Blockchain, etc. His articles help the learners to get insights about the Domain. You can reach him on Linkedin




