- 6 Hot And In-Demand Tech Areas In 2024
- How To Forward Your Career With Cloud Skills?
- Top 7 On-Demand IT Certifications
- Most In-demand Technologies To Upskill Your Career
- Top 10 Hottest Tech Skills to Master in 2024
- Top Skills You Need to Become a Data Scientist
- Groovy Interview Questions
- Facets Interview Questions
- Crystal Reports Tutorial
- VAPT Interview Questions
- Flutter Tutorial
- Saviynt VS Sailpoint
- Flutter vs Xamarin
- PingFederate Interview Questions and Answers
- Dart vs Javascript : What's the Difference?
- Terraform Private Registry
- Cylance Interview Questions and Answers
- Sophos Interview Questions and Answers
- Top Camunda Interview Questions
- NUnit Interview Questions and Answers
- Impala Interview Questions and Answers
- ETL Tutorial
- Ionic Interview Questions
- Grafana Tutorial
- What is VAPT? - A Complete Beginners Tutorial
- SnapLogic Interview Questions
- Saviynt Interview Questions
- What is PingFederate? - A Complete Beginners Tutorial
- SnapLogic Tutorial
- Grafana Interview Questions
- RHCE Interview Questions and Answers
- Web Services Interview Questions
- Domo Interview Questions and Answers
- Terraform Interview Questions
- What is Sophos? | Sophos Turorial for Beginners
- Top Servlet Interview Question And Answers
- NLP Interview Questions and Answers
- Microsoft Intune Interview Questions
- Top XML Interview Questions And Answers
- Tosca Commander
- Katalon vs Cypress
- SQLite Tutorial
- Tosca Tutorial - A Complete Guide for Beginners
- Xamarin Interview Questions and Answers
- UiPath vs Automation Anywhere - The Key Differences
- OpenShift Interview Questions
- What is Katalon Studio - Complete Tutorial Guide
- Kronos Interview Questions
- Tosca Framework
- Burp Suite Tutorial
- Mendix Interview Questions
- Power Platform Interview Questions
- Burp Suite Interview Questions
- What is Mendix
- What is Terraform ?
- Burp Suite Alternatives
- Dart vs Kotlin
- What is Kronos?
- ES6 Interview Questions
- Entity Framework Interview Questions
- COBOL Interview Questions
- Express JS Interview Questions
- OSPF Interview Questions
- LINQ Tutorial
- CSS3 Interview Questions and Answers
- Auth0 Tutorial
- MS Access Interview Questions
- What is SPARQL - A Complete Tutorial Guide
- ExpressJS Tutorial
- UML Tutorial
- HTML vs XML
- Cypress vs Jest
- Impacts of Social Media
- Security Testing Interview Questions
- OpenShift vs Docker
- ES6 Tutorial
- Spark SQL Interview Questions
- Spark SQL Tutorial
- What is OWASP?
- AppDynamics Interview Questions
- Dynatrace Interview Questions
- Rest Assured Tutorial
- New Relic Interview Questions
- REST API Tutorial
- Datadog Interview Questions
- Rest API Interview Questions
- Rest Assured Interview Questions
- PTC Windchill Interview Questions
- Easiest Tech Skills To Learn
- Python SQLite Tutorial - How to Install SQLite
- Datadog Tutorial - Datadog Incident Management
- What is AppDynamics - AppDynamics Architecture
- RabbitMQ Interview Questions And Answers
- What is Dynatrace
- Datadog Vs Splunk
- Web Developer Job Description
- JP Morgan Interview Questions
- Types of Corporate Training
- Benefits of Corporate Training
- What is Corporate Restructuring?
- Blended Learning in Corporate Training
- What is Corporate Level Strategy?
- Flutter Projects and Use Cases
- How to Become a Web Developer
- How To Install Keras?
- How to Install Flutter on Windows?
- How to Install Cypress on Windows?
- How to Become a Computer Scientist?
- How to Install Katalon Studio in Windows
- How to Become a Programmer
- OWASP Projects and Use Cases
- How to Install Sophos?
- Workato Tutorial
- Workato Tutorial - What is Workato?
OWASP, or Open Web Application Security Project, is a non-profit organization that aims to improve and educate online users about web security. It has several tools, applications, and guides that contribute to improving the overall health of the internet. It is very important for educators, developers, managers, and architects to know about the importance of web security and also the consequences of not adhering to security measures. With the help of OWASP, you also get to identify which security areas need more attention and what methodologies to follow.
Importance of OWASP:
- OWASP provides a free and open-source tool for automated scanning for vulnerabilities. These tools are completely free to use.
- It opens up doors for everyone who wants to contribute related to projects based on web security. Users can participate in online forums and resolve queries related to security-based issues.
- Since 2003, OWASP has maintained its position in the top 10 advancement security list.
- OWASP provides cheatsheet, MSTG and WSTG-like operations from an open platform.

