- 6 Hot And In-Demand Tech Areas In 2024
- How To Forward Your Career With Cloud Skills?
- Top 7 On-Demand IT Certifications
- Most In-demand Technologies To Upskill Your Career
- Top 10 Hottest Tech Skills to Master in 2024
- Top Skills You Need to Become a Data Scientist
- Groovy Interview Questions
- Facets Interview Questions
- Crystal Reports Tutorial
- VAPT Interview Questions
- Flutter Tutorial
- Saviynt VS Sailpoint
- Flutter vs Xamarin
- PingFederate Interview Questions and Answers
- Dart vs Javascript : What's the Difference?
- Terraform Private Registry
- Cylance Interview Questions and Answers
- Sophos Interview Questions and Answers
- Top Camunda Interview Questions
- NUnit Interview Questions and Answers
- Impala Interview Questions and Answers
- ETL Tutorial
- Ionic Interview Questions
- Grafana Tutorial
- What is VAPT? - A Complete Beginners Tutorial
- SnapLogic Interview Questions
- What is PingFederate? - A Complete Beginners Tutorial
- SnapLogic Tutorial
- Grafana Interview Questions
- RHCE Interview Questions and Answers
- Web Services Interview Questions
- Domo Interview Questions and Answers
- Terraform Interview Questions
- What is Sophos? | Sophos Turorial for Beginners
- Top Servlet Interview Question And Answers
- NLP Interview Questions and Answers
- Microsoft Intune Interview Questions
- Top XML Interview Questions And Answers
- Tosca Commander
- Katalon vs Cypress
- SQLite Tutorial
- Tosca Tutorial - A Complete Guide for Beginners
- Xamarin Interview Questions and Answers
- UiPath vs Automation Anywhere - The Key Differences
- OpenShift Interview Questions
- What is Katalon Studio - Complete Tutorial Guide
- Kronos Interview Questions
- Tosca Framework
- Burp Suite Tutorial
- Mendix Interview Questions
- Power Platform Interview Questions
- Burp Suite Interview Questions
- What is Mendix
- What is Terraform ?
- Burp Suite Alternatives
- Dart vs Kotlin
- What is Kronos?
- ES6 Interview Questions
- Entity Framework Interview Questions
- COBOL Interview Questions
- Express JS Interview Questions
- OSPF Interview Questions
- LINQ Tutorial
- CSS3 Interview Questions and Answers
- Auth0 Tutorial
- MS Access Interview Questions
- What is SPARQL - A Complete Tutorial Guide
- ExpressJS Tutorial
- UML Tutorial
- HTML vs XML
- Cypress vs Jest
- Impacts of Social Media
- OWASP Interview Questions
- Security Testing Interview Questions
- OpenShift vs Docker
- ES6 Tutorial
- Spark SQL Interview Questions
- Spark SQL Tutorial
- What is OWASP?
- AppDynamics Interview Questions
- Dynatrace Interview Questions
- Rest Assured Tutorial
- New Relic Interview Questions
- REST API Tutorial
- Datadog Interview Questions
- Rest API Interview Questions
- Rest Assured Interview Questions
- PTC Windchill Interview Questions
- Easiest Tech Skills To Learn
- Python SQLite Tutorial - How to Install SQLite
- Datadog Tutorial - Datadog Incident Management
- What is AppDynamics - AppDynamics Architecture
- RabbitMQ Interview Questions And Answers
- What is Dynatrace
- Datadog Vs Splunk
- Web Developer Job Description
- JP Morgan Interview Questions
- Types of Corporate Training
- Benefits of Corporate Training
- What is Corporate Restructuring?
- Blended Learning in Corporate Training
- What is Corporate Level Strategy?
- Flutter Projects and Use Cases
- How to Become a Web Developer
- How To Install Keras?
- How to Install Flutter on Windows?
- How to Install Cypress on Windows?
- How to Become a Computer Scientist?
- How to Install Katalon Studio in Windows
- How to Become a Programmer
- OWASP Projects and Use Cases
- How to Install Sophos?
- Workato Tutorial
- Workato Tutorial - What is Workato?
The utmost concern of most organizations, irrespective of their size, is "security" and the area of their operations. Saving the data from the unfolding security risks has been the priority of organizations.
Hence professionals who are well trained and skilled on the IAM tools like Saviynt have a massive demand in the market.
Mindmajix offers an advanced Saviynt Course with Certification and Interview Questions for Experienced and Freshers to help you crack your interview & achieve a dream career as Saviynt Developer.