It is a web application security-related online community that produces several tools, techniques, articles, technologies, and other publications. We have brought you an amazing series of FAQs and interview questions for both freshers and experienced in order to assist you in landing your dream job. The following are some of the questions you might anticipate being asked at an OWASP interview. So let's start preparing!
Top 10 OWASP Interview Questions
- Describe IPSEC.
- What are OWASP WebGoat and WebScarab?
- Describe the Owasp risk rating system.
- What is OWASP ESAPI?
- Describe bug bounty.
- Describe the various security testing methodologies.
- What Exactly Do You Mean by Security Testing?
- How to diminish SQL Injection risks?
- Are Authentication and Authorization Different?
- What Could You Tell Us About XXS?
OWASP Interview Questions For Freshers
1. Describe OWASP.
A group or online community called OWASP (Open Web Application Security Project) has made a considerable investment in safe software development. In order to help with online application security, it, therefore, makes available free papers, tools, software, techniques, and technologies. Dennis Groves and Mark Curphey created it in 2001.
2. Give a valid explanation of the risk involved in not designating HTTP cookies with the security tokens as secure.
The risk of an Access Control Violation occurs when HTTP cookies containing tokens are not marked as secure.

3. Have You Ever faced Sensitive Data Exposure? How Might It Be Reduced?
The threat of sensitive data disclosure, which is a major problem in web security, can be mitigated in a number of ways. Encrypting data is the easiest and most obvious way to safeguard it against cyberattacks. Sensitive information ought to be deleted as soon as feasible rather than being stored incorrectly or pointlessly. Creating a threat model for the purpose of data security in transit and during testing, storing passwords with a password protection scheme, and blocking auto-completion of forms that gather sensitive data are further methods.

4. Describe IPSEC.
The IETF (Internet Engineering Task Force) standardized protocol suite for the two different communication levels of an IP network includes IPSEC, commonly known as IP security. It guarantees the confidentiality, authenticity, and integrity of the dataset. It produces encrypted and decrypted data packets with authentication.
| If you want to enrich your career and become a professional in Cyber Security and SIEM, then enroll in "OWASP Training". This course will help you to achieve excellence in this domain. |
5. What are OWASP WebGoat and WebScarab?
WebGoat: It serves as a benchmark for testing security technologies against known problems and is a learning tool for application security. It is a J2EE web-based application built on the basis of tomcat and JDK 1.5 that is divided into "Security Lessons"
WebScarab: A framework for evaluating HTTP/HTTPS traffic is called WebScarab. It performs a number of tasks, including fragment analysis, observing browser and server traffic, session ID analysis, manual intercept, and locating new URLs on each page browsed.
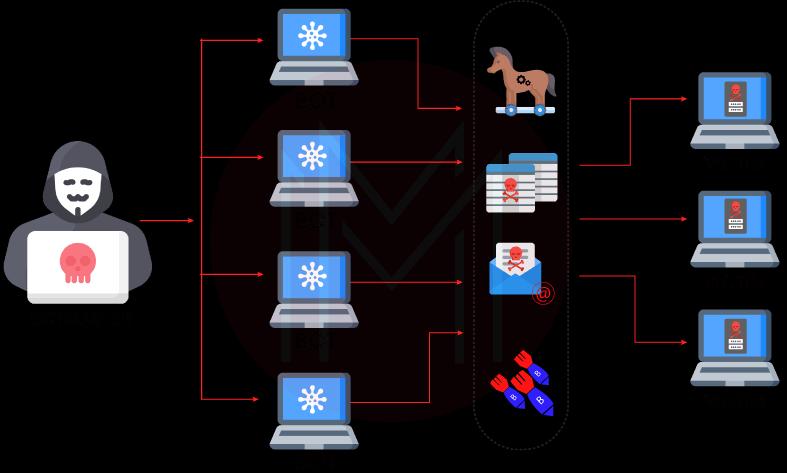
6. What is a botnet?
A group of internet-connected gadgets that are home to one or more bots is known as a botnet. These could be a number of privately owned computers that are being remotely managed without the owner's knowledge and that include harmful or hacked software. Consequently, in the botnet attack, a computer is compromised and then infected with malware. The malware then establishes a connection between the system and the main botnet server. Data theft, spam distribution, hacker access to a smartphone and its connections, and different heterogeneous denial of service attacks that block authorized users from various services are the main uses of botnets.
7. Give an example of a threat that can be averted by generating unique usernames with a high level of entropy.
By using a high level of entropy to create distinct usernames, authorization bypass could be avoided.
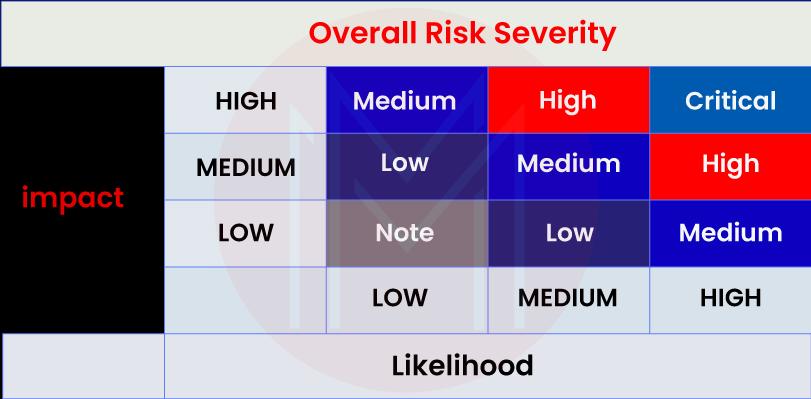
8. Describe the Owasp risk rating system.
Owasp's risk rating algorithms are divided into various tiers, including Layer for System Risk Identifications Estimating the Risk mechanism's source Impact analysis, and estimation assessing the risk's seriousness. Risk-reduction strategies.
9. What does OSI stand for?
The Open Systems Interconnection (OSI) paradigm, often known as a communication model, enables the usage of common protocols with various communication systems. The International Organization for Standardization is creating it.
10. What is OWASP ESAPI?
Developers can create or construct lower-risk apps using the Open-Source Web Application Security Control framework known as OWASP ESAPI (Enterprise Security API).
11. Describe bug bounty.
Many large corporations have programs called "bug bounties" that offer payments to people who notify them of security flaws. After resolving the problems, these firms typically post those vulnerabilities on their websites.

12. Describe the OWASP ESAPI's core design.
The OWASP ESAPI's fundamental layout consists of
- Interfaces for security controls
- There's a reference implementation for each type of security control.
- Each security measure has options for deployment within your own company.