According to research, Saviynt has occupied a market share of 2.74% in the cloud-access-security-broker market and has given innumerable opportunities for many reputed companies and professionals skilled in this area.
We have categorized Saviynt Interview Questions - 2024 (Updated) into 2 levels they are:
Top 10 Frequently Asked Saviynt Interview Questions
- What is Saviynt?
- In which areas is Saviynt used?
- What are the basic primary operations of Saviynt?
- What are the products and platforms that Saviynt supports?
- Mention some benefits of Saviynt’s IAR?
- What are the different API calls available in Saviynt?
- What are the modules present in Saviynt?
- Mention the multi-dimensional RISK model of Saviynt?
- Name a few features of Saviynt?
- Describe some of the primary duties of Saviynt?
Saviynt Questions for Beginners
If you are new to this field, these are the basic questions mostly posed to freshers. Preparing these questions first will boost your confidence enough to face the interview.
1. What is Saviynt?
Ans: Saviynt is a cloud-built identity and access governance platform that can help modern enterprises to level up their cloud initiatives. It offers the latest solution to overcome the challenges of compliance and security. Saviynt offers granular application access, frictionless user experience, Secure the whole business ecosystem, identity governance(IGA), and cloud security.
The world’s largest brands trust Saviynt to accelerate digital transformation, empower distributed workforces, and meet continuous compliance. Most organizations rely on Saviynt to fulfill the adherence terms, speed up the digital transformation process, and authorize the workforces.
Data protection, enterprise, and cloud applications are all offered on a single platform by Saviynt. Minimizing security threats, intelligence management, and risk analytics differentiates Saviynt from its peers.
| If you want to enrich your career and become a professional in Saviynt, then enroll in "Saviynt Online Training" - This course will help you to achieve excellence in this domain. |
2. What is IAM?
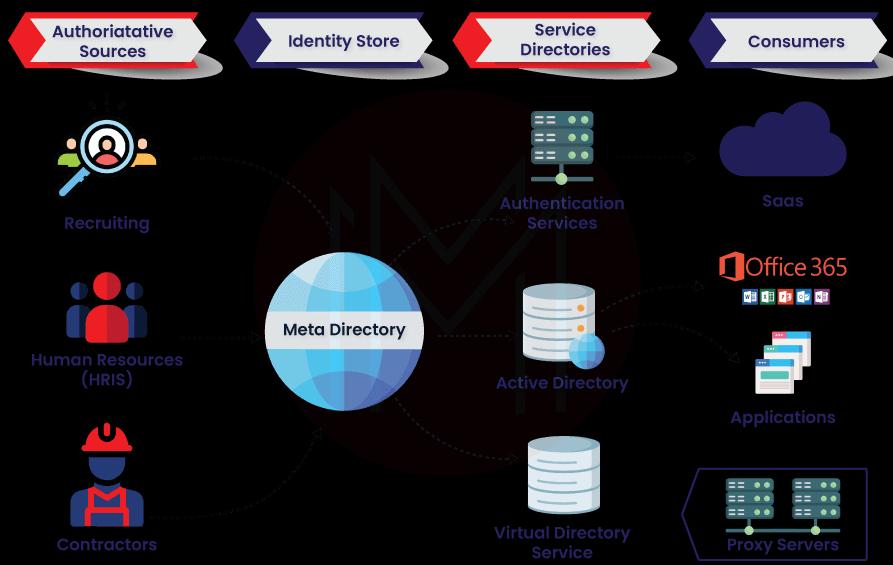
Ans: IAM (Identity and Access Management) manages the user and device access to cloud and platform applications. Employees, stakeholders, customers, etc., are referred to as users, and the devices that support IAM include computers, tablets, smartphones, routers, sensors, etc.
The IAM tool issues a single digital identity and password to the users. Hence, their identities should be managed to protect the organizational information from falling into the wrong hands.