13. Mention what occurs when a user's data is loaded into an application and sent to a web browser rather than being properly validated and escaped.
When an application delivers user-inputted data to a web browser without performing adequate validation and escaping, cross-site scripting occurs.
14. How can we prevent forced browsing from affecting web applications?
Carefully verify access-control settings are correct and complete on all website pages and applications to prevent forced browsing of web applications.
15. Tell us about the problem that results from the session tokens' insufficient randomization across a range of values.
Session tokens' low randomization across a range of values leads to session hijacking.
OWASP Interview Questions For Experienced
1. List out the controls to test during the assessment.
- Authenticate Testing
- Authorization Testing
- Business logic testing
- Client-side testing
- Configuration and Deploy management testing
- Cryptography
- Data Validation Testing
- Error Handling
- Identify Management testing
- Information gathering
- Session Management Testing
2. Give OWASP definitions for WebGoat and WebScarab
The goal of OWASP is to strengthen web security. Thus, WebGoat is a purposefully unsafe web application created to impart security practices and lessons to users. It features activities to teach individuals about security controls and penetration methodologies as well as examples of various server-side application problems.
WebScarab, on the other hand, is a toolkit that intercepts requests and server responses and provides users the freedom to change them. Additionally, it might keep track of traffic for later analysis. All of these resources belong to the Open Web Security Project.
3. Are You Aware of the OWASP Project's Application Security Verification Standard?
This project enables web application developers to test technological security mechanisms. It also includes a set of specifications that improve secure development. It is typically employed to reliably create secure online apps. A basis for specifying application security verification criteria in many contracts is another provision, as is guidance for security developers on what to include in security controls to meet application security needs.Overall, this project is mostly used as a statistic to assess the level of confidence that web application developers should have.
4. Describe the various security testing methodologies.
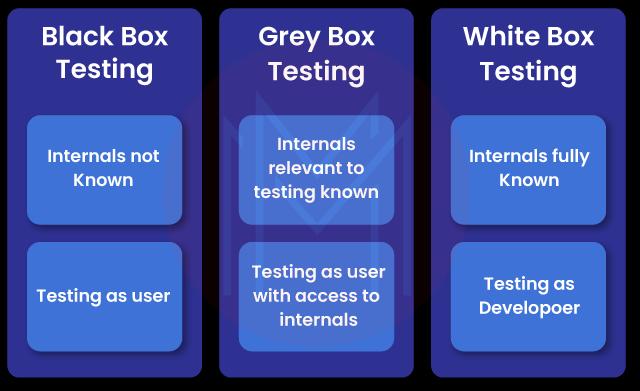
Grey box, white box, and black box are the three main security testing approaches.
- Grey Box Testing: In grey box testing, testers are only given incomplete knowledge. The remainder must be worked out on their own.
- White Box Testing: In this testing is typically employed to check whether the code implementation adhered to the intended design. Additionally, it displays some of the current vulnerabilities and evaluates security functionalities. The testers in this form of testing are given a wide variety of information.
- Black-Box Testing: It involves testing the defenses, security measures, and application designs with little to no prior information about the operation of the program.
5. How to effectively reduce the great risk of Sensitive Data Exposure?
The reduction methods that are adopted for secure applications from Sensitive data exposure are as follows:
- Create a threat model to protect data from both sorts of attackers when it is in transit and at rest ( e.g., external user type or inside attack type).
- Strong standardized algorithms and robust keys should always be utilized, and appropriate key management should be in place. FIPS 140 certified cryptographic modules should be used.
- To safeguard data from online attacks, encrypt it.
- Never voluntarily store critical information. As quickly as you can, throw it away. You can't steal data that you don't possess.
- Make that passwords are stored using a password-protection-specific algorithm, such as scrypt, bcrypt, or PBKDF2.
- Disabling autocomplete on such forms that request sensitive information and disabling caching on pages that do so.
6. What Exactly Do You Mean by Security Testing?
One of the most important kinds of software testing is security testing. Before an app is made available to the public, it must be completed. This kind of testing finds weaknesses in software, including network- or web-based applications. As a result, it defends against assaults and intrusions. Any sensitive data in an app is secured from leaking thanks to security testing. It is also important to note that an organization or developer must perform it frequently to find and address various vulnerabilities, similar to any other form of software testing.
7. Can you List the Top 10 OWASP Vulnerabilities?
The top 10 OWASP security flaws are:
- Broken Authentication and Session Management
- Cross-site scripting
- Failure to restrict
- Failure to restrict URL access
- Information leakage and improper error handling
- Injection
- Insecure communications
- Insecure cryptographic storage
- Insecure direct object reference
- Malicious file execution
8. How to diminish SQL Injection risks?
SQL injection mitigation:
Whenever using ready statements with parameterized queries, be sure your SQL interpreter can tell the difference between code and data. Never employ dynamic searches that are unable to distinguish between them. Use a static SQL query instead, and then give the external input as a query parameter. When using prepared statements (with parameterized queries), the developer is compelled to first define all the SQL code before passing each query parameter.
Implementing stored procedures:
A stored procedure is similar to a C function that a database administrator can call whenever necessary. Although SQL injection threats are not entirely eliminated, they are significantly decreased by preventing dynamic SQL generation inside.
White List Input Validation:
Only allow input that has been pre-approved by the developer and always utilize white list input validation. Never employ a blacklist strategy since it offers less security than a whitelist strategy.
Using the least privilege and removing all user input

9. How can the danger of weak session management and authentication be reduced?
Controls of session management and strong authentication can reduce the impact of weak authentication and session management. These are some examples of controls:
- Complies with all authentication and session management specifications outlined in OWASP's ASVS (Application Security Verification Standard) sections V2 (Authentication) and V3 (Session Management).
- For developers, always utilize a straightforward interface. Consider using, emulating, or building upon the User APIs and ESAPI Authenticator as models.
- Use best practices to prevent cross-site scripting attacks on session id.

10. What does OWASP's passive mode or phase I of security testing entail?
The comprehension of the application's logic and information gathering using the proper tools are part of the passive mode, or phase I, of security testing. The tester should be able to identify all of the application's gates and access points at the conclusion of this phase.
11. How Can the Risks of SQL Injection Be Reduced?
SQL mitigation risks could be reduced by a bunch of approaches. First, developers or online security professionals should avoid utilizing dynamic queries to guarantee that the SQL translator is better able to recognize a code and data collection. When using prepared statements, programmers must define the SQL code before giving the query's input arguments.
Using stored procedures, which are C programs that a database administrator can use at any time, is another way to lessen it. It aids in stopping the creation of dynamic SQL. White list input validation, applying the principle of least privilege, and escaping user inputs are other mitigation techniques.
12. Describe OWASP. Also, tell us about the OWASP TOP 10 2021.
The nonprofit group OWASP publishes a list of the most prevalent web vulnerabilities. It functions as a network of cybersecurity experts who are continually working to create an ecosystem for spreading knowledge about secure online apps. Recent updates to OWASP's top 10 vulnerabilities for 2021 include:
- A01:2021-Broken Access Control
- A02:2021-Cryptographic Failures
- A03:2021-Injection
- A04:2021-Insecure Design
- A05:2021-Security Misconfiguration
- A06:2021-Vulnerable and Outdated Components
- A07:2021-Identification and Authentication Failures
- A08:2021-Software and Data Integrity Failures
- A09:2021-Security Logging and Monitoring Failures
- A10:2021-Server-Side Request Forgery