3. What are the risks involved in IAM?
Ans: Organizations with the updated architecture face the following IAM risks:
- Operational Risk
- Information Security Risk
- Compliance Risk
- Privacy Risk
4. In which areas is Saviynt used?
Ans: Saviynt is used in the following departments:
- Healthcare
- Financial Services
- Energy
- Higher Education
- Federal Government
5. What are the applications that support integration with Saviynt?
Ans:
- Azure AD and Okta
- AWS, Azure, and GCP
- Workday and Salesforce
- Epic and Cerner
- ServiceNow
- SAP and Oracle
- Box and O365
6. What are the basic primary operations of Saviynt?
Ans: The core operations of Saviynt are:
- Multi-cloud Governance
- Modernizing Legacy IGA
- Machine Identities
- Third-Party/Vendor Access
- Non-stop Compliance
- Control Internal Identities
7. What are the products and platforms that Saviynt supports?
Ans:
- Identity Governance and Intelligence
- Infrastructure Access Management
- Application Access Governance
- Data Access Governance
- External Access Governance
8. What is Segregation of Duties in Saviynt, and what is its need?
Ans: Segregation of duties is the core foundation of Saviynt as it eases the tasks of many users by executing a service method to keep a check on the threat of internal scams.
| Related Article: Saviynt vs Sailpoint Which One is Better? |
9. What are Entitlements and their usage?
Ans: Entitlements portray the benefits of a device or an application on any platform. Entitlements are allied to the profiles in the database.
10. What is Authoritative Source in Saviynt?
Ans: Authoritative Source is a secure application that is the sole resource for data correctness. This document stores and saves the customer's data and acts as a primary source for data verification.
11. What are Connected Applications?
Ans: Applications linked to Saviynt through OOTB adapters following all the connection guidelines are connected applications or linked apps. These apps also automatically provide banners that are allowed in the Security System.
Saviynt Interview Questions for Experienced
If you are an experienced candidate in this domain with 2+ years, these are some of the questions most likely asked by an interviewer. Preparing yourself with these questions will enhance your knowledge and confidence.
12. What is the use of IAR in Saviynt?
Ans: To overcome this problem, Saviynt's Intelligent Access Request provides advanced capabilities to find secured and convenient access. This helps the users to understand anomalous or high-risk access requests. Thus this advanced feature of Saviynt helps the employee improve productivity by eliminating the waiting time to access approvals.
13. Mention some benefits of Saviynt’s IAR?
Ans: Benefits
- Request access without friction
- Fast Access
- Simplified approval process design
- Easy detection of risk
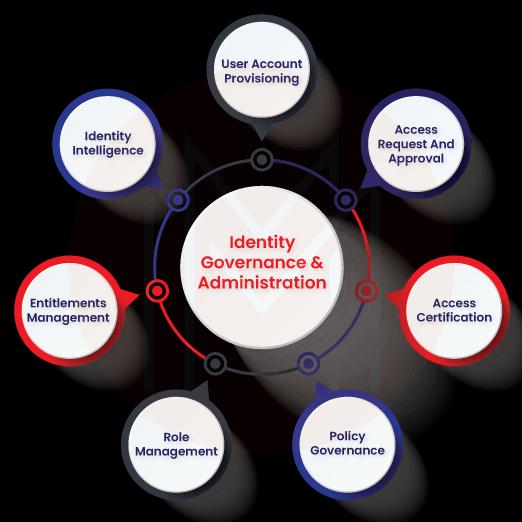
14. What is IGA in Saviynt?
Ans: The Identity Governance Application in Saviynt simplifies access request workflows for administrators and end-users. It provisions applications and segregation of duty (SOD), and another violation of risks is prevented automatically by IGA. Organizations use Saviynt applications to provide their partners, customers, and employees with flexible workflows when requesting, granting, and monitoring application access.
15. Where is Saviynt IGA used?
Ans: Saviynt Identity Governance and Administration (IGA) is used when there is a need to deliver safety and security for a company’s crucial data. This increases the company's productivity by giving correct accessibility for the best consumers, which is time-saving.
16. What are the different API calls available in Saviynt?
Ans: Some of the API calls that are included in Saviynt are
- APIs for rule engineering
- APIs for Create-Read-Update-Delete (CRUD)
- APIs for managing rules
- APIs for managing access requests and approval workflow
- APIs for management analytics and dashboards
- APIs for Segregation of Duties (SoD)
- APIs for delegation administration
17. What are the modules present in Saviynt?
Ans: Various modules present in Saviynt are:
- SOD Management Continuous Controls
- Request Certification
- Roles / Rule / Policy Management
- Reports of Identity Analytics
- Password Management
- User Administration
18. Mention the multi-dimensional RISK model of Saviynt?
Ans:
Static:
- Context-based access policies
- Segregation of duty policies
- Security & Compliance controls
- Classification / Glossary
Dynamic:
- Usage analysis
- Outlier / Peer analysis
- Behavior analysis
- Access outside role
Inherent:
- Geolocation
- Threat intelligence/vulnerability
- User type
19. What is the security manager in Saviynt?
Ans: The security manager in Saviynt is responsible for guarding the data, functions, and facilities on Cloud (Office 365, Workday, AWS, Azure, Salesforce) and Enterprise (SAP, Oracle EBS). IGA 2.0 is led by Saviynt by automating risk analytics, knowledge, and power advantage monitoring.