13. Are Authentication and Authorization Different?
An entity, user, or website's identity is confirmed by authentication. It 100% confirms that a person is who they claim to be. The regulations governing the authority provided to certain parties, in contrast, are referred to as authorization. It can also be referred to as the method of figuring out whether a client is allowed to utilize a particular resource or access a specific file. Therefore, verification is the main focus of authentication, whereas permissions are the main focus of authorization. For authentication, you must log in and input your password, whereas, for authorization, you need to have the necessary clearance.
14. Describe the components of the (ASVS)OWASP Application Security Verification Standard initiative.
The standard project for OWASP application security comprises:
- As a metric, use: It offers a benchmark for app owners and app developers to assess the level of trust that may be given in their online apps.
- Use this as a guide: It gives authors of security controls guidance on what to include in security protocols in order to satisfy the requirements for application security.
- Use while making a purchase: It offers a foundation for defining contract requirements for application security verification.
15. What Could You Tell Us About XXS?
Cross-Site Scripting, or XXS, is a sort of client-side code injection that enables an attacker to insert malicious scripts into a web browser. Session tokens, cookies, and a lot of sensitive data can all be readily compromised. XXS comes in three basic varieties: reflected, saved, and DOM.
The dangerous script in the reflected XXS, in contrast to the stored XXS, originates from the existing HTTPS request rather than being stored in the database. The dangers in the Document Object Model XXS, often known as DOM XXS, are discovered in the client-side code rather than the server code.
We may emphasize the following as some of the primary advantages that OWASP offers to businesses and IT professionals:
- Aids in strengthening applications' defenses against online threats.
- Decreases the frequency of mistakes and system failures.
- Makes greater encryption possible.
- Ups the likelihood that an application will be successful.
- Enhances the company's reputation as a software provider.
Frequently Asked OWASP Questions
1. What is OWASP?
A nonprofit organization dedicated to providing improved and optimized software security is the Open Web Application Security Project (OWASP).
| Related Article: What is OWASP? |
2. What are OWASP security principles?
The principles as stated in the OWASP development guide include
- Minimize attack surface area
- Fail securely
- Don't trust services
- Separation of duties
- Avoid security by obscurity
- Keep security simple
- Fix issues correctly
- Establishing secure defaults
3. How is OWASP executed?
- Define the security demands.
- Apply libraries and frameworks for security.
- Access to a secure database.
- Data encryption and escape
- Verify Every Input
- Digital identity implementation.
- Implement access controls.
- Data protection at all times.
4. Is OWASP a framework?
OWASP Security Knowledge Framework, an open-source web application, discusses secure coding principles in a variety of programming languages. The OWASP SKF's Objective is to assist you in learning security by design, incorporating it into your software development, and creating secure-by-design applications.

5. What is OWASP XSS?
Malicious scripts are introduced into otherwise trustworthy and innocent websites in Cross-Site Scripting (XSS) attacks. XSS attacks take place when an attacker sends malicious code, most often in the form of a browsing side script, to a separate end user using an online application.
6. Is OWASP still relevant?
The OWASP Top Ten Project's success can be attributed to its simplicity, ability to assist users in prioritizing risk, and actionability. There are several positive aspects, including the emphasis on the most serious threats rather than particular vulnerabilities.
7. Do mobile apps come under Owasp?
Mobile Application Security Verification Standard is offered by OWASP (MASVS). A standard for phone app security is the OWASP MASVS. It can be used by smartphone architects, developers, and testers to create safe mobile applications and to guarantee the consistency and thoroughness of test results.

8. Why is OWASP so crucial?
In order to make certain that security is built from the ground up and that the final product is as secure as possible, OWASP is a free and open-source security community project that offers a vast amount of information and tools to assist someone involved in the production, development, testing, implementation, and support of a web application.
9. OWASP ZAP: Is it secure?
ZAP is entirely safe and within legal rights for proxying requests; it merely lets you observe what is happening. Spidering is a little riskier. Depending on the operation of your application, it can result in issues.

10. How do Owasp and Azure DevOps integrate?
- Add a Bash Script Task
- Add the artifact to the release pipeline
- Add the Docker Installer Task
- Add tasks to the pipeline.
- Configure Agent Job Details
- Configure the Bash Script Task
- Create a new release pipeline
Conclusion:
Looking at these perks, it is yet an easy task to say that web application security is a crucial aspect of all human activities in the Internet World. We wish you the best of luck with your upcoming interview, and we hope this article will help you understand the types of questions that you may encounter.
 On-Job Support Service
On-Job Support Service
Online Work Support for your on-job roles.

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs:
- Pay Per Hour
- Pay Per Week
- Monthly
| Name | Dates | |
|---|---|---|
| OWASP Training | Jun 09 to Jun 24 | View Details |
| OWASP Training | Jun 13 to Jun 28 | View Details |
| OWASP Training | Jun 16 to Jul 01 | View Details |
| OWASP Training | Jun 20 to Jul 05 | View Details |

