20. Name a few features of Saviynt?
Ans:
ATTESTATION Tab: This tab is used to initiate the authentication for the certification of accessibility concerning many services.
ADMIN Tab: This tab is used to deal with Funds, Protection bodies, individuals, Titles, Password Plans, Functions, Individual Teams, Endpoints, and Interaction with Organizations.
ARS Tab: This tab is used when there is a demand for accessibility for personal data link handing over the consumer recommended tasks. It can be used for upgrading individual particulars, code reset and producing other functions.
ROLE Tab: It is used in producing Role, Entitlement Discovery, and Role Mining.
SOD Tab: It is used to generate, publish, and handle SOD. Handling SOD includes SOD Reports, SOD Violations, Ruleset Requests, Mitigating Controls, Ruleset, Risk, and Functions.
21. What is the Identity Access Rule in Saviynt?
Ans: The Identity Access Rules are a collection of guidelines that describe particular circumstances and trigger the activities. Identity Access rules can be enhanced, or the operations can be adjusted using the Global Configuration setups.
22. What are the actors involved in a Campaign in Saviynt?
Ans:
Certifier: User Managers/ Role Owners/ Entitlement Owner/ Service Account Owner.
End-User: Consumers who gain access and are being evaluated by a certifier.
Delegate: An individual whom the Certifier has handed over their duties.
Campaign Owner: Person that possesses the Campaign coming from SAM Support group.
Access Provisioning Team: In the scenario of hand-operated provisioning SAM Role Admin/ L3 Support Role.
23. Describe each of the Campaigns available in Saviynt?
Ans:
User Manager: The capacity to provide license and examine the gain of access by the Line Managers is done by the user manager campaign.
Service Account: This Campaign is used when there is a need to provide Generic Account protectors' capacity to evaluate and accrediting the gain of access to the designated Generic Accounts. These profiles could be service accounts depending on the qualification.
Entitlement Owner: This Campaign permits the Entitlement Owners to access and accredit the titles.
Role Owner: This Campaign allows the Role Owners to examine and license the tasks.
24. Describe some of the primary duties of Saviynt?
Ans:
- Accessibility selections are made keeping the risks in mind through the identification lifecycle.
- Streamlining of solution profile monitoring is done with ease.
- Dependency on IT procedures is reduced by equipping the individuals and admins with self-service attributes.
- There is good exposure, management, and control of data in Saviynt.
- Identity Bot an integrated RPA engine that allows automation of provisioning jobs.
25. What are Orphan Accounts?
Ans: The accounts that do not have any individual link with the profile but are active consumer profiles in the identification database is called orphan account.
26. What is Saviynt's Cloud PAM?
Ans: To provide secure, privileged, and sensitive access to business-critical hybrid applications and multi-cloud workloads, Saviynt offers a cloud-architected and cloud-delivered solution known as PAM (Privileged Access Management). The PAM provides automated discovery of multi-cloud workloads, helps reduce the attack surface, provides complete auditability of just-in-time (JIT), enforces compliance controls and persistent accounts.
Conclusion
With this, you might have understood the type of questions asked in the Saviynt interview. So face your fear and attend the interview. We might add more questions to this blog. I hope this helped you prepare for the most frequently asked questions.
 On-Job Support Service
On-Job Support Service
Online Work Support for your on-job roles.

Our work-support plans provide precise options as per your project tasks. Whether you are a newbie or an experienced professional seeking assistance in completing project tasks, we are here with the following plans to meet your custom needs:
- Pay Per Hour
- Pay Per Week
- Monthly
| Name | Dates | |
|---|---|---|
| Saviynt Training | May 26 to Jun 10 | View Details |
| Saviynt Training | May 30 to Jun 14 | View Details |
| Saviynt Training | Jun 02 to Jun 17 | View Details |
| Saviynt Training | Jun 06 to Jun 21 | View Details |

Madhuri is a Senior Content Creator at MindMajix. She has written about a range of different topics on various technologies, which include, Splunk, Tensorflow, Selenium, and CEH. She spends most of her time researching on technology, and startups. Connect with her via LinkedIn and Twitter .




